Amtrak is the latest organization to have a major dataset added to the Have I Been Pwned (HIBP) database, following claims by the ShinyHunters hacking group that it breached the US passenger rail service and exfiltrated millions of customer records.
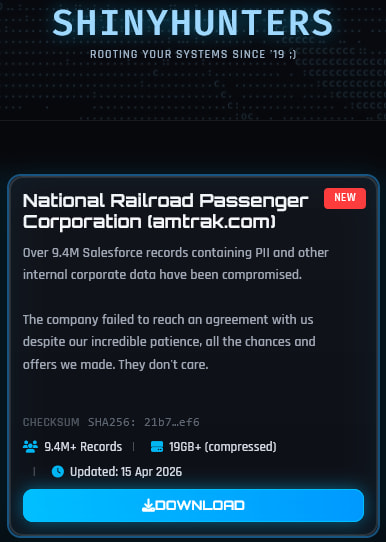
The development comes days after ShinyHunters publicly alleged they had compromised Amtrak’s systems, stating that “over 9.4 million Salesforce records containing PII and other internal corporate data” had been obtained. The group, known for targeting Salesforce instances and attempting to extort the company before releasing stolen data, claimed negotiations with the company failed, prompting the publication of the dataset.
HIBP operator Troy Hunt subsequently downloaded and analyzed the leaked data, adding it to the breach notification service today. According to the HIBP entry, the dataset contains approximately 2.1 million unique email addresses, along with associated names, physical addresses, and customer support ticket records. It should be noted that, while the data appears legitimate based on multiple validation methods, inclusion in HIBP does not constitute official confirmation from the affected organization.
Amtrak, formally known as the National Railroad Passenger Corporation, is the primary provider of intercity passenger rail service in the United States, serving more than 30 million customers annually across a nationwide network. The company operates a mix of long-distance, regional, and high-speed rail services, making it a significant holder of customer travel and support data.
The discrepancy between the 9.4 million records claimed by ShinyHunters and the 2.1 million unique email addresses identified by HIBP likely reflects duplicate entries or multiple records tied to the same individuals within the dataset, a common pattern in Salesforce-related leaks. HIBP also reported that approximately 80% of the exposed data had already appeared in previous breaches.
ShinyHunters has built a reputation for breaching cloud-based CRM platforms, particularly Salesforce, often leveraging misconfigurations, stolen credentials, or third-party integrations to gain access. Once inside, the group typically exfiltrates customer databases and internal records before initiating ransom negotiations. If those talks fail, the data is released on underground forums or public leak sites.
At the time of writing, Amtrak has not issued any public statement acknowledging the breach or confirming the authenticity of the leaked data.
The exposed data could be used in targeted phishing or social engineering campaigns. Users should remain cautious about unsolicited communications that reference travel details or customer support interactions, and avoid clicking links or downloading attachments from unknown sources.







Leave a Reply