A newly uncovered malware campaign is leveraging fake Proton VPN websites, alongside gaming mods and utility tools, to distribute a Windows infostealer known as NWHStealer.
According to Malwarebytes, which documented the activity, attackers rely on a mix of deceptive websites, open platforms like GitHub and SourceForge, and even YouTube videos, some of which are AI-generated, to funnel victims toward malicious downloads.
Malwarebytes
NWHStealer is designed to harvest sensitive data, including browser-stored credentials, autofill data, and cryptocurrency wallet information. The malware can execute directly in memory or inject itself into legitimate processes such as RegAsm.exe, making detection more difficult. It also targets more than 25 wallet-related directories and registry keys while extracting data from browsers such as Chrome, Edge, Firefox, Opera, Brave, and others.
Malwarebytes identified two primary infection scenarios. In one case, a free web hosting platform, onworks[.]net was found hosting malicious ZIP archives disguised as legitimate utilities such as HardwareVisualizer, Sidebar Diagnostics, and OhmGraphite. These archives contain executables embedded with obfuscated loader code that performs environment checks, decrypts payloads using AES-CBC via Windows BCrypt APIs, and ultimately deploys the stealer.
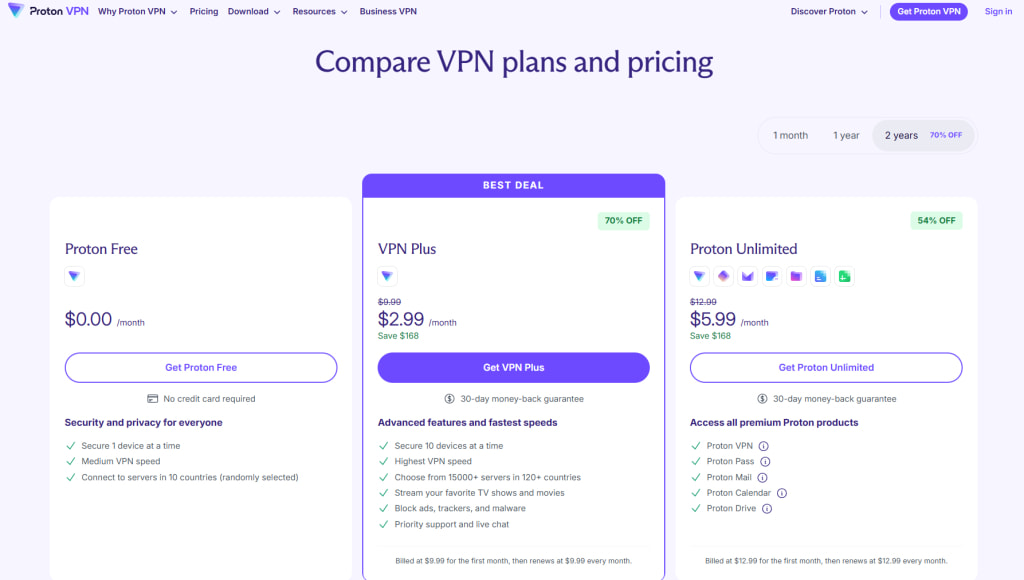
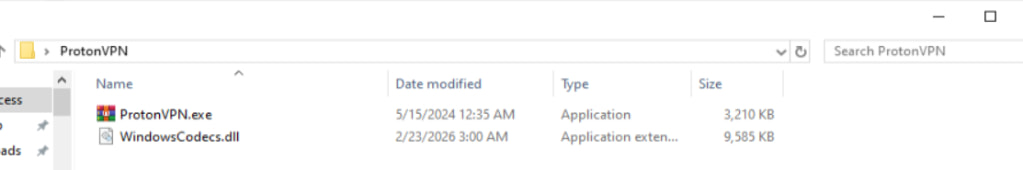
A second distribution method involves fake Proton VPN websites that deliver trojanized installers via ZIP files. These samples often rely on DLL hijacking, in which a legitimate executable, often a repackaged WinRAR binary, is paired with a malicious DLL. Once executed, the DLL decrypts an embedded payload and initiates process hollowing using low-level Windows APIs.
Malwarebytes
The infection chain continues by injecting code into active browser processes to extract decrypted data, and then exfiltrating it to a command-and-control (C2) server using AES-CBC encryption. The malware establishes persistence by creating scheduled tasks, adding Windows Defender exclusions, and deploying payloads masquerading as legitimate system processes such as svchost.exe or RuntimeBroker.exe. If the primary C2 server is unavailable, NWHStealer can retrieve fallback infrastructure via a Telegram-based dead drop.
The malware abuses the Windows cmstp.exe utility to bypass User Account Control (UAC), generating a temporary .inf file and programmatically approving the elevation prompt using Windows APIs. This allows it to execute PowerShell commands with elevated privileges without user awareness.
Despite the prominence of Proton VPN lures, Malwarebytes also observed the same payloads distributed via mining software, cheat tools like Xeno, and various hardware utilities.
To reduce exposure to these threats, users should avoid downloading software from unofficial sources or links in YouTube descriptions, even if they appear legitimate. Verifying file signatures, checking publisher information, and sticking to official vendor websites remain critical safeguards.







Leave a Reply