
Google has released a new Chrome Stable update that fixes two high-severity security vulnerabilities, both of which the company says are already being actively exploited in the wild.
The flaws affect core browser components and are addressed in Chrome versions 146.0.7680.75/76 for Windows and macOS, and 146.0.7680.75 for Linux.
The update began rolling out on March 12, 2026, and will gradually reach users over the coming days and weeks. Google confirmed that the release resolves two vulnerabilities, CVE-2026-3909 and CVE-2026-3910, though technical details remain restricted until a larger share of users receive the patch.
According to the advisory, both vulnerabilities were reported internally by Google on March 10, 2026. Google did not disclose how the attacks were detected or whether they were uncovered through in-the-wild exploitation analysis, but the company explicitly stated that exploits for both flaws currently exist.
Chrome is the world’s most widely used web browser, with billions of users across desktop and mobile platforms. Because browsers process untrusted content from websites continuously, security flaws affecting rendering engines or JavaScript execution environments can be attractive targets for attackers seeking to compromise systems through malicious web pages.
The first vulnerability, CVE-2026-3909, is described as an out-of-bounds write in Skia, the open-source 2D graphics library used by Chrome to render images, text, and visual elements across the browser interface and web content. Out-of-bounds write bugs occur when software writes data outside the boundaries of allocated memory. In browser environments, such memory corruption issues can allow attackers to crash the browser or manipulate memory to enable arbitrary code execution.
The second flaw, CVE-2026-3910, involves an improper implementation in V8, Chrome’s high-performance JavaScript engine that executes web scripts. Implementation errors in JavaScript engines are frequently security-critical because they process complex, attacker-controlled inputs delivered via websites. Exploiting such weaknesses can allow malicious scripts to escape intended execution constraints or corrupt memory during script processing.
Although Google has not released exploit details, attacks exploiting vulnerabilities in components such as Skia or V8 are commonly triggered when a victim visits a specially crafted website or loads malicious web content.
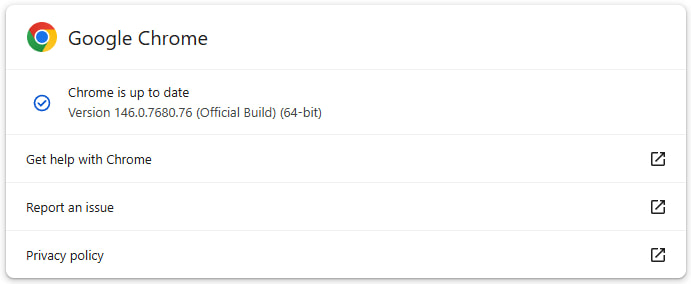
Chrome users are advised to update to the latest version as soon as it becomes available. On desktop systems, Chrome typically updates automatically, but users can manually trigger the update by navigating to Settings → About Chrome, which downloads and installs the latest release.







Great catch