
Proton Mail has introduced optional post-quantum cryptography (PQC) protection for all users, allowing them to secure their email communication against potential future attacks from quantum computers.
The feature is available starting today across all plans, including free accounts.
While today’s encryption standards, primarily RSA and elliptic curve cryptography (ECC), remain secure against classical computers, they could eventually be broken by sufficiently powerful quantum systems using algorithms such as Shor’s algorithm.
To address this, Proton Mail added support for post-quantum-ready encryption keys that can be generated and used for new encrypted emails. Once users enable the feature in their account settings, Proton Mail begins encrypting future messages with these quantum-resistant keys. However, the protection is not retroactive, meaning existing emails stored in users' inboxes remain encrypted with older cryptographic schemes.
Proton Mail is one of the world’s most widely used privacy-focused email services, serving millions of users globally with end-to-end encrypted communications.
The implementation also introduces support for OpenPGP v6, a newer version of the widely used encryption standard that enables compatibility with modern cryptographic algorithms, including PQC. Proton says this will help standardize quantum-safe email across the broader ecosystem, with ongoing collaboration involving projects like Mozilla Thunderbird to ensure interoperability between providers.
How to turn PQC on
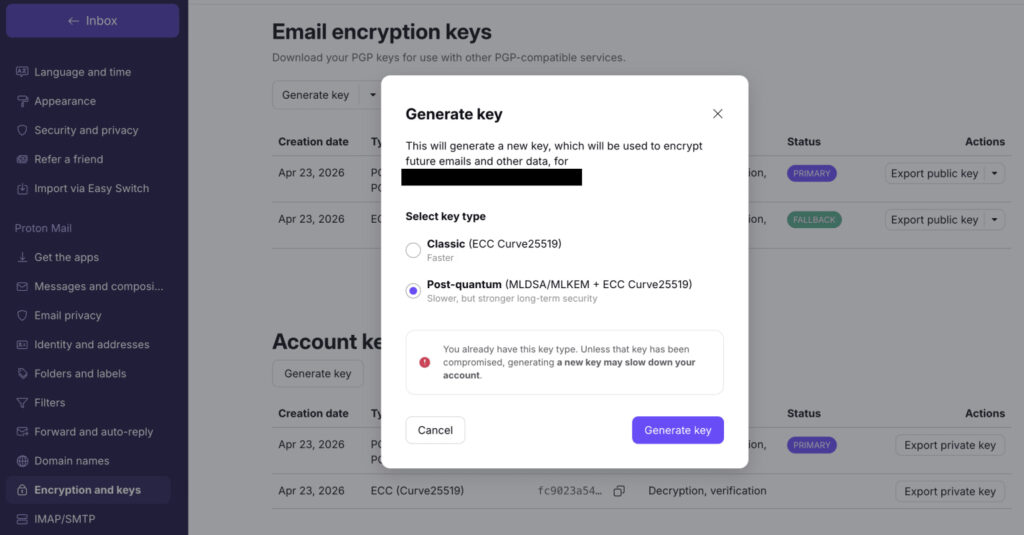
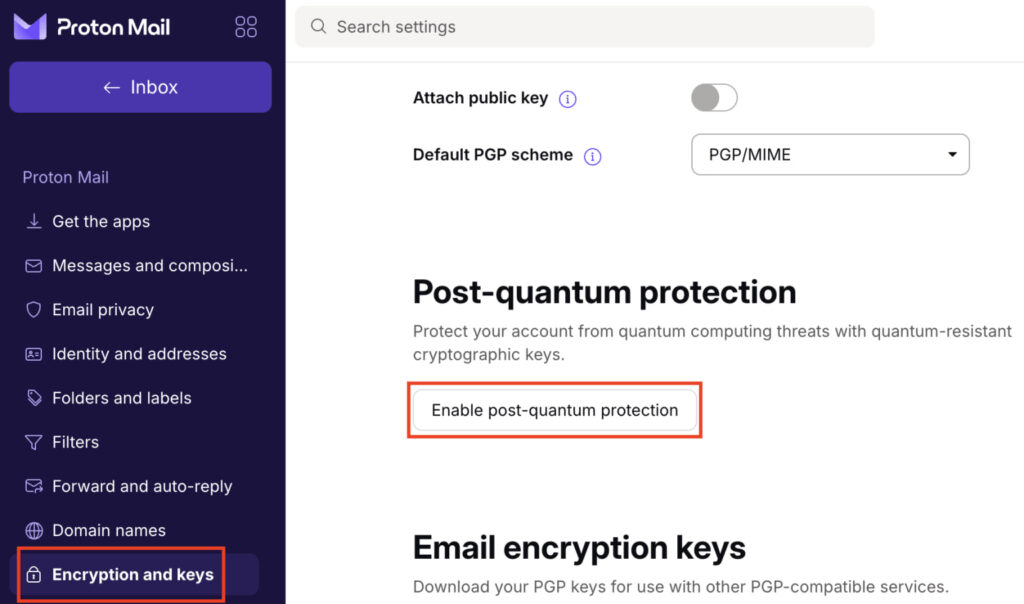
Enabling the new protection requires users to update to the latest Proton apps, as older versions do not support PQC keys. Once activated, the feature replaces existing encryption keys for future communications, while maintaining familiar key management capabilities such as generation, revocation, and export. Proton notes that enabling PQC may introduce a slight performance impact, though this should be negligible on modern devices. Additionally, users relying on end-to-end encrypted email forwarding will see that feature temporarily disabled, as it is not yet compatible with the new cryptographic scheme.
To enable post-quantum protection, sign into account settings, navigate to the ‘Encryption and keys’ section on the sidebar, and activate the feature to generate new keys. For more information on activating PQC, check out this short guide.
The move reflects growing concern over “harvest now, decrypt later” attacks, where adversaries collect encrypted data today with the intention of decrypting it once quantum computing capabilities mature. This threat model has accelerated the adoption of post-quantum cryptography across the tech industry, even though practical quantum attacks are not yet feasible.
In a recent interview with CyberInsider, University of Michigan professor and cryptography expert Chris Peikert warned that even a small probability of quantum computers breaking current encryption represents a major risk due to the catastrophic consequences such a breakthrough would have on global digital security. He emphasized that transitioning to post-quantum systems requires significant time and planning, making early adoption critical.






Leave a Reply