
Google has released an emergency Chrome update to patch a zero-day vulnerability actively exploited in the wild, alongside 20 additional security flaws.
The issue, tracked as CVE-2026-5281, is a high-severity use-after-free bug in the Dawn graphics component.
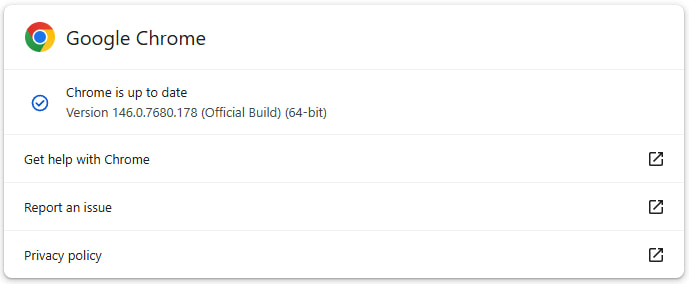
The fix was rolled out on March 31, 2026, with Chrome version 146.0.7680.177/178 for Windows and macOS, and 146.0.7680.177 for Linux. Google confirmed in its advisory that it is aware of active exploitation but has restricted technical details to prevent further abuse while users update their browsers.
The zero-day vulnerability, CVE-2026-5281, was reported on March 10, 2026, by an anonymous researcher. The flaw is described as a “use-after-free” issue in Dawn, a Chromium component that implements the WebGPU standard and handles low-level GPU interactions.
Use-after-free vulnerabilities occur when memory that has already been released is mistakenly reused, which can lead to memory corruption. In browser contexts, these bugs are particularly dangerous because they can potentially allow attackers to achieve arbitrary code execution within the renderer process.
Although Google has not disclosed exploitation details, such flaws are typically triggered through specially crafted web content. An attacker-controlled webpage could manipulate GPU-related operations to corrupt memory and potentially escape the browser’s sandbox.
In addition to the zero-day, Google addressed 20 other vulnerabilities in this release, most of them rated high severity. These include multiple memory safety issues, such as:
- Heap buffer overflows in GPU and ANGLE components
- Integer overflows in media codecs and ANGLE
- Use-after-free bugs affecting WebCodecs, WebGL, Web MIDI, PDF rendering, and navigation
- Object corruption in the V8 JavaScript engine
- Insufficient policy enforcement in WebUSB
Google is rolling out the update gradually, meaning some users may not receive it immediately. To apply the security update, open Chrome, go to Settings > About, and allow the update checker to fetch the latest update. A restart of the program will be required for the fixes to apply.
Typically, these flaws are exploited in highly targeted operations, though in some cases, they are leveraged in broader-scoped operations. Given the lack of details about the observed attacks, users are recommended to apply the available update as soon as possible.







Leave a Reply