Russian state-backed threat actors are conducting a large-scale phishing campaign aimed at compromising Signal and WhatsApp accounts belonging to government officials, journalists, and military personnel.
The warning was published by the Netherlands Defense Intelligence and Security Service (MIVD) and the General Intelligence and Security Service (AIVD), which say the activity forms part of a global effort to access communications of individuals of interest to the Russian government.
According to the advisory, the attackers primarily rely on phishing and social engineering rather than on malware or vulnerabilities in the messaging platforms themselves. Dutch government employees have already been both targeted and successfully compromised in the campaign, and the agencies believe journalists and other high-value individuals are also likely targets.
The Dutch services describe two main techniques used in the campaign: account takeover via phishing and abuse of linked-device functionality. These are the same techniques German authorities warned about in a similar bulletin in February.
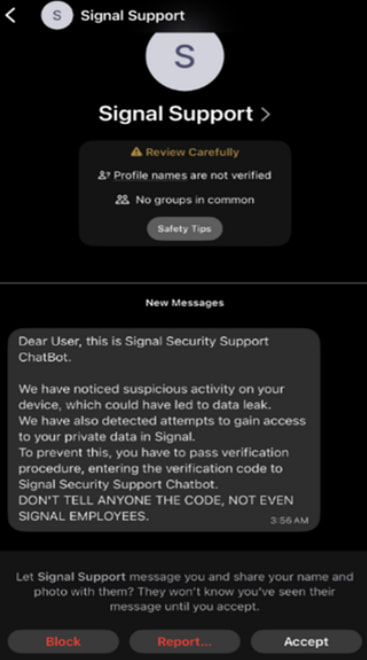
In the first scenario, attackers impersonate customer support representatives or automated security bots from the messaging platforms. Victims receive a message claiming suspicious activity has been detected on their account and are urged to complete a verification process.
During this process, the attacker requests the SMS verification code generated when they attempt to register the victim’s phone number on a new device. Victims may also be asked for their Signal PIN, which can bypass the app’s Registration Lock security feature.
Once the code and PIN are obtained, attackers can take full control of the account, reassign it to a phone number under their control, and gain access to contacts and incoming messages. They may also impersonate the victim in conversations or group chats.
Victims may not immediately realize their account has been hijacked. Because Signal stores chat history locally on the device, re-registering the app can restore past conversations, potentially creating the false impression that nothing has happened.
aivd.nl
The second technique abuses QR codes and “linked devices” features present in both Signal and WhatsApp. Attackers send malicious QR codes or links disguised as invitations to join group chats or connect with a contact. If the victim scans the code, the attacker’s device becomes linked to the account, allowing them to read messages, view chat history, and send messages as the victim while the legitimate user still retains access.
Signal’s response
Signal confirmed it is aware of targeted phishing attacks that have resulted in account takeovers of some users, including government officials and journalists.
In a statement posted on X, the company said its encryption and infrastructure remain secure and were not breached.
“Signal’s encryption and infrastructure have not been compromised and remain robust,” the company said, adding that the incidents stem from “sophisticated phishing campaigns designed to trick users into sharing information – SMS codes and/or Signal PIN – to gain access to users’ accounts.”
Signal also warned users that its support team will never contact them through in-app messages, SMS, or social media to request verification codes or account PINs.
Meta, which operates WhatsApp, had not issued a public statement about the campaign at the time of publication.






Leave a Reply