
Kaspersky researchers have uncovered strong technical links between “Coruna,” a sophisticated iOS exploit framework recently highlighted by Google and iVerify, and the infamous Operation Triangulation campaign.
The investigation builds on earlier reports by Google and iVerify describing Coruna, a powerful exploit kit targeting Apple iPhones in targeted attacks, including watering-hole campaigns in Ukraine and financially motivated operations in China.
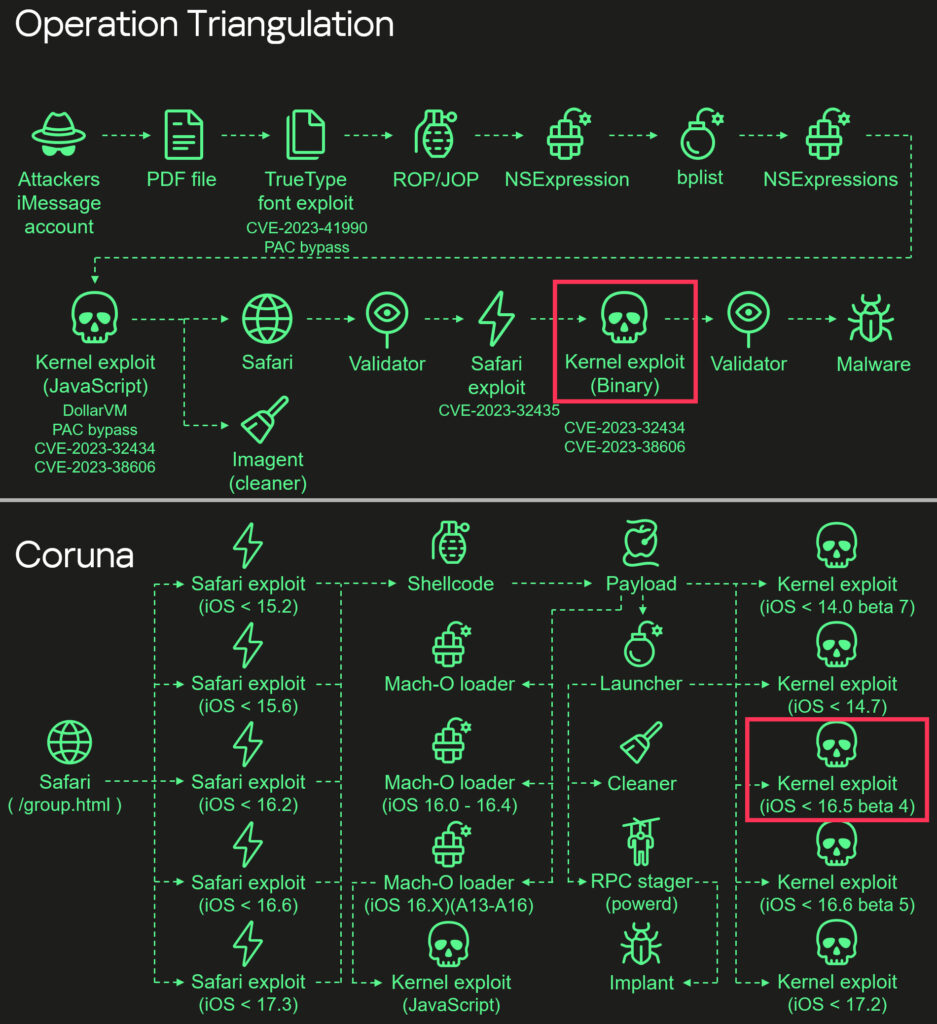
Kaspersky’s involvement stems from its earlier discovery of Operation Triangulation, a long-running advanced persistent threat (APT) campaign targeting iOS devices. The company initially detected the operation while monitoring anomalous traffic on its own corporate Wi-Fi network, eventually uncovering a highly advanced spyware implant delivered through multiple zero-day vulnerabilities.
Kaspersky researchers obtained active Coruna distribution links referenced in Google’s report, enabling them to collect, decrypt, and reverse-engineer the framework’s components. Their analysis revealed that one of Coruna’s kernel exploits, targeting CVE-2023-32434 and CVE-2023-38606, is an updated version of the same exploit previously used in Operation Triangulation. These vulnerabilities had originally been identified as zero-days during that earlier campaign.
Beyond this overlap, Coruna includes four additional kernel exploits not observed in Triangulation, two of which were developed after the campaign became public. Despite targeting different vulnerabilities, all five exploits share a common codebase and are built on the same underlying kernel exploitation framework. According to Kaspersky, this consistency indicates a unified development effort rather than a collection of unrelated tools, reinforcing the conclusion that Coruna is a direct evolution of the Triangulation toolkit.
Kaspersky
Technically, Coruna employs a multi-stage attack chain that begins in Apple’s Safari browser. An initial “stager” fingerprints the target device and selects appropriate remote code execution (RCE) and pointer authentication code (PAC) exploits based on browser and system characteristics. It then retrieves encrypted payload metadata, including decryption keys and component locations.
The payload orchestrates further exploitation by downloading and decrypting additional modules using the ChaCha20 cipher and custom container formats marked by identifiers such as 0xBEDF00D and 0xF00DBEEF. These containers store compressed data and modular components, including kernel exploits, Mach-O loaders, and the final spyware implant. The framework dynamically selects packages based on device architecture (ARM64/ARM64E), firmware version, and CPU generation, enabling broad compatibility across iOS versions.
Once kernel access is achieved, a launcher component takes over, reusing established kernel primitives to avoid re-triggering exploits. It removes forensic artifacts, injects malicious code into legitimate processes, and deploys the implant while maintaining persistence.
Kaspersky warns that Coruna’s modular design and reuse of previously patched vulnerabilities make it particularly dangerous. While originally associated with targeted espionage, the framework is now being adopted in broader cybercriminal activity, significantly expanding its potential impact.
Apple recently published guidance for iOS users on how to defend from these attacks. The key is to apply the latest iOS updates immediately and consider activating the Lockdown Mode on the device.







Leave a Reply