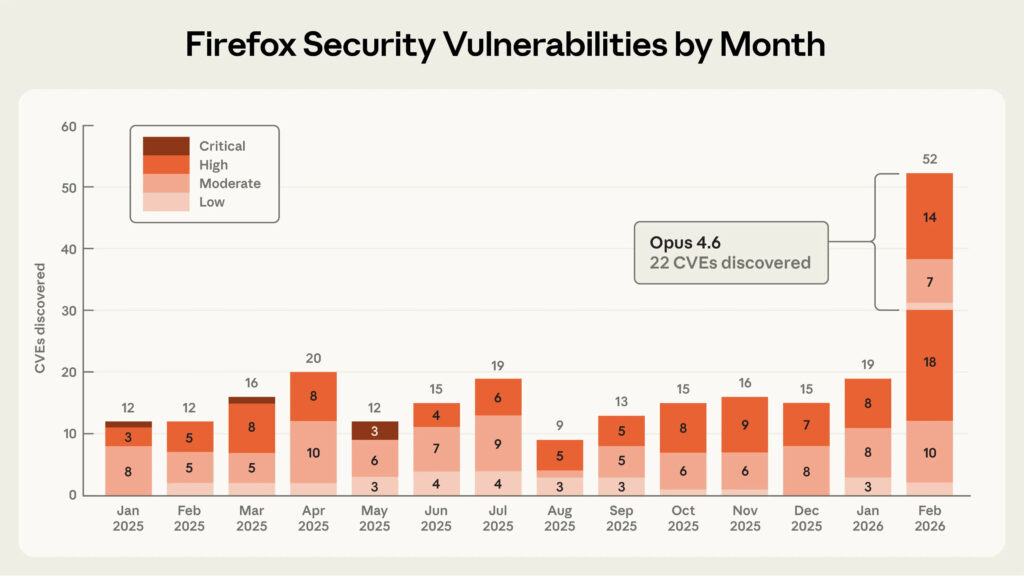
Anthropic says its Claude Opus 4.6 AI model discovered 22 previously unknown vulnerabilities in Mozilla Firefox during a two-week collaboration with Mozilla researchers.
Anthropic researchers used Claude Opus 4.6 to analyze Firefox’s codebase and identify security flaws, and submitted the results to Mozilla via its Bugzilla vulnerability reporting system.
The AI-assisted research resulted in 112 vulnerability reports, including 22 issues later assigned CVE identifiers by Mozilla. Most of the bugs were fixed in the recently released Firefox 148.
Anthropic said the research began in late 2025 after internal evaluations showed that Claude Opus 4.5 could solve nearly all tasks in CyberGym, a benchmark used to test whether language models can reproduce known security vulnerabilities. To test more realistic scenarios, researchers constructed a dataset of historical Firefox CVEs and asked Claude Opus 4.6 to reproduce them.
While the model successfully rediscovered many historical bugs, researchers were concerned that some of the vulnerabilities might have appeared in the model’s training data. To eliminate that possibility, the team tasked Claude with identifying entirely new vulnerabilities in the current Firefox codebase.
The AI initially focused on the browser’s JavaScript engine, one of the most security-critical components because it executes untrusted code from websites. Within about 20 minutes of exploration, Claude reported a use-after-free memory vulnerability, a type of bug that can allow attackers to overwrite memory with malicious data. Researchers validated the flaw in a virtual machine running the latest Firefox release before submitting it to Mozilla, along with a proposed patch generated by the model.
While the first vulnerability was being validated, Claude had already generated roughly 50 additional unique crashing test cases. Over the course of the project, the AI scanned nearly 6,000 C++ source files and produced hundreds of test inputs that triggered potential flaws.
Mozilla engineers later encouraged Anthropic researchers to submit their findings in bulk, even when individual crashes had not yet been fully validated, allowing the Firefox security team to triage the reports internally.
The resulting vulnerabilities span multiple browser components, many of which affect the JavaScript engine, DOM implementation, WebAssembly, audio/video subsystems, and IndexedDB storage. Several of the high-severity flaws involve use-after-free memory errors, while others involve integer overflows, boundary condition errors, or sandbox escape vulnerabilities. All of them were fixed in Firefox 148.
