
Researchers have uncovered at least 72 additional malicious extensions on the Open VSX marketplace linked to the ongoing GlassWorm malware campaign.
The latest activity shows the threat actor shifting tactics by abusing extension dependency features to distribute malware indirectly through seemingly benign packages.
The findings were reported by the Socket Research Team over the weekend, which has been tracking the campaign’s continued activity since late January. While earlier GlassWorm variants embedded the malware loader directly into malicious extensions, the new wave increasingly relies on transitive installation mechanisms that allow attackers to hide the malicious component behind a separate extension.
Open VSX is an open-source extension registry used by VS Code–compatible editors such as VSCodium, Eclipse Theia, and other development environments. Extensions from the marketplace add functionality ranging from syntax highlighting and linters to developer productivity tools, making the ecosystem an attractive target for supply-chain attacks targeting developer workstations.
The campaign now abuses two legitimate extension manifest fields, extensionPack and extensionDependencies, which automatically install related extensions alongside the main package. Attackers publish extensions that initially appear harmless and contain no obvious malicious code. In later updates, the extension’s manifest is modified to reference a separate GlassWorm-linked extension, causing the editor to install it automatically.
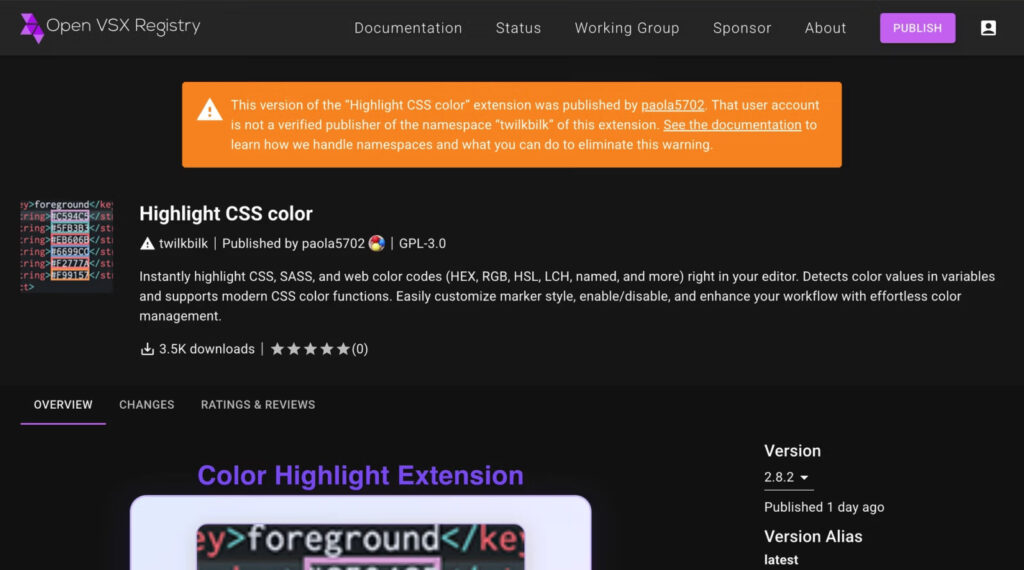
Researchers confirmed this behavior in multiple packages, including otoboss.autoimport-extension, which was later updated to reference other extensions tied to the campaign. Additional examples include twilkbilk.color-highlight-css, and crotoapp.vscode-xml-extension, which were still live in the registry during parts of the investigation.
This approach allows threat actors to distribute malware without placing the malicious loader directly inside the extension users install. Instead, the loader is delivered indirectly through dependency relationships added in later versions, reducing the likelihood that the malicious component will be noticed during an initial review.
Many of the extensions mimic popular developer utilities, including linters, formatters, language tooling for frameworks like Angular and Flutter, and widely used productivity add-ons such as icon packages and comment helpers. In some cases, attackers used typosquatted publisher names to impersonate legitimate projects, while some listings displayed artificially inflated download counts to appear more trustworthy.
Socket
Although the delivery mechanism has evolved, the underlying GlassWorm loader remains consistent with earlier activity. The malware relies on staged JavaScript execution, heavy code obfuscation, and selective execution techniques designed to evade analysis. Once triggered, it retrieves additional code and executes it directly in memory, giving attackers access to data stored on the developer’s system.
This access can expose sensitive assets commonly present on development machines, including API tokens, credentials, environment variables, configuration files, and project secrets.
Open VSX has removed many of the identified extensions since the report was published, but researchers say the takedown process is ongoing, and some malicious packages were still available during the investigation.
Because malicious dependency relationships may be added after an extension has already earned user trust, the researchers warn that reviewing an extension only at installation time is no longer sufficient. Security teams should instead analyze extension version histories and manifest changes to identify newly introduced dependencies that could pull in malicious packages.







Leave a Reply