
Google has disrupted a long-running global cyber espionage operation that leveraged Google Sheets as a covert command-and-control channel to target telecommunications providers and government entities across more than 70 countries.
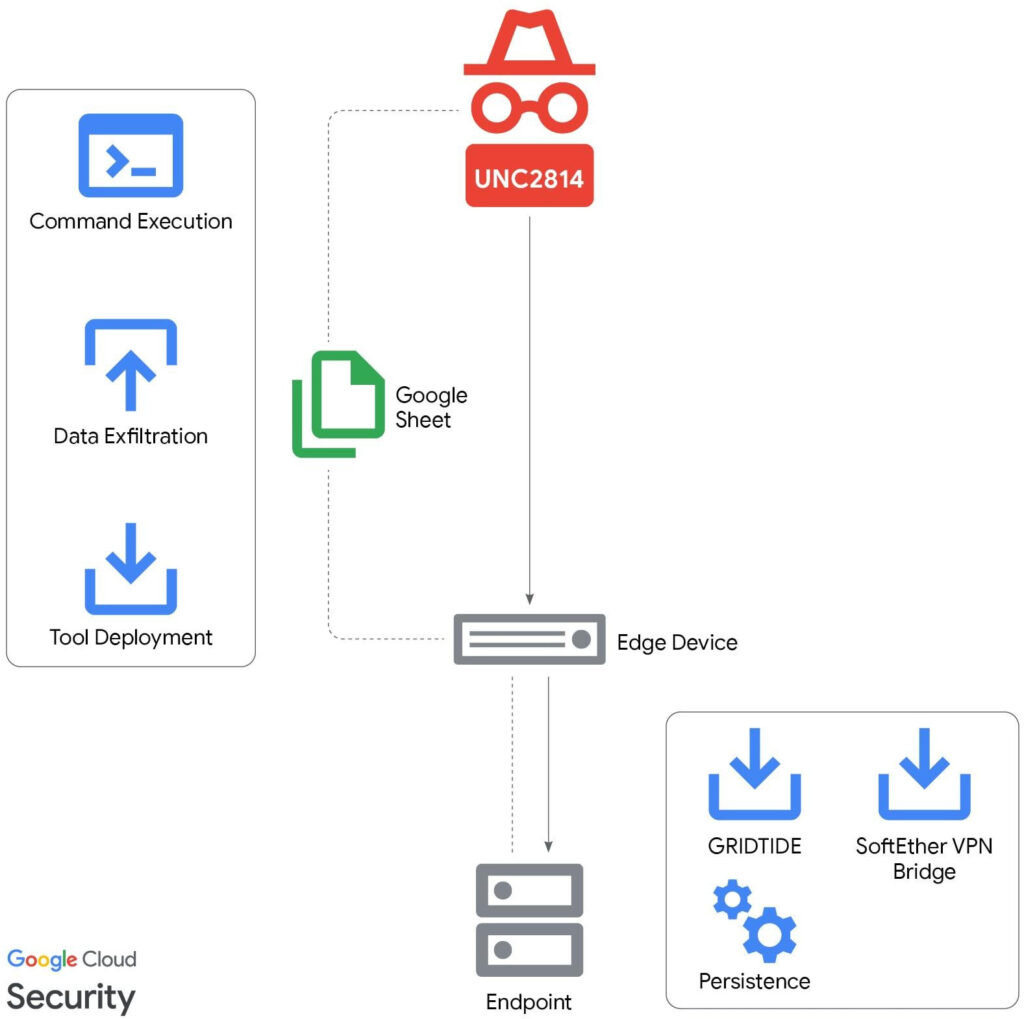
The campaign, attributed to a suspected China-linked threat actor tracked as UNC2814, relied on a newly identified backdoor, GRIDTIDE, to blend malicious traffic with legitimate cloud API activity.
The operation was uncovered and analyzed by the Google Threat Intelligence Group (GTIG) and Mandiant. As of February 18, 2026, investigators confirmed 53 victims across 42 countries spanning Africa, Asia, the Americas, and additional regions, with suspected targeting in at least 20 more nations.
