AdGuard has released AdGuard Home v0.107.73 to patch a critical vulnerability that could allow unauthenticated attackers to bypass authentication and gain full administrative access to the service.
The flaw, tracked as CVE-2026-32136, carries a CVSS score of 9.8 and affects earlier versions of the popular network-wide ad-blocking software.
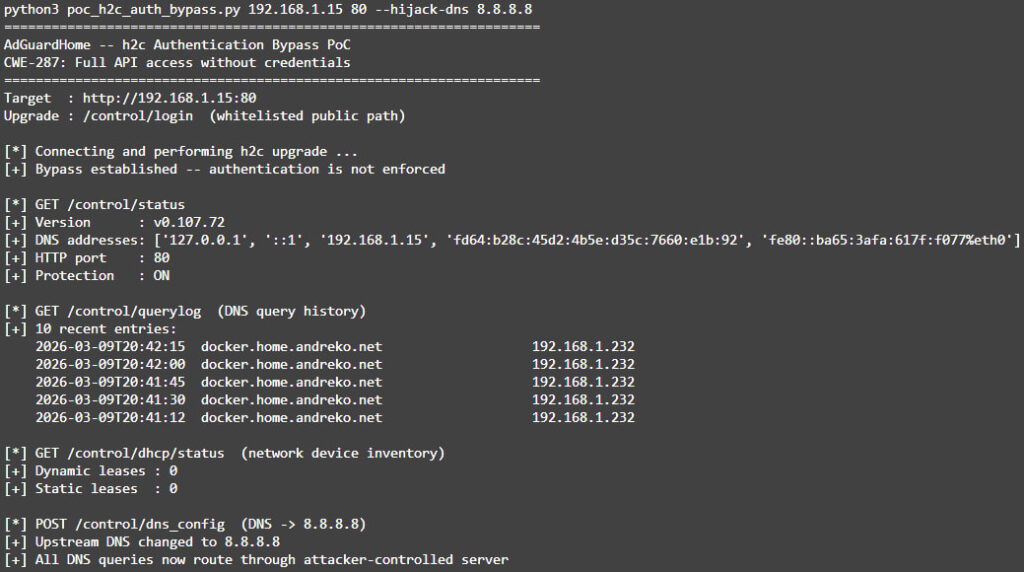
The vulnerability was reported by security researcher @mandreko, who discovered the issue while reviewing AdGuard Home’s codebase. According to the researcher’s technical write-up, the flaw stems from how the application handled HTTP/2 Cleartext (h2c) upgrade requests, which inadvertently allowed attackers to bypass the authentication middleware protecting the administrative API.
AdGuard Home is a self-hosted DNS filtering platform designed to block ads, trackers, and malicious domains across entire networks. It is widely deployed on home routers, Raspberry Pi devices, and small virtual machines, where it intercepts DNS traffic from all devices on the network. The software also provides a web-based management interface that allows administrators to configure DNS filtering rules, view query logs, and manage DHCP leases.
The issue originates in the service’s HTTP server initialization logic. Authentication checks were applied as a wrapper around the HTTP handler, which normally ensures that API requests require valid credentials. However, the application also supported h2c, an unencrypted form of HTTP/2 defined in RFC 7540 that allows an HTTP/1.1 connection to upgrade to HTTP/2 using a special request header.
When such an upgrade request was sent to a public endpoint, such as /control/login, the authentication middleware permitted it because the path was whitelisted. The h2c handler then hijacked the underlying TCP connection and passed it to an HTTP/2 server that relied on an internal handler lacking authentication checks. As a result, once the upgrade was completed, all subsequent HTTP/2 requests on that connection were processed as fully authenticated, even if no credentials had been supplied.
A proof-of-concept exploit demonstrated that an attacker could connect to the AdGuard Home service, trigger the h2c upgrade, and immediately interact with administrative API endpoints. This allowed attackers to retrieve sensitive data such as DNS query logs and DHCP device inventories, which may reveal browsing activity and detailed network device information.
mattandreko.com
Moreover, attackers can modify configuration settings, including:
- Changing upstream DNS servers to attacker-controlled infrastructure
- Disabling DNS filtering and protection features
- Altering filtering rules or DNS rewrites
- Resetting the administrator password and locking out legitimate users
Such a level of access allows attackers to redirect all DNS traffic on a network, enabling phishing attacks or traffic interception across every connected device.
AdGuard addressed the vulnerability in version 0.107.73 by moving the authentication middleware inside the handler used by the h2c server, ensuring that authentication checks apply to all HTTP/2 requests after an upgrade occurs. Alternatively, administrators can reduce exposure by disabling h2c support entirely if it is not required.
The vulnerability was discovered on March 8, 2026, reported to the AdGuard security team the following day, and patched in a coordinated release on March 10.
AdGuard strongly recommends that all users upgrade to v0.107.73 immediately. Administrators should also ensure that the AdGuard Home web interface is not exposed to the internet and is accessible only from trusted networks. Additional protections, such as reverse proxies, authentication layers, or firewall restrictions, can further reduce the risk of unauthorized access.







Leave a Reply