
The FBI has issued a new alert warning that Iranian government-backed hackers are leveraging Telegram as a command-and-control (C2) channel to distribute malware targeting dissidents, journalists, and opposition groups worldwide.
According to the FBI FLASH bulletin, the activity is attributed to cyber actors operating on behalf of Iran’s Ministry of Intelligence and Security (MOIS). Investigators say the campaign has been active since at least fall 2023 and relies heavily on social engineering and tailored malware to infiltrate Windows systems used by individuals perceived as threats to the Iranian government.
The FBI reports that attackers initiate contact through messaging platforms, often impersonating trusted individuals or posing as technical support staff. Victims are persuaded to download malicious files disguised as legitimate applications, including modified versions of tools like KeePass, WhatsApp, or Telegram.
Once executed, the initial payload deploys a second-stage persistent implant. This implant establishes communication with attacker-controlled Telegram bots via the official API, effectively turning the messaging platform into a covert C2 infrastructure.
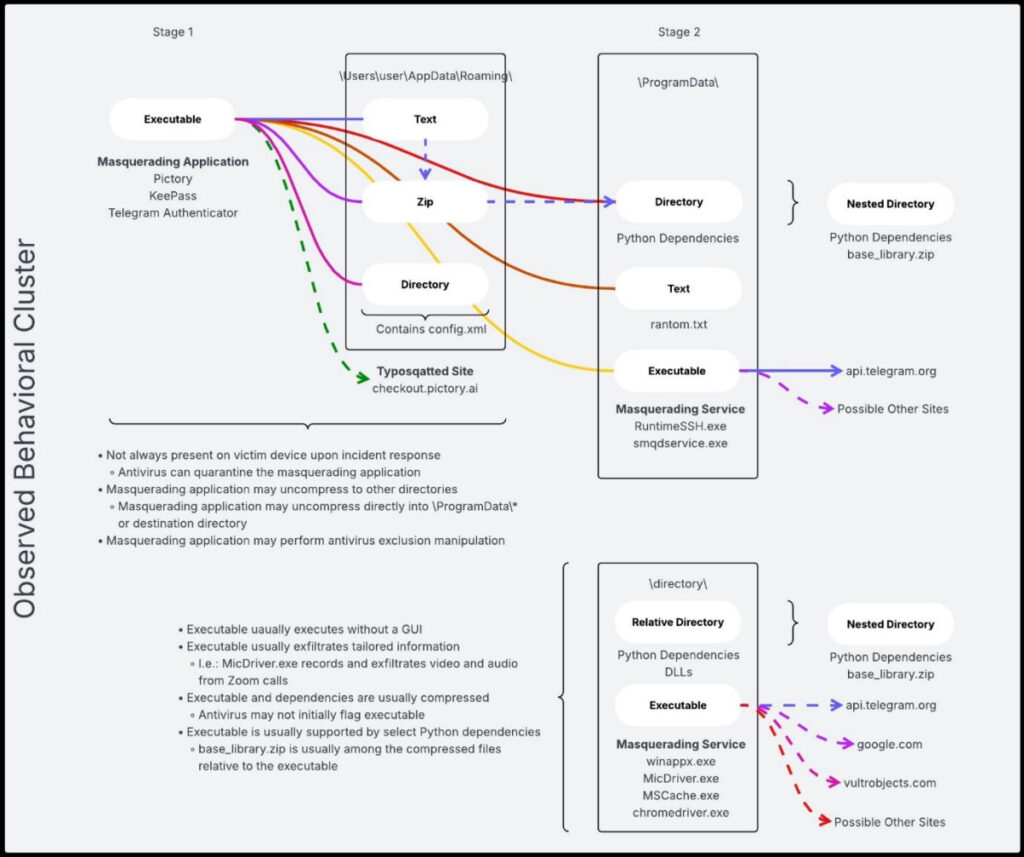
The malware enables remote access to infected devices, allowing attackers to exfiltrate files, capture screenshots, and monitor activity. Some variants include more specialized capabilities, such as recording audio and screen content during Zoom sessions. The FBI identified several malicious components used in the campaign, including MicDriver.exe, MsCache.exe, and RuntimeSSH.exe, which handle data collection, compression, and transmission.
To maintain persistence, the malware modifies Windows Registry entries and uses PowerShell-based evasion techniques to bypass security warnings. Victim-specific customization of the initial payload suggests that attackers conduct reconnaissance prior to targeting, increasing the likelihood of successful compromise.
The FBI also tied elements of this campaign to the “Handala Hack” persona, which claimed responsibility for a July 2025 leak operation targeting critics of Iran’s government. Authorities assess that some of the leaked data was obtained using the same malware toolkit described in the bulletin.
Handala has previously been linked to destructive cyber activity, including wiper malware attacks, and more recently, a disruptive cyberattack against American healthcare technology firm Stryker. The FBI’s findings also confirm Telegram’s inability to shake off cybercrime. Despite recent enforcement efforts, platform abuse persists.
The FBI advises those at high risk to avoid downloading files sent via unsolicited messages, even from known contacts, keep software up to date, and enable multi-factor authentication protection for accounts.







Leave a Reply