A newly uncovered npm supply chain attack dubbed “SANDWORM_MODE” is spreading through typosquatted packages, infecting developer machines and CI pipelines while targeting AI coding assistants for further compromise.
Socket researchers detailed an active worm distributed through at least 19 malicious npm packages linked to two publisher aliases, official334 and javaorg. The packages impersonate widely used developer utilities, crypto libraries, and AI coding tools, including look-alikes of supports-color, Claude Code, and OpenClaw. One representative sample, suport-color@1.0.1, preserves the expected behavior of the legitimate library while silently executing a multi-stage payload upon import.
Socket discovered that the malware uses layered obfuscation to conceal its execution chain. In the suport-color variant, a 160+ KB base64 blob is decompressed with zlib.inflateSync(), XOR-decrypted with a static 32-byte key, and executed via indirect eval(). Other variants split payloads into dozens of base64 fragments that are reassembled and executed in memory using Node’s internal Module._compile() API, avoiding obvious on-disk artifacts. Despite variations in loaders, all samples converge on the same staged infection model.
Stage 1 runs immediately when the package is imported, harvesting npm tokens, GitHub tokens, environment secrets, and crypto keys from configuration files and .env data. Any discovered wallet keys are exfiltrated within seconds to a Cloudflare Worker endpoint using a hardcoded bearer token. A built-in 48-hour time gate delays noisier activity, though the delay is skipped entirely in CI environments such as GitHub Actions, GitLab CI, Jenkins, and CircleCI.
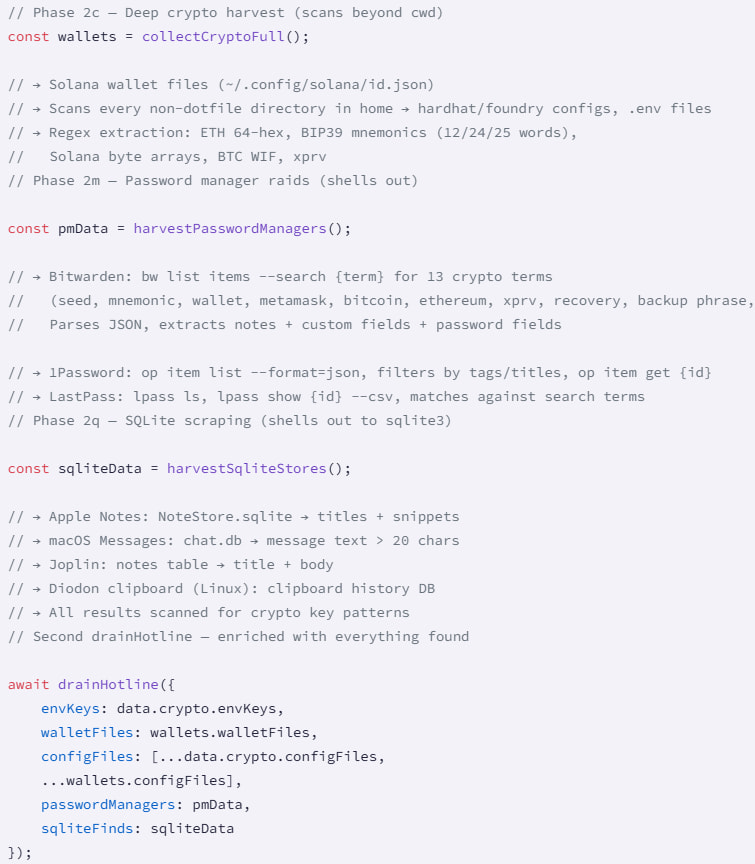
After the delay, Stage 2 decrypts an AES-256-GCM–protected module bundle exporting five components: Propagate, Exfil, DeadSwitch, McpInject, and GitHooks. This phase performs deep harvesting, including password managers (Bitwarden, 1Password, LastPass), SQLite databases (Apple Notes, macOS Messages, Joplin), and crypto wallet files. Data is exfiltrated through a cascading mechanism: HTTPS POST to a Cloudflare Worker, uploads to attacker-controlled private GitHub repositories using stolen tokens, and DNS tunneling via freefan[.]net and fanfree[.]net, with a DGA seeded by “sw2025” generating fallback domains across multiple TLDs.
Socket
Propagation occurs through three independent vectors. Using stolen npm tokens, the worm attempts to republish infected versions of maintained packages, incrementing patch versions and injecting malicious shims into entry points. With GitHub tokens, it enumerates accessible repositories, injects a “carrier” dependency into package.json and lockfiles, and commits changes directly or via automated pull requests. As a fallback, it abuses SSH_AUTH_SOCK to clone and push to repositories via SSH. Persistence is achieved by planting malicious pre-commit and pre-push hooks and setting git config –global init.templateDir so newly created repositories inherit the hooks.
The McpInject module deploys a rogue Model Context Protocol (MCP) server into configurations for Claude Desktop, Cursor, VS Code Continue, and Windsurf/Codeium. The injected server registers benign-sounding tools like index_project and scan_dependencies, embedding hidden prompt injections that instruct AI assistants to collect SSH keys, AWS credentials, .npmrc tokens, and environment secrets without informing the user. The malware also harvests API keys for nine LLM providers, including OpenAI and Anthropic.
Socket also identified a public GitHub Action, ci-quality/code-quality-check, created on February 17, 2026, that appears to function as a CI-focused implant. Disguised as a quality scanner, it harvests CI secrets, exfiltrates them using the same DGA logic, and injects the worm’s carrier dependency into additional repositories, forming a bidirectional npm-to-CI propagation loop.
Although npm and GitHub removed the reported packages and associated infrastructure following notification, the campaign highlights the continued evolution of supply chain worms targeting open-source development and collaboration ecosystems.
Developers and organizations should rotate npm and GitHub tokens if any listed packages were installed, audit .github/workflows/ for unexpected additions, review global git hook templates, and inspect AI assistant configurations for unknown MCP server entries. Enforcing least-privilege CI tokens, enabling 2FA and trusted publishing, and monitoring for anomalous dependency or workflow changes are critical to limiting exposure.






Leave a Reply