The supply chain attack targeting Aqua Security’s Trivy scanner is still evolving, with investigators confirming fresh unauthorized activity and newly discovered compromised Docker images.
In an update published March 23, Aqua Security revealed that its investigation uncovered additional suspicious repository activity on March 22, consistent with the attacker’s earlier techniques. The company stated that the incident is no longer viewed as a contained breach but rather an “ongoing and evolving attack,” with evidence suggesting the threat actor reestablished access after initial remediation efforts.
To support the response, Aqua engaged incident response firm Sygnia to assist with forensic analysis and containment. The team is now focused on identifying and closing all remaining access paths, after earlier credential rotations were found to be incomplete, allowing the attacker to maintain a foothold.
The incident was first disclosed on March 19, when attackers used compromised credentials to tamper with GitHub repositories and release pipelines. The attackers force-pushed malicious commits to dozens of version tags in the aquasecurity/trivy-action and setup-trivy repositories, while also publishing a trojanized Trivy binary (v0.69.4). These changes allowed malicious code to be silently executed in CI/CD pipelines that relied on mutable version tags.
Trivy is a widely used open source security scanner designed to detect vulnerabilities, misconfigurations, and secrets in containers and code repositories. Maintained by Aqua Security, a cloud-native security firm headquartered in Boston, it is deeply integrated into automated DevOps workflows, making it a high-value target for supply chain attacks.
The injected payload functioned as an infostealer, harvesting sensitive data such as cloud credentials, API tokens, SSH keys, Kubernetes secrets, and Docker configuration files. Because the malicious code executed before legitimate scanning operations, compromised pipelines continued to appear normal while exfiltrating data to the attacker-controlled infrastructure.
New findings from Socket’s threat research team suggest the campaign has expanded beyond GitHub. Researchers identified additional compromised Trivy Docker images (tags 0.69.5 and 0.69.6) pushed to Docker Hub on March 22 without corresponding GitHub releases. These images contain indicators of compromise linked to the same “TeamPCP” infostealer used earlier, including references to the typosquatted command-and-control domain scan.aquasecurtiy[.]org and exfiltration artifacts such as payload.enc and tpcp.tar.gz.
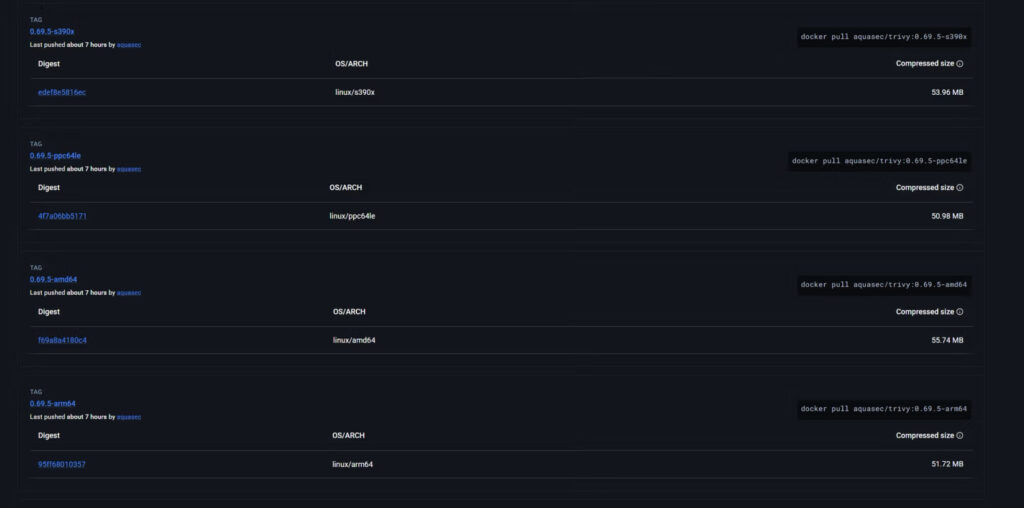
Socket
The appearance of these images, alongside Aqua’s report of renewed malicious activity, reinforces concerns that the attacker retains meaningful access or has established multiple persistence mechanisms. Observations by researcher Paul McCarty suggest there may have also been temporary exposure of internal repositories within Aqua’s GitHub organization, although the full scope remains under investigation.
Security researchers from Aikido Security and CrowdStrike, who previously analyzed the attack, warn that stolen credentials are now being actively weaponized, potentially extending the campaign beyond the initial CI/CD compromise into downstream environments and services.
At present, version 0.69.3 is considered the last known safe Trivy release. Aqua confirmed that its commercial products remain unaffected due to controlled integration processes that isolate them from the open source release pipeline.







Leave a Reply