
Attackers exploited 90 zero-day vulnerabilities in the wild in 2025, with commercial spyware vendors responsible for the largest share of attributed exploitation.
The findings come from Google, which examined vulnerabilities that were exploited before vendors released patches.
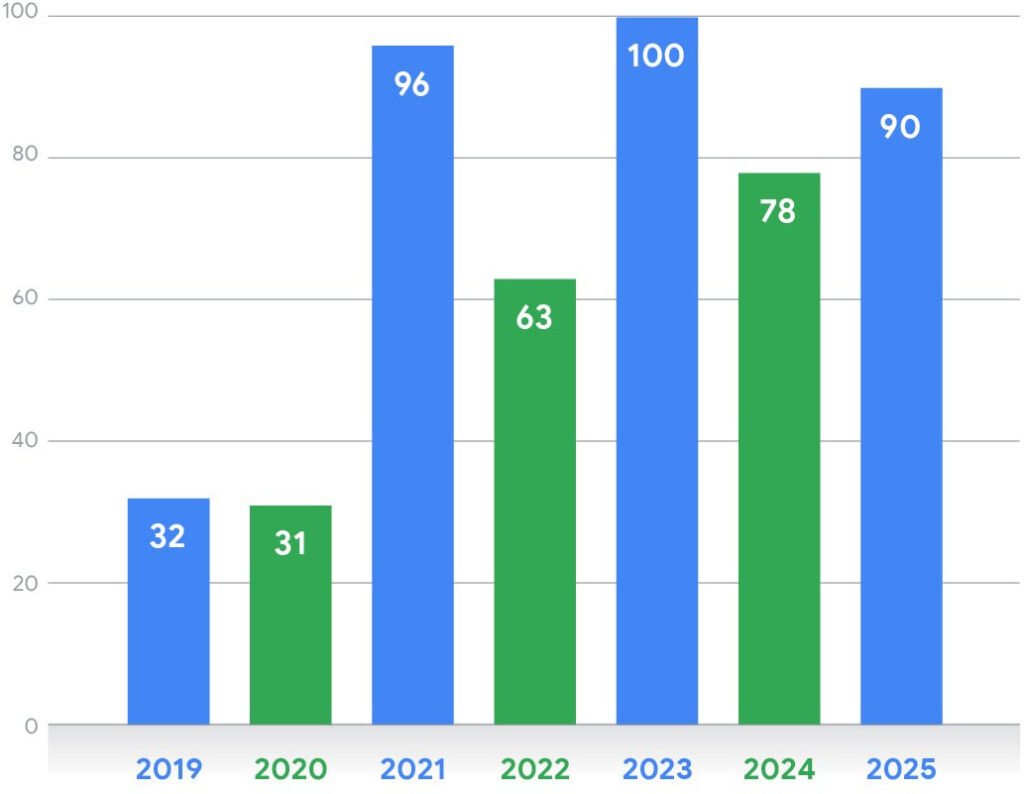
GTIG tracked 90 zero-days disclosed in 2025, a figure slightly below the record 100 observed in 2023 but higher than 78 in 2024, indicating that annual exploitation levels have stabilized at elevated levels since 2021.
Spyware vendors drive most exploitation
For the first time since Google began monitoring the space, commercial surveillance vendors (CSVs), companies that develop spyware and exploit tools for government clients, were linked to more zero-day exploitation than traditional state-sponsored hacking groups.
These vendors build exploit chains capable of compromising mobile devices and computers, often selling access to government customers. Google warns that the growing spyware industry is expanding access to zero-day capabilities beyond elite intelligence agencies.
Companies such as Intellexa continue to adapt their spyware platforms and exploit chains to bypass newer mobile security protections.
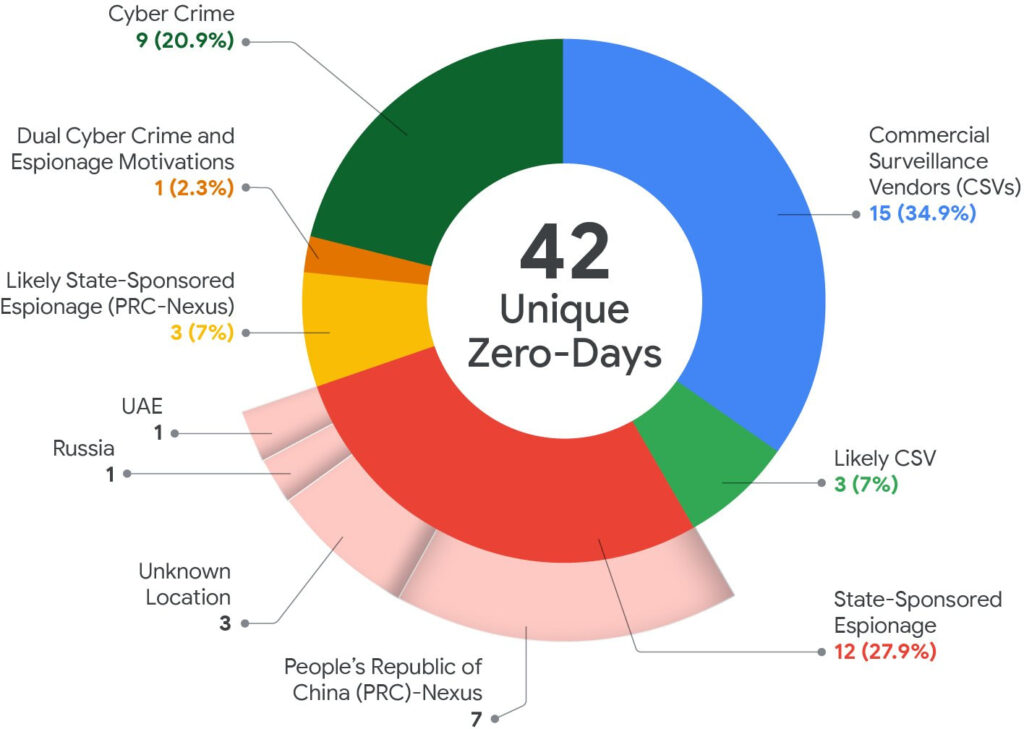
Chinese threat groups are the most prolific
Among nation-state actors, China-linked cyber-espionage groups remained the most prolific users of zero-days.
