
Google has unveiled a new Android security feature called “Intrusion Logging,” a forensic logging system designed to help investigators detect spyware attacks and infections on mobile devices.
The capability is rolling out as part of Android Advanced Protection Mode (AAPM) and was developed in collaboration with Amnesty International’s Security Lab and other civil society organizations.
The announcement marks the first time a major mobile platform vendor has introduced a built-in feature specifically intended to support consensual forensic investigations into advanced cyberattacks targeting journalists, activists, politicians, and other high-risk users.
Amnesty International, which acted as a design partner during development, says the feature addresses a longstanding problem in mobile forensics: Android’s existing logs were never designed for intrusion detection and are often overwritten quickly or inaccessible by the time an investigation begins.
“Surveillance actors are increasingly aware of forensic efforts and are more diligent in hiding their actions on targeted devices,” Amnesty International’s Head of Security Lab, Donncha Ó Cearbhaill, said in the organization’s technical briefing. “Intrusion Logging promises to help shift the balance to the advantage of defenders.”
Catching spyware on Android
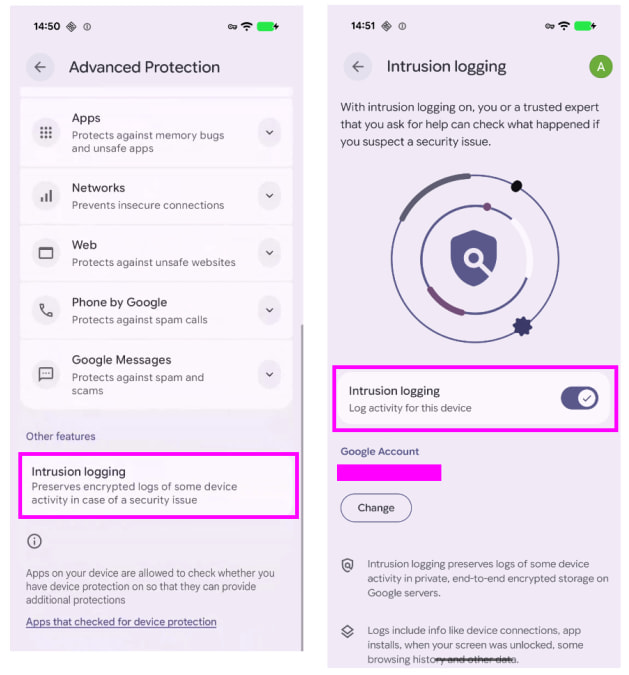
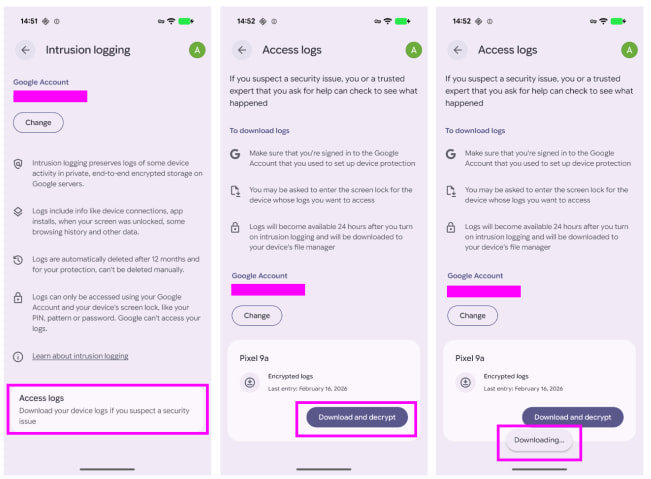
Intrusion Logging is part of Android’s Advanced Protection Mode, a hardened security profile aimed at users facing elevated risks from spyware and targeted attacks. The feature stores forensic logs in encrypted form inside the user’s Google account, but the logs are protected with a user-generated encryption key, preventing Google or third parties from accessing their contents.
The logs are uploaded periodically and can later be downloaded and decrypted by the device owner for analysis or secure sharing with forensic specialists.
Google says the feature is rolling out to devices running Android 16 with the December security update and newer releases, initially focusing on Pixel devices before broader Android OEM adoption.
According to Amnesty, the system captures three major categories of events relevant to intrusion investigations:
- Security events
- DNS activity
- Network connection events
These logs can help investigators determine whether a device was unlocked during a seizure, whether Android Debug Bridge (ADB) commands were executed, if files were transferred from the device, or whether suspicious apps were installed and later removed.
The system can also expose potential command-and-control (C2) traffic tied to spyware infections by logging DNS lookups and outbound connections associated with specific Android applications.
Amnesty Int.
Amnesty International says the feature is especially valuable in scenarios where targeted users only discover potential compromise months after an incident occurred.
Historically, investigators relied on volatile Android artifacts such as Logcat buffers, bug reports, crash tombstones, or limited Google Takeout data. Those records were often incomplete, quickly overwritten, or inaccessible without elevated permissions. Intrusion Logging instead creates a persistent forensic trail specifically intended for security investigations.
Amnesty simultaneously released updates for AndroidQF and the Mobile Verification Toolkit (MVT) to support automated acquisition and analysis of Intrusion Logging data.
MVT’s new check-advanced-logs module can parse the collected data, generate timelines of events, and flag suspicious indicators such as known malicious domains or unusual application behavior.
Amnesty Int.
It’s important to note that Intrusion Logging must be enabled before an incident occurs, meaning it cannot recover historical evidence retroactively. The feature also requires Android 16 or newer and a linked Google account.
Android 17's new privacy and security protections
Alongside the Intrusion Logging rollout, Google also previewed several privacy and security features coming with Android 17 later this year.
Some of the most notable additions include:
Verified financial calls – Android will detect spoofed calls impersonating participating banks and automatically terminate fraudulent calls.
Expanded Live Threat Detection – On-device AI will monitor applications for suspicious behavior such as SMS forwarding abuse, hidden overlays, or stealthy background activity.
Accessibility service restrictions – Android 17 will block non-accessibility apps from using accessibility APIs under Advanced Protection Mode, limiting abuse by spyware and malware.
Temporary precise location sharing – Users will be able to grant apps temporary access to precise location data only while actively using the app.
Improved location access transparency – A new location indicator will show when apps are actively accessing location data and allow users to review recent usage.
Granular contact sharing – A new contact picker system will let users share only selected contacts and specific data fields with apps instead of exposing entire address books.
Android OS verification – Pixel devices will gain the ability to verify whether they are running an official Android build instead of a modified or tampered version.
OTP protection – Android will temporarily hide one-time passwords from most applications to prevent malicious apps from intercepting authentication codes.
Expanded theft protections – Android 17 will strengthen PIN brute-force protections, improve “Mark as lost” functionality, and expand theft detection features globally.
Post-quantum cryptography support – Google is adding new cryptographic protections intended to defend against future quantum-computing threats.
Google says many of these protections are aimed at countering increasingly sophisticated financial fraud, spyware operations, and mobile device theft campaigns targeting Android users worldwide.







Leave a Reply