Anthropic also tested whether the AI could automatically exploit the vulnerabilities it discovered. In hundreds of attempts costing roughly $4,000 in API credits, Claude successfully created functioning proof-of-concept exploits in only two cases, and even those worked only in a controlled testing environment where some browser defenses, such as the sandbox, were intentionally disabled.
The results suggest that current AI models are significantly better at finding vulnerabilities than turning them into working exploits. However, Anthropic noted that the ability to automatically generate even crude exploits demonstrates the need to accelerate defensive security work before such capabilities improve.
Anthropic says it plans to expand its work with open-source maintainers and has already used Claude to search for vulnerabilities in other projects, including the Linux kernel.







Firefox is trash now.
An open-source browser having fewer extensions than Chrome makes no sense, especially when Chrome’s extension approval process is stricter, slower, and costs developers more time and money. The fact that Firefox still can’t attract developers shows how little real usage it has.
Nobody wants to talk about the elephant in the room. The only people making noise about Firefox are a tiny group of loud, defensive users who pretend it’s still relevant. They ignore the browser’s issues, the limitations, the higher hard‑drive writes, the profile corruption problems, the memory fragmentation, and all the other things most users never notice until something breaks. The fanboys glaze over Mozilla’s failures and act like pointing out problems is some kind of attack on “open source.”
Meanwhile, the actual situation is getting worse. Claude AI found 22 Firefox vulnerabilities in two weeks of testing across the JavaScript engine, DOM, WebAssembly, audio/video components, and IndexedDB. That’s not a small number. That’s a sign of deep structural problems in the codebase.
The extension ecosystem is shrinking. Developer interest is down. User share keeps dropping. Mozilla keeps cutting teams and trying to pivot into unrelated products. None of that looks like a healthy browser project.
This site calls itself unbiased. If that’s true, it should acknowledge Firefox’s real issues and the current mindset of its user base instead of ignoring them and letting a handful of loud defenders create the illusion that Firefox is still widely used or technically competitive. Cyberinsider blogs should reflect this fact.
Respectfully, I disagree. Firefox is anything but trash.
1. Firefox has problems (e.g. heavy memory use, constant communications with unknown servers) but they are easily remedied. I have been using it for years and it is highly stable. Things don’t break. I have never seen problems with hard-drive writes, memory fragmentation or profile corruption.
2. Firefox’s being open source is an advantage, not a liability. Developments are vigorous and updates are frequent. Firefox has a large and highly active developer community fixing problems and advancing features. This is a leading-edge browser.
3. A browser’s value is not determined by the number of extensions it supports. For its part, Firefox has plenty including highly useful and powerful ones. However, it is true Firefox should be stricter in approving extensions.
4. The 22 vulnerabilities Claude found are easily within reason for a web browser of this class. The fact Mozilla collaborated with Anthropic on this proves Mozilla takes security seriously and solicits audits. How many vulnerabilities would Claude find in other leading browsers ?
5. I am not sure developer and user interests in Firefox are shrinking. As noted, Firefox has quite a developer community. The user share seems to be holding its own.
6. Comparing Firefox to Chrome is preposterous as regards privacy (not necessarily other aspects).
Firefox is built around privacy in every way. It offers many strong privacy features, gives users control over them, supports a large number of powerful, diverse privacy extensions and allows any user to tweak advanced privacy / security settings via about:config (behind-the-scenes developer interface). When properly configured and extension-bolstered, Firefox is nearly “bombproof”. Add a trustworthy VPN and safe browsing habits, and your security is beyond sound. Confirmed with tools like Panopticlick.
Chrome is made by Google, the world’s largest espionage agency masquarading as a tech. company. No privacy-conscious user would ever consider using it. Like all things Google – the product is attractive, useful, user-friendly and offers many features & advantages. But for these you pay with your privacy. Chrome’s spying on its users is well-established.
So Firefox is not perfect but it is a solid, trustworthy, leading-edge choice for users demanding privacy.