Google attributed at least 10 exploited vulnerabilities in 2025 to Chinese groups such as UNC5221 and UNC3886, which frequently targeted network security appliances and edge infrastructure to gain persistent access to corporate networks.
In contrast, no zero-day exploitation was attributed to North Korean groups in 2025, a notable shift from the five vulnerabilities linked to them in 2024.
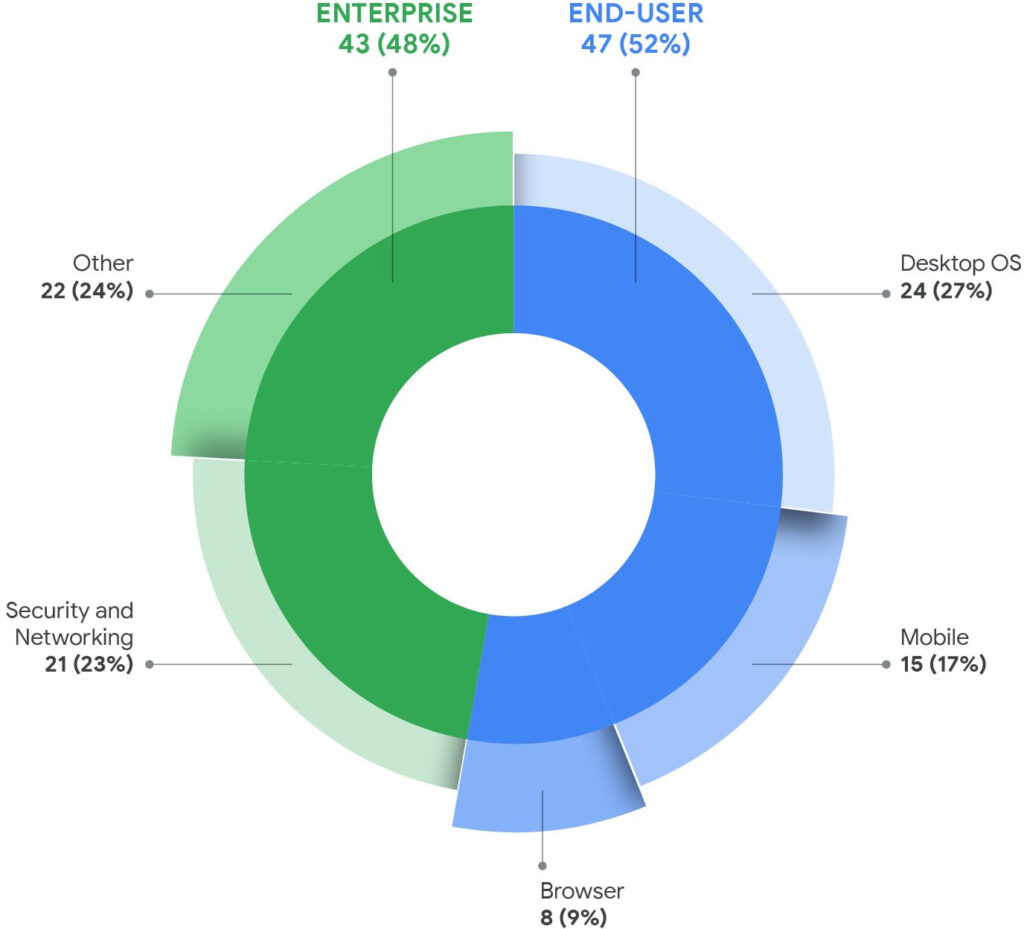
In 2025, 43 zero-days (48%) affected enterprise products, the highest share recorded. Many targeted security appliances and networking devices from vendors, including Cisco, Fortinet, Ivanti, and VMware, which often provide privileged access within corporate environments.
Because these edge systems rarely run endpoint detection tools, attackers can maintain access while remaining difficult to detect.
Operating systems lead zero-day targets
Across end-user platforms, operating systems accounted for 39 zero-days (44%), making them the most exploited category. Mobile OS vulnerabilities also increased, rising to 15 in 2025 from nine the previous year.
Meanwhile, browser-based exploitation fell below 10% of observed zero-days, suggesting that browser hardening measures are making attacks more difficult.
Financially motivated groups were linked to nine zero-days in 2025, including attacks tied to CL0P-linked extortion campaigns exploiting Oracle E-Business Suite vulnerabilities before patches were released.
Looking ahead, Google warns that AI could accelerate both vulnerability discovery and exploit development, potentially shortening the time between vulnerability discovery and real-world attacks.
Google recommends organizations adopt defense-in-depth strategies, including network segmentation, asset inventory management, and behavioral monitoring, while individuals should enable advanced security protections and install updates promptly.







So the Blue and Light Green colors are softly & generically listed as CSVs but should be proper labeled USA Sponsored Espionage
I mean that is quite literally what Google and BigTech are, how convenient to leave the USA off the chart lol
Be careful of spin folks, this pie chart is Goolge spin on a platter
“These vendors build exploit chains capable of compromising mobile devices and computers, often selling access to government customers. Google warns that the growing spyware industry is expanding access to zero-day capabilities beyond elite intelligence agencies.”