
ProtonMail often touts its Swiss jurisdiction and privacy guarantees, but at the same time, it is complying with a record number of data request orders going through the Swiss legal system.
ProtonMail is one of the most popular secure email services in the world, having launched in 2014 via a crowdfunding campaign. It promises a higher level of privacy and security over other email platforms and frequently touts its Swiss jurisdiction.
While Switzerland is a good jurisdiction for privacy-conscious users, it’s certainly no guarantee for data security.
On the ProtonMail homepage, you can see references to “strict Swiss privacy laws” that should keep your data secure.
Let’s dig deeper.
Proton provides data to the FBI and other police agencies
This past week Forbes ran an article on a case where the FBI was able to get data on a U.S. ProtonMail user who was being investigated for harassment (but not charged with any crime).
The warrant revealed that the FBI managed to acquire data from Proton Technologies, the owner of Proton Mail, to kick off the hunt for the anonymous emailer. It’s a rare example of a U.S. data request on Proton and shows how small pieces of metadata from encrypted software can prove hugely useful for cops trying to unmask users who expect strong privacy protections from such apps.– Forbes
In this case, Proton Technologies provided the FBI with the “recovery and associated email addresses” of the user, which lead to his discovery.
Two years ago, RestorePrivacy ran an article on another ProtonMail logging case involving a French activist who was also a ProtonMail user. In that case, French police received the user’s IP address from Proton Technologies, leading to the arrest of the suspect.
This begs the question, how common are cases like these, particularly with cases that don’t end up in the news?
Nearly 6,000 data request orders “complied with” in 2022
To ProtonMail’s credit, the organization publishes a transparency report going back to 2017. In it, we find the following statistics detailing legal orders for user data.
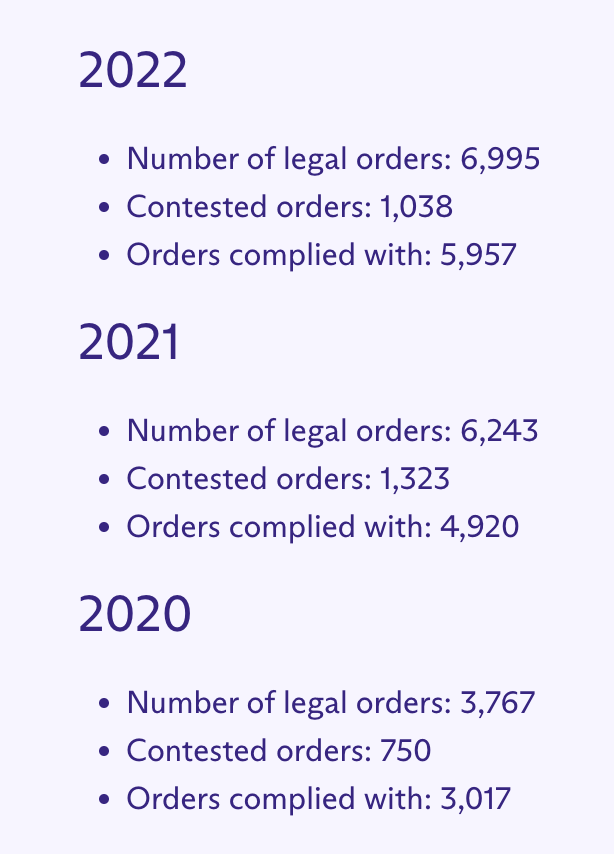
Additionally, you can see that the number for all three categories continues to climb every year. With that being said, this growth is also not surprising given that ProtonMail is a popular brand with a growing user base. Aside from email, the company also offers Proton VPN and a Proton Pass, a password manager.
Proton prefaces the transparency report by noting that data requests must go through Swiss legal channels.
From time to time, Proton may be legally compelled to disclose certain user information to Swiss authorities, as detailed in our Privacy Policy. This can happen if Swiss law is broken.
… Swiss authorities may from time to time assist foreign authorities with requests, provided that they are valid under international legal assistance procedures and determined to be in compliance with Swiss law. In these cases, the standard of legality is again based on Swiss law. – Proton Transparency Report
Proton Mail provided us with an explanation for the growing number of cases below.
The increase in cases reflects the increase in our user base. As Proton has scaled, and now has 100m sign ups to our services, it’s not surprising that these figures have risen. However, these cases have come through the Swiss authorities (which is a good sense check of their validity) and have also been reviewed by Proton to ensure they are reasonable for us to respond to (hence why there are also cases that we have not complied with mentioned on the transparency report). Please note that in all cases email content, attachments, files etc are always encrypted and cannot be read.– Proton spokesperson
Is Proton Mail still secure and private?
The answer to this question all boils down to determining your threat model and the adversaries you are trying to protect yourself against.
In short, the answer is yes if you are looking for a secure, encrypted email service that does not have access to the contents of your inbox. After all, ProtonMail is far better than Gmail or Yahoo when it comes to privacy.
