The US Department of Justice has dismantled the American portion of a router-hijacking operation run by Russia’s GRU Unit 26165, also known as APT28, after the group used compromised small office and home office devices to reroute internet traffic and steal credentials.
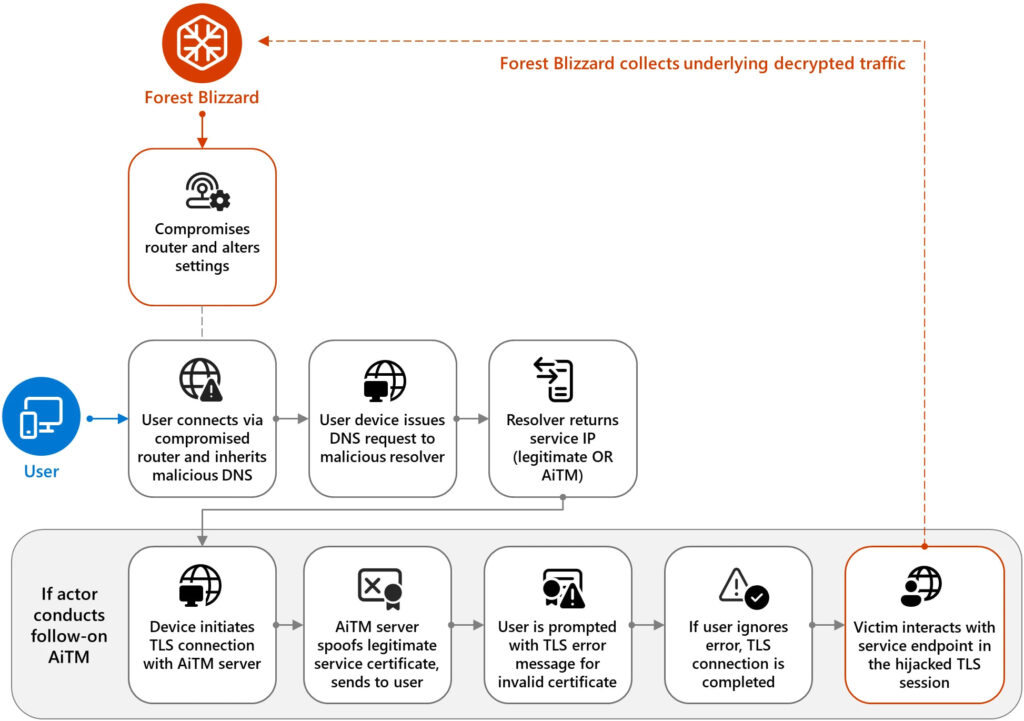
The FBI carried out the court-approved action as part of “Operation Masquerade,” targeting compromised routers across the United States. Investigators say the attackers exploited known vulnerabilities in internet-exposed TP-Link devices, altered DNS settings, and forced connected systems to use malicious resolvers under their control. This allowed the GRU to monitor DNS traffic and, for selected victims, return fraudulent DNS records that redirected authentication requests to attacker-controlled systems.
The campaign is attributed to APT28, a Russian state-backed threat actor linked to the GRU’s 85th Main Special Service Centre. The group has a long history of cyber-espionage targeting governments, defense, and critical infrastructure. In this operation, compromised routers were used to target individuals and organizations worldwide, including those in military and government sectors.
TP-Link devices were a primary target. The NCSC said attackers likely exploited flaws such as CVE-2023-50224 in models like the WR841N to extract credentials via crafted HTTP requests. With administrative access, attackers modified DHCP/DNS settings so all connected devices would inherit malicious DNS servers. The agency also listed multiple affected TP-Link models, noting the list is likely incomplete.
Lumen’s Black Lotus Labs, which tracks the activity as “FrostArmada,” observed early operations beginning in May 2025, followed by a sharp expansion in August 2025, just one day after a separate NCSC report on related tooling, indicating rapid adaptation by the threat actor.
Microsoft reported that APT28 and its sub-group Storm-2754 compromised thousands of SOHO devices, impacting over 200 organizations and at least 5,000 consumer devices. Lumen’s broader telemetry suggests a larger footprint, with more than 18,000 moderate-confidence victim IPs across 120 countries at the campaign’s peak in December 2025.
Microsoft
After compromising routers, attackers redirected DNS traffic to actor-controlled servers, often using the legitimate dnsmasq utility. Most DNS queries were resolved normally to avoid detection, but requests tied to authentication services, such as Outlook or Office 365, could be selectively redirected to adversary-in-the-middle (AitM) infrastructure. There, attackers intercepted login flows and harvested passwords, emails, and authentication tokens, sometimes by presenting spoofed services or invalid TLS certificates.
Both Microsoft and the NCSC assess the operation as opportunistic at scale but selective in execution. Attackers first compromised a wide pool of routers, then filtered DNS traffic to identify high-value intelligence targets. Targeted domains included Microsoft Outlook services, and Microsoft also observed TLS interception against government systems in Africa.
To counter the threat, the FBI issued commands to affected US routers to collect evidence, restore legitimate DNS settings, and block attacker access. Officials said the operation did not collect user content and did not disrupt normal device functionality. Router owners can reverse the changes via factory reset or manual configuration.
Users and organizations are urged to replace end-of-life routers, apply firmware updates, verify DNS settings, and restrict remote administration interfaces.







Leave a Reply