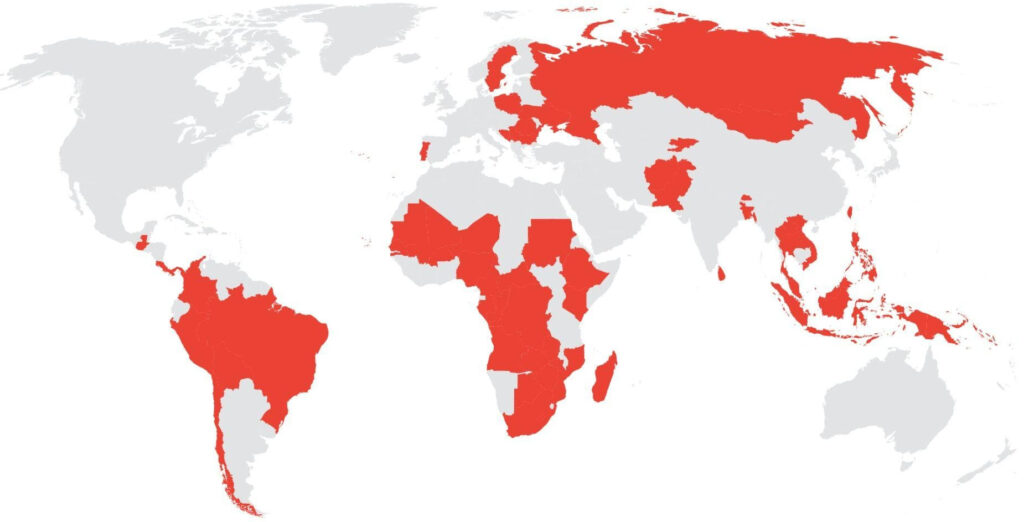
UNC2814 has primarily targeted telecommunications providers, though government entities were also compromised. Google confirmed that UNC2814’s operations have been ongoing for nearly a decade, with the scale of confirmed and suspected activity indicating sustained, resource-backed efforts.
Google emphasized that the activity is not linked to the publicly reported “Salt Typhoon” campaign and involves distinct victims and tradecraft.
Initial detection
The investigation began when Google flagged suspicious activity on a customer’s CentOS server. Analysts observed an unusual process tree in which a binary named /var/tmp/xapt spawned a root shell and executed sh -c id 2>&1, a command used to confirm elevated privileges. The output showed uid=0(root), indicating successful privilege escalation.
The file name “xapt” was likely chosen to resemble the legitimate apt package manager used in Debian-based systems.
Following confirmation of malicious behavior, Mandiant analysts notified the affected customer and began deeper forensic analysis, uncovering a broader post-compromise toolkit.
Persistence and lateral movement
After gaining access, UNC2814 used a service account to move laterally via SSH, relying heavily on living-off-the-land (LotL) techniques to avoid detection. The attackers created a malicious systemd service to ensure the malware would run automatically at system boot.
The backdoor was initially launched using nohup ./xapt, allowing it to persist after session termination. Investigators also found that the attackers deployed SoftEther VPN Bridge to establish encrypted outbound connections to external infrastructure.
In at least one case, GRIDTIDE was deployed on systems containing personally identifiable information (PII), including full names, phone numbers, dates and places of birth, voter ID numbers, and national ID numbers. While Google did not directly observe data exfiltration in this campaign, historical China-linked intrusions into telecom networks have involved the theft of call detail records and SMS data, and the abuse of lawful intercept systems for surveillance.
A spreadsheet-based backdoor
GRIDTIDE is a C-based backdoor capable of executing arbitrary shell commands and transferring files to and from infected systems. What distinguishes it is its use of Google Sheets as a command-and-control (C2) mechanism.
