A major supply chain attack targeting the widely used Axios JavaScript library briefly exposed developers to a stealthy remote access trojan (RAT).
The incident unfolded between March 30 and March 31, 2026, when threat actors gained control of the npm account belonging to Axios maintainer jasonsaayman. Researchers from Socket and independent analysts identified that two tampered releases, axios@1.14.1 and axios@0.30.4, were published within 39 minutes of each other, both outside the project’s normal GitHub-based release workflow. The attacker altered the account email to a ProtonMail address and used a stolen npm token to bypass the repository’s trusted publishing mechanism.
Axios is one of the most widely adopted HTTP clients in the JavaScript ecosystem, with hundreds of millions of monthly downloads and extensive use across frontend frameworks, backend services, and enterprise applications. Its popularity significantly amplified the potential impact, as projects using permissive version ranges could have automatically pulled the malicious updates during routine installs.
Notably, the attackers did not modify the Axios source code. Instead, they introduced a single “phantom” dependency, plain-crypto-js@4.2.1, which is never imported by the legitimate library. This package, published shortly before the attack from a separate throwaway account (nrwise@proton.me), was designed solely to execute a postinstall script during npm installation.
Security analysis shows that the malicious dependency deployed a multi-stage infection chain. Its embedded dropper (setup.js) used layered obfuscation to hide functionality, then contacted a command-and-control (C2) server at sfrclak[.]com:8000 to retrieve platform-specific payloads. The malware delivered:
- A Mach-O RAT on macOS, disguised as a system cache file (/Library/Caches/com.apple.act.mond)
- A PowerShell-based payload on Windows, executed via a hidden VBScript and a renamed interpreter (%PROGRAMDATA%\wt.exe)
- A Python-based backdoor on Linux, saved to /tmp/ld.py
The final payload was a fully functional RAT capable of system reconnaissance, command execution, and payload deployment, with periodic beaconing to the attacker's infrastructure.
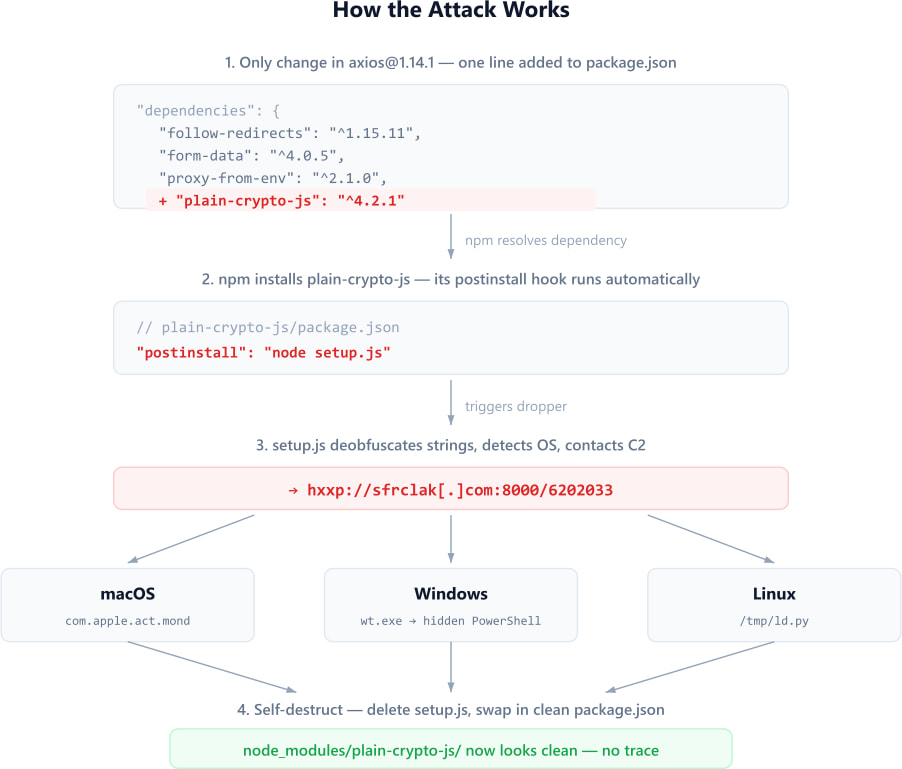
To evade detection, the dropper employed anti-forensics techniques by deleting itself, removing its malicious package.json, and replacing it with a clean decoy file. This effectively erased visible evidence from node_modules, making traditional audits unreliable. In many cases, the only remaining indicator of compromise is the unexpected presence of the plain-crypto-js directory or OS-level artifacts left by the second-stage payload.
The attack was carefully staged. A benign version of plain-crypto-js was first published to establish credibility, followed by the weaponized version hours later. The malicious Axios releases were then pushed after the dependency had aged enough to avoid suspicion from automated scanners.
Both compromised Axios versions were removed by npm within roughly three hours, and the malicious dependency has since been replaced with a security placeholder. However, the short exposure window was sufficient to pose a serious risk, particularly to CI/CD pipelines and automated builds.
Developers are recommended to check for the presence of axios@1.14.1, axios@0.30.4, or plain-crypto-js, and if found, rotate all credentials and perform a full system cleanup.







Leave a Reply