A security researcher has revealed that Notion’s public pages can expose the email addresses of all contributors through an unauthenticated API request, a behavior that has reportedly been known since 2022 and is still present today.
The issue allows anyone to extract user data, including names, emails, and profile images, without logging in or interacting with the platform.
Researcher “impulsive” (@weezerOSINT) detailed how Notion’s backend API leaks personally identifiable information (PII) tied to public pages. According to a thread on X, the exposure stems from how Notion handles permissions metadata. Public pages include editor UUIDs within their block permission structures, which can be retrieved without authentication. These identifiers can then be submitted to the /api/v3/syncRecordValuesMain endpoint, which returns associated user details, including their email addresses.
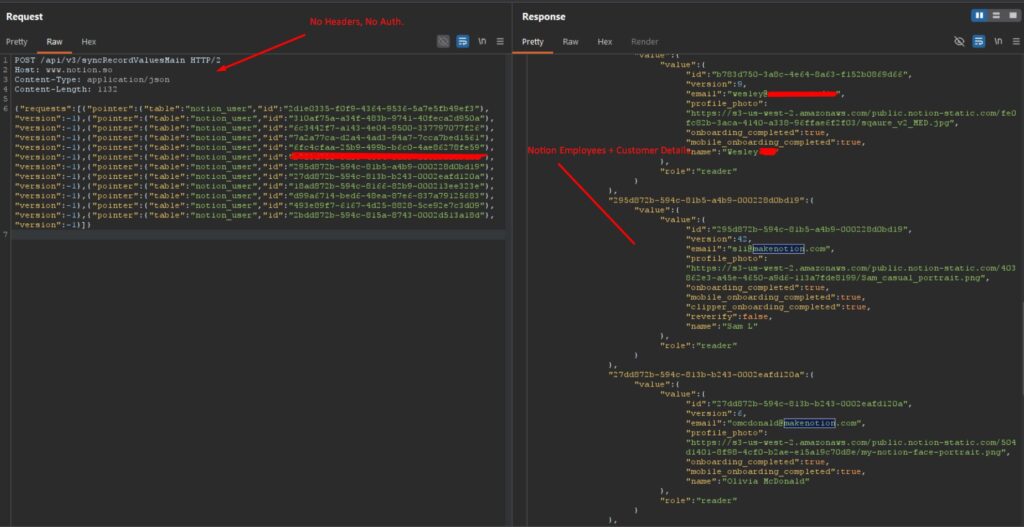
To validate the issue, the researcher tested Notion’s own publicly accessible Community page, extracting 13 user UUIDs and successfully resolving 12 of them to email addresses. The returned data reportedly included internal Notion employee accounts, a production service account (svc-notion-prod@makenotion.com), and at least one external collaborator. The researcher emphasized that this process requires no authentication tokens, cookies, or special privileges, just a single, crafted POST request.
Notion, a widely used productivity and collaboration platform valued at approximately $11 billion, is relied upon by individuals, startups, and large enterprises for documentation, internal wikis, and project management. Its “Publish to web” feature is commonly used to share content publicly, including help centers, onboarding materials, and job listings, thereby significantly expanding the potential scope of exposure.
The researcher warned that thousands of publicly indexed Notion pages, easily discoverable via search engines, may be leaking contributor email addresses. In enterprise environments, where large teams collaborate on shared documents, a single public page could expose hundreds of corporate email accounts. The researcher further notes that the data can be enriched using another unauthenticated endpoint, getLoginOptions, which reveals whether an account uses password-based authentication or single sign-on (SSO). This combination could provide attackers with a curated list of targets for credential stuffing or phishing campaigns.
Notion exposing user PII since 2022
The vulnerability was reportedly first disclosed through HackerOne on July 28, 2022, where it was triaged as “informative” and did not result in a fix, CVE assignment, or bounty. The researcher states they independently rediscovered and reported the same issue, only for it to be marked as a duplicate. Testing conducted in April 2026 confirmed that the behavior remains unchanged.
In response to the disclosure, Notion’s Max Schoening stated that while the behavior is documented and users are warned when publishing pages, the current implementation is insufficient. He added that Notion is exploring fixes, including removing PII from public endpoints or introducing email proxying, similar to GitHub’s approach for public commits.
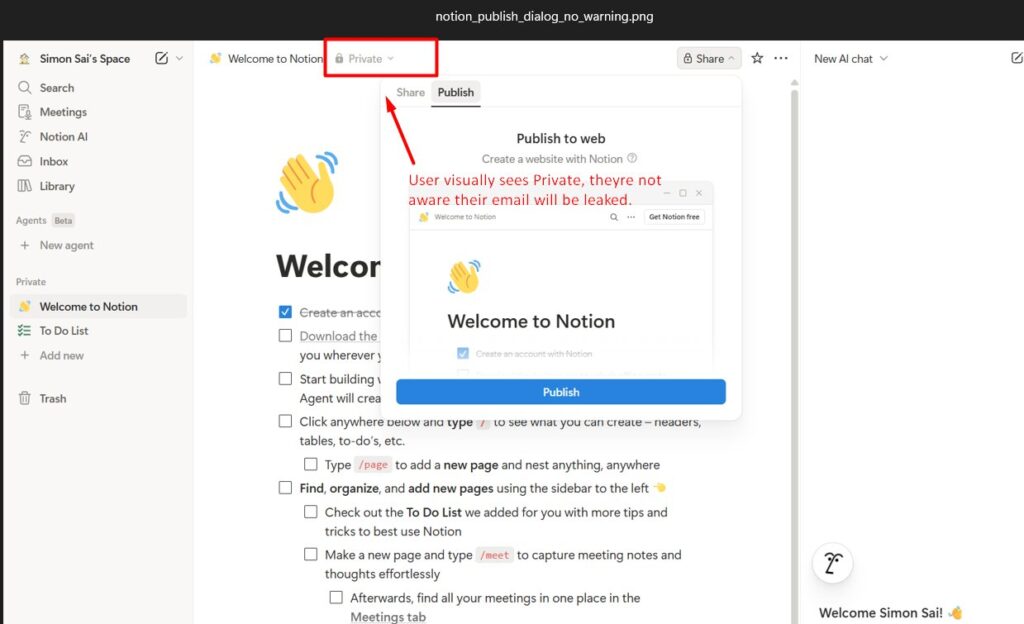
However, the researcher disputed the claim that users are adequately warned. In follow-up testing using a fresh account, they reported that the “Publish to web” interface contains no mention of email exposure or API-based data leakage. The publishing dialog reportedly includes only basic controls and a preview, with no indication that contributor information becomes accessible externally. Additionally, even when a page is labeled “Private” in the interface, underlying API calls can still expose associated user data if the page has been published.
Until a fix is implemented, users and organizations should review their Notion sharing settings and avoid publishing pages that involve sensitive collaborators. Where public sharing is required, limiting the number of editors and avoiding the use of corporate email accounts on exposed pages can reduce risk.







Leave a Reply