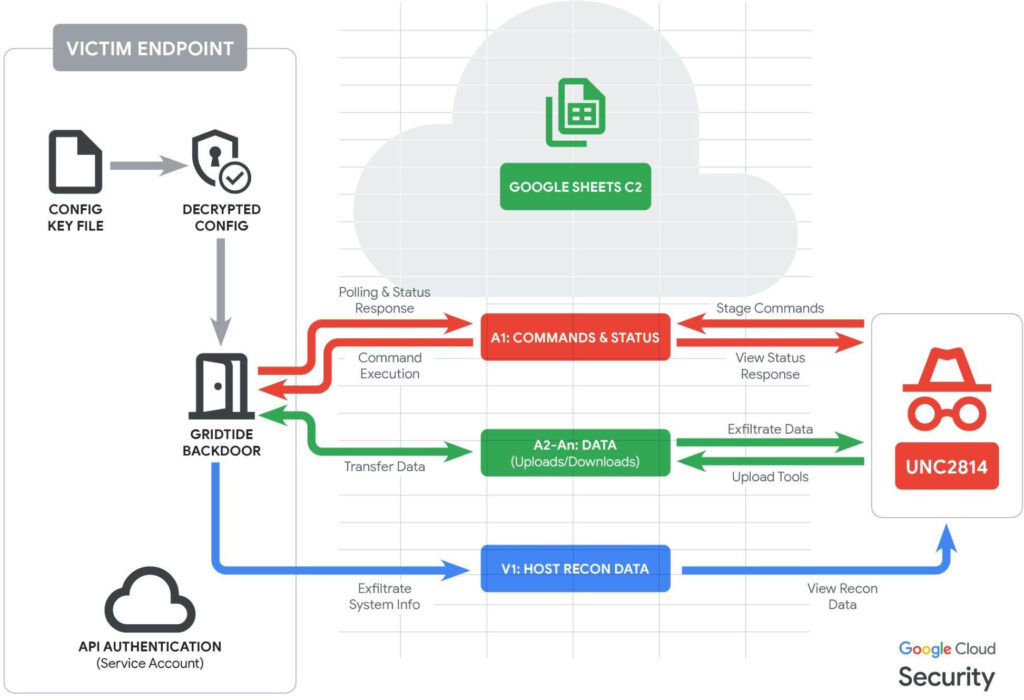
Instead of exploiting a vulnerability in Google’s products, the malware abuses legitimate Google Sheets API functionality. It authenticates using a threat actor–controlled Google service account and communicates through a spreadsheet that acts as a data exchange channel.
Before operating, GRIDTIDE expects a 16-byte cryptographic key stored locally. It uses AES-128 in CBC mode to decrypt embedded Google Drive configuration data, which includes service account credentials and the spreadsheet ID used for C2.
Once connected, the malware “sanitizes” the spreadsheet by clearing the first 1,000 rows across columns A-Z using the batchClear API method. It then fingerprints the compromised host, collecting details such as username, hostname, OS version, local IP address, working directory, language settings, and time zone. This information is encoded and written into cell V1.
Commands are issued through cell A1 using a structured syntax. Supported operations include:
- Executing Base64-encoded shell commands.
- Uploading data from spreadsheet cells to the endpoint.
- Downloading local files in 45 KB fragments back to the spreadsheet.
The malware uses a 1-second polling interval, switching to randomized 5–10-minute delays after 120 failed attempts to reduce detection noise. All communications are encoded using a URL-safe Base64 variant to evade filtering.
Disruption
Google terminated all attacker-controlled Google Cloud projects, revoked access to abused Google Sheets APIs, disabled associated accounts, and sinkholed known domains tied to UNC2814 infrastructure. The company also released indicators of compromise (IOCs) linked to infrastructure active since at least 2023 and issued formal victim notifications.
Organizations in the telecommunications and government sectors are advised to monitor for unusual use of cloud APIs, especially Google Sheets, audit service account usage, restrict API access to least-privilege principles, and inspect for unauthorized systemd services and binaries in temporary directories.
Google warns that while the disruption significantly degrades UNC2814’s current capabilities, the group is likely to attempt reestablishing its global foothold.







Leave a Reply