If you are doing things to attract the attention of law enforcement, then the data you provide when you use ProtonMail, such as IP address and recovery email, may be shared with authorities if Proton Technologies is legally compelled to do so in Swiss court.
All businesses must comply with the laws in the countries where they are legally based. The only other option is to shut down, like we saw with CTemplar in 2022 and Lavabit back in 2013.
Furthermore, there are also different alternatives with various privacy and security benefits, as you can see in our secure email guide.
Consider your OPSEC
It’s also important to consider what data you provide when you sign up for a service. In the ProtonMail cases we mentioned above, the data that exposed the users was the user’s IP address (French activist) and the “recovery and associated email addresses” (US suspect investigated by the FBI recently).
By protecting the data you provide when interacting with the email service, you can make your email account even more private and secure.
- IP address – Use a good VPN service to hide your IP address whenever using the email service (or anytime you are online for that matter)
- Recovery email – Consider using a disposable email for a recovery email, or a new and unused recovery email address that is not linked to your identity
- Payment methods – Email is fundamentally different from a no logs VPN service in that there is always personal data stored (your inbox contents and other account data). Therefore it’s more important to use an anonymous payment method if you want more privacy.
Having good OPSEC is a crucial consideration whenever you are using privacy tools.






lol.. too many reasons against:
– board of directors composition
– data request statistics
– false claims in the past (‘we don’t log you’) ..logging is opt-out currently
– ‘If you don’t pay, you’ll be the product’
– certain sponsorships / funding..
Tutanota not better.. it’s privacy-as-a-parfume.
Completely agree—about both Protonmail and Tutanota.
(I’ve posted elsewhere on RP about my own, very bad, privacy-related fiascos with Tutanota.)
And, I want to express my admiration for Sven, who (when he was the primary person running this site/resource—but possibly still [I just see far less of his work now]) so ethically balanced (much-needed, I’m sure) efforts to keep this site viable/running, with his often rather unsparing approach toward (even RP-recommended [and thus commission-providing]) services for which evidence of questionable security/privacy practices comes available.
He has struck a great balance, and so I’ve trusted Sven since c. 2018.
Thank you Poppy. You are right, there is a balance, and we all have bills to pay.
I’ll second that comment re Sven/RP. The best example of this is the article Is Tor Trustworthy and Safe? At a time when the majority of those who should know better, such as EFF, were/are dangerously and inexusably promoting Tor with no caveats whatsoever, this resource provides the clearest and most detailed analysis I found, and I looked long and hard after seeing routing activity that suggested that all was not as it seemed in the Tor system. But for RP I would have accepted the blinkered/ignorant/compromised advice from all these other so-called watchdogs.
When we read something, we often interpret it in a very literal sense, sometimes too literal. It’s like looking at a painting and only seeing the brush strokes, without considering the bigger picture.
While I understand where @Truth is coming from. His apology seems unnecessary. The tone of the blog suggests that this website isn’t as dedicated to Proton as Sven claims it to be. It’s like a friend who says they support you, but their actions say otherwise.
However, to suggest or imply that disclosing Proton’s recovery email address and other metadata is insignificant is like saying that the foundation of a building doesn’t matter. It shows a lack of understanding or perhaps even bias. Just as the foundation is crucial to the stability of a building, the security of our personal information is crucial to our online safety.
Furthermore, Proton’s official response seems to be on Reddit in their subreddit which is asinine in my opinion. It should be on their website.
Just one minor thought.
I am not intending to minimize the metadata given. I think it is not good.
However, in my case, I am easily found based on my email (business). I supplied a recovery because I needed it.
However, if I am desperate to remain anon, I am not going to use an incriminating email, nor will I use a restore email that can be handed.
I also won’t use subject lines. Based on these three things as well as Tor, or Onion routing,y meta will be very, very little to nothing.
This guy being referenced had a backup email, then used that SAME email to open a us based social media account.
I’m not downplaying the meta but if someone is going to break a law, they already are behind the 8 ball. This just shows he was further behind than tought. He willingly gave it.
Even Tutanota and others have Metadata. that is all but unavoidable.
The only things I found that hasn’t has been Sessions and Signal.
As for the other comments, I agree with you.
And yet the only info given was the recovery email and a few other Metadata
They got nothing else.
I saw this on Reddit and it has a great back and forth:
https://www.reddit.com/r/ProtonMail/comments/15luwua/perhaps_not_as_private_as_we_thought/
After sifting through the comments and supporting docs, Proton still is good.
I do wonder, who do you all recommend? Mailfence? https://cyberinsider.com/email/reviews/mailfence/
Not open source, logs data, 14 eye. Yes, strong encryption, but can we trust? How?
Second recommendation: Tutanota.
Rolls their own encryption, part of the 14 eye.
