
Private Internet Access (PIA) says it received 30 legal data requests in the fourth quarter of 2025, yet once again produced no user data in response.
At the same time, the VPN provider completed its third independent Deloitte audit, which examined its no-logs architecture and server configuration under the ISAE 3000 assurance standard.
In its Q4 2025 Transparency Report, PIA details the volume and types of legal processes it received between October and December 2025. The company’s legal team handled a mix of US and international requests, including subpoenas, warrants, civil demands, and informal foreign inquiries. None resulted in the disclosure of user information, as PIA maintains it does not log user activity.
According to the breakdown, PIA received seven subpoenas, one warrant, ten other government or civil requests, and twelve foreign or informal requests during the quarter. While subpoenas remained the most common formal legal instrument, the quarter-over-quarter increase was primarily driven by a rise in other government and civil demands, as well as foreign and informal inquiries. Despite the broader mix, PIA reports that it produced zero logs in all cases.
Private Internet Access is a US-based VPN provider headquartered in Colorado. The company operates a global VPN network that provides encrypted tunnels via protocols such as WireGuard and OpenVPN and offers features including dedicated IP addresses, DNS protection, and multi-platform clients for Windows, macOS, Linux, iOS, and Android.
Audit validates no-logs promise
The latest audit was conducted by Deloitte and completed on December 19, 2025, under the International Standard on Assurance Engagements (ISAE) 3000 (Revised).
Deloitte’s procedures included interviews with responsible PIA personnel, inspection of VPN and distribution servers, and review of configuration, access control, change management, and incident management processes. The auditors also verified that logging controls were implemented as described in PIA’s internal documentation. Deloitte stated that nothing came to its attention, suggesting that PIA’s system configuration and operational management were not prepared, in all material respects, in accordance with the company’s no-logging description.
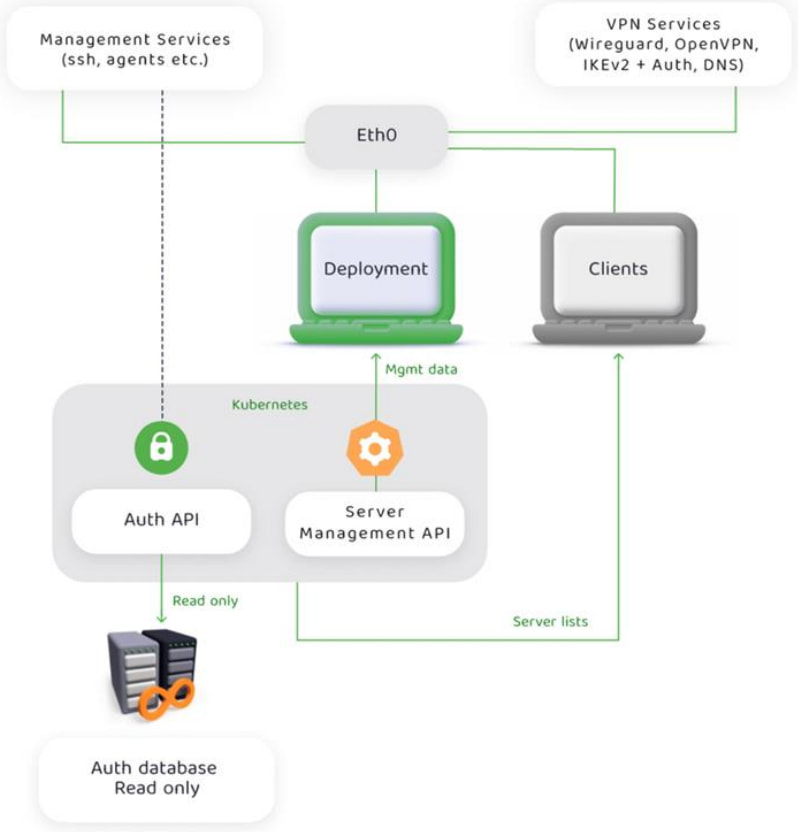
The audit report provides technical detail about how PIA enforces its no-logs policy. All VPN services run in ephemeral containers without persistent disk storage, and logging is disabled at both the container and service levels, with output redirected to /dev/null. VPN servers use RAM disks with full-disk encryption, meaning data is wiped on power loss. The architecture is designed so that even if a server were seized or compromised, it would not contain historical user activity data.
PIA
The report also examines PIA’s token-based Dedicated IP (DIP) system. Authentication to the DIP service uses tokens that cannot be associated with user identities on the server side, are stored only on the client, and cannot be linked to a specific purchase in a way that ties them to a user. If a token is lost, PIA states it cannot be recovered, an intentional design decision aimed at preventing backend traceability.
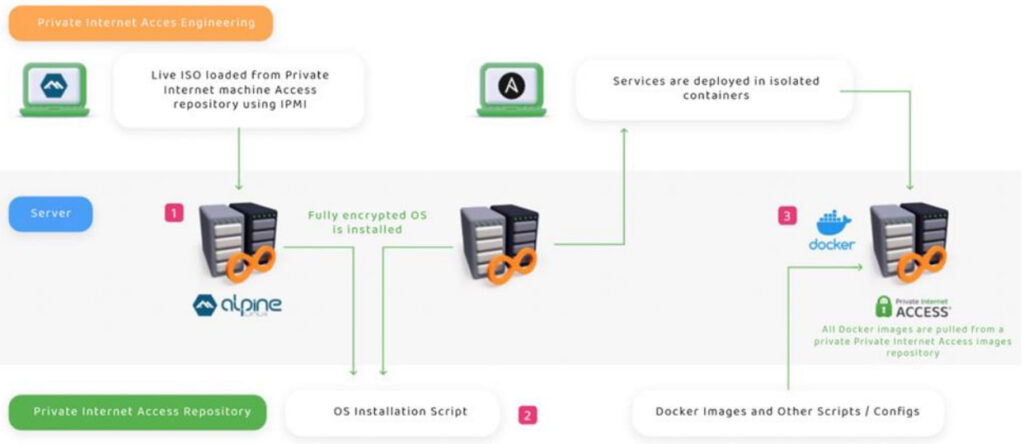
In addition to server-side controls, Deloitte reviewed PIA’s deployment and release management processes. VPN servers are provisioned using a standardized Linux image, configured with full-disk encryption, and deployed via Ansible, with logging disabled before accepting user connections. Changes to production systems require documented impact assessments, dependency mapping, stakeholder approvals, and rollback plans to reduce the risk of unauthorized modifications.
PIA
Separately, PIA reports continued activity in its bug bounty program. During Q4 2025, it received 14 submissions, 13 unique, with one confirmed security issue that was remediated. The remaining reports were classified as false positives.







Leave a Reply