
“Kazuar,” a long-running malware platform linked to the Russian state-sponsored threat group Secret Blizzard, has evolved into a stealthy peer-to-peer botnet designed for persistent intelligence collection.
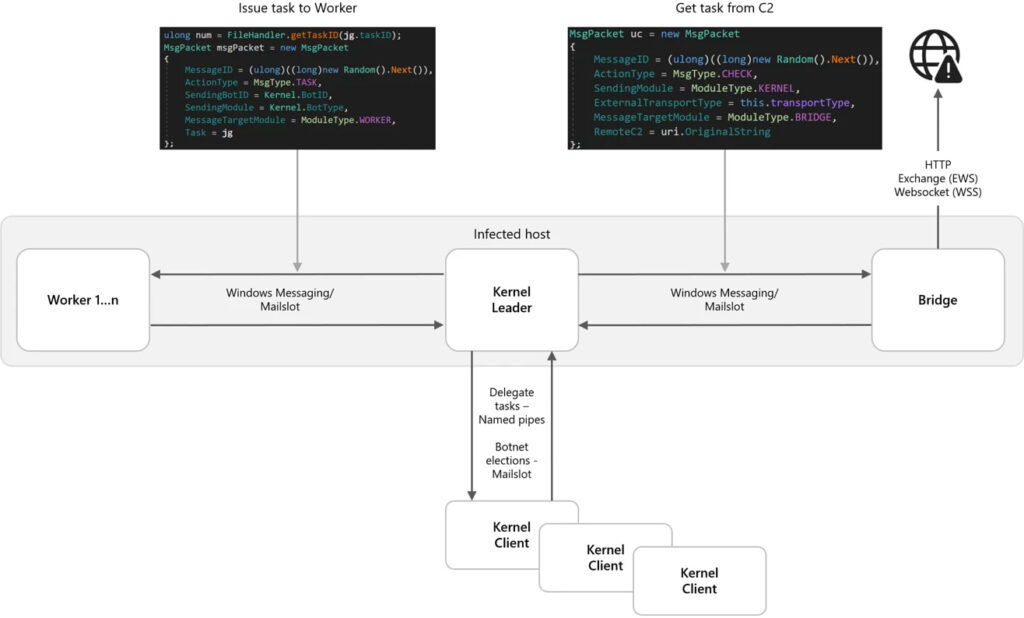
Microsoft Threat Intelligence reports that Kazuar has transformed from a conventional backdoor into a modular ecosystem built around three separate components, Kernel, Bridge, and Worker modules, that collectively enable covert command-and-control (C2), distributed task execution, and resilient communications while minimizing detection opportunities.
Secret Blizzard, which the US Cybersecurity and Infrastructure Security Agency (CISA) attributes to Center 16 of Russia’s Federal Security Service (FSB), has historically targeted government, diplomatic, and defense-related organizations across Europe and Central Asia.
Modular architecture built for stealth
Microsoft’s analysis shows that Kazuar now operates as a highly modular botnet, with functionality divided among specialized components rather than centralized in a single malware process.
The “Kernel” module acts as the core orchestrator, managing tasks, coordinating communications, and maintaining operational state across infected systems. Before activating, the malware performs extensive anti-analysis checks, including scanning for debugging tools, sandbox-related DLLs, and canary files commonly used by researchers.
The “Bridge” module serves as the malware’s communications proxy, handling outbound traffic to external infrastructure via multiple protocols, including HTTP, WebSockets, and Exchange Web Services (EWS)-based email. Meanwhile, the “Worker” module executes espionage tasks, including keylogging, screenshot capture, file harvesting, and system reconnaissance.
Microsoft says the architecture is specifically designed to reduce visibility into malicious activity. Rather than allowing all infected hosts to communicate externally, Kazuar elects a single “leader” system within the botnet that alone interacts with the command infrastructure while other infected systems operate in a silent mode.
“This upgrade aligns with Secret Blizzard’s broader objective of gaining long-term access to systems for intelligence collection,” Microsoft explained.
The malware uses multiple inter-process communication (IPC) mechanisms, including Windows Messaging, named pipes, and Mailslots, to route instructions internally between modules. Communications are encrypted, and fallback mechanisms ensure continued operation if one transport channel fails.
Extensive espionage capabilities
Kazuar’s Worker modules can gather a wide range of information from infected systems, including installed software, browser history, recent documents, Outlook data, USB device information, network shares, running processes, PowerShell versions, Windows update history, and security product details.
The malware can also:
- Capture screenshots
- Monitor active windows
- Record keystrokes
- Enumerate email information through MAPI
- Encrypt and exfiltrate collected data after staging it in a dedicated working directory
Microsoft says the malware relies heavily on Google Protocol Buffers (Protobuf) to serialize and route internal communications between modules, as well as to package data sent to C2 infrastructure.
Mitigation guidance
Microsoft says defenders should focus not only on malware samples themselves but also on behavioral indicators such as leader election activity, IPC message routing, staged working directories, and periodic exfiltration attempts.
The researchers urge organizations to strengthen endpoint protections using Microsoft Defender and attack surface reduction rules, including blocking obfuscated scripts, preventing abuse of vulnerable signed drivers, and enabling endpoint detection and response (EDR) in block mode.
Additional recommendations include enabling PowerShell logging, enforcing execution policies, enabling tamper protection, and using browser protections, such as Microsoft SmartScreen, to block malicious websites and phishing infrastructure.







Leave a Reply