Again, can you trust their encryption is done right? There seems to be major issues, even in as simple as signing up. good, maybe? But verifiable? And if merely signing up brings problems, what about when real system work must be done?
Plus they have to log as demanded. Sure they can’t see anything, but they WILL hand over anything they have.
All this to say it seems this site has a strong bias against Proton simply because…well, Proton, yet they are no less or no more open and potentially vulnerable than the others. Actually, Proton may still be stronger.
The difference: They seem to be more open about what they do and why.
Don’t take my word, read through the info on the reddit. But, Sven, please don’t mislead someone to ignore Proton and jump to your recommended, when your recommended is not as resistant (non Swiss, not open source) as Proton itself.
I also know the Tutanota guy was here once, have you asked Proton to rep to come on for a Q/A? Would be interesting to engage there.
You claim, “this site has a strong bias against Proton”
yet Proton Mail is still among our top recommendations and has been for years:
https://cyberinsider.com/email/secure/
Sven,
Ok. Perhaps I cam off too strong on that and I apologize.
What I was reacting to is how quick PM was given a new post dinging it for “handing over” info, without also including the docs that possibly support their strength and security.
At the same time, Tutanota, for example, is treated a little different.
for example, under Tutanota, they have a long list of positives. great.
but what is not mentioned is:
1) They are part of the 14 eyes and therefore are part of international survalince.
2) Germany itself told them to monitor an account and hand over what they had.
3) They too will hand over anything required too.
4) German Government just GAVE tutanota money to increase encryption which they themselves want a back door.
Yet PM has been dinged because they were also given money.
could we ask for these negatives be added to Tutanota for full disclosure?
A reader will see very little negatives on Tutanota, but look at PM and think, “Wow, they’ll hand over anything!” without realizing the info PM handed over:
first was an outside email that the account holder supplied voluntarily.
and second, little to no other data was handed because of the security.
So I do apologize if I came off as hard but when I see these remarks, and then a seeming quietness on others, I felt I should say something.
Tutanota, per my experience, bans your account if you use a vpn and then they lie and say you’re entering a wrong password.🤡
@.
I used to use them as well.
I now use PM.
I just checked Tutanota’s review and none of the issues I said here were added.
@Sven, could you add these negatives to Tutanota?
1) Part of the 14 eyes.
2) Gets funding from German government
3) Cheap intro price until more things are needed. Then gets as expensive as PM.
4) Technical work of apps and web mail can be hit or miss.
5) Tech support can be hit or miss.
6) Rolls their own encryption, which could be good but there must be trust they are doing it right
7) Part of the E.U. so affected by their laws toward encryption.
8) Will log IP’s and turn over any data they have if demanded by a German or international law under the 14 eye survellience.
and then keep the three negatives you already have.
this will bring a good record of negatives to the review and be balanced.
Thanks.
Truth, just leave your own review and negatives in the Tutanota review comment section.
Forgot to add,
at the bottom there is the checklist.
Seeing the negatives between Mailfence, Tutanota, and PM,
is there a reason Mailfence is there and not PM? PM is open source and Mailfence is not making PM stronger.
Between companies and individuals, we send and receive about 347.3 billion emails every day, 61.9% of which we open on mobile devices.
Proton’s website lists three methods of account password recovery. Two of those could be turned off completely, leaving only the recovery phase, which is required for both account recovery, and data recovery. Would that have been enough to secure the account from the search?
Sven Sir generally it is said it all depends on one’s preferences and threat model. But it is never emphasized ideally and objectively what should be the privacy and security threat model for commoners and how they can secure and protect themselves without sacrificing convenience and should not have to go into the jugglery of undertaking difficult to implement and unsustainable measures.
In my opinion propaganda, censorship and indoctrination are real threats to human society and soul of a person. Also for people at a different level the threats are malware and social media frauds causing loss of reputation and humiliation or financial loss or stalking by partner in personal relationships. For organisations data loss which is their asset. The data collected by data brokers and analytics companies does fall into the hands of bad actors and makes their work of targeting people easier. It is used by dictatorial regimes to strengthen their exploitation. Privacy is a part of device security which is intrinsic to personal security as these devices are a part of our lives. Privacy is not bigger than security but a safeguard to security.
Again this security is with respect to security from others. For our security from ourselves one can befriend technology and use it wisely for learning, understanding and knowledge. Likewise for security from hostile politics technology can be a good friend to organise and strength values and virtues of a society.
Sven Sir also email protocols are inherently insecure as they are still from a bygone era when the need for online security and privacy was not fully realised. Snowden confirmed this in one of his tweets.
At the end of the day it is humans who read data and find out things and act on it. Proton mail makes a person stand out from the crowd as it indicates a person has something to hide.
It is better to use secure Messenger apps for sensitive communication than using email.
Also one needs to pay for proton mail and still it might not have spam filtering and security as good as Gmail and Outlook. Google said it does not scan emails anymore and Outlook paid version has no advertisements and added Security which I use.