
Mullvad has published the results of an independent security audit of GotaTun, its Rust-based implementation of the WireGuard VPN protocol, confirming that no major vulnerabilities were discovered.
The review identified two low-severity issues and several minor notes, most of which have already been addressed in newer releases.
The audit was conducted by Swedish cybersecurity firm Assured Security Consultants between January 19 and February 15, 2026. The researchers performed a source code review and limited testing of GotaTun version 0.2.0, focusing on the core library while excluding the command-line interface, Mullvad’s DAITA functionality, and most external dependencies.
According to the auditors, the assessment uncovered no critical, high, or medium-severity vulnerabilities; the findings consisted of two low-risk issues and nine informational notes.
Mullvad’s push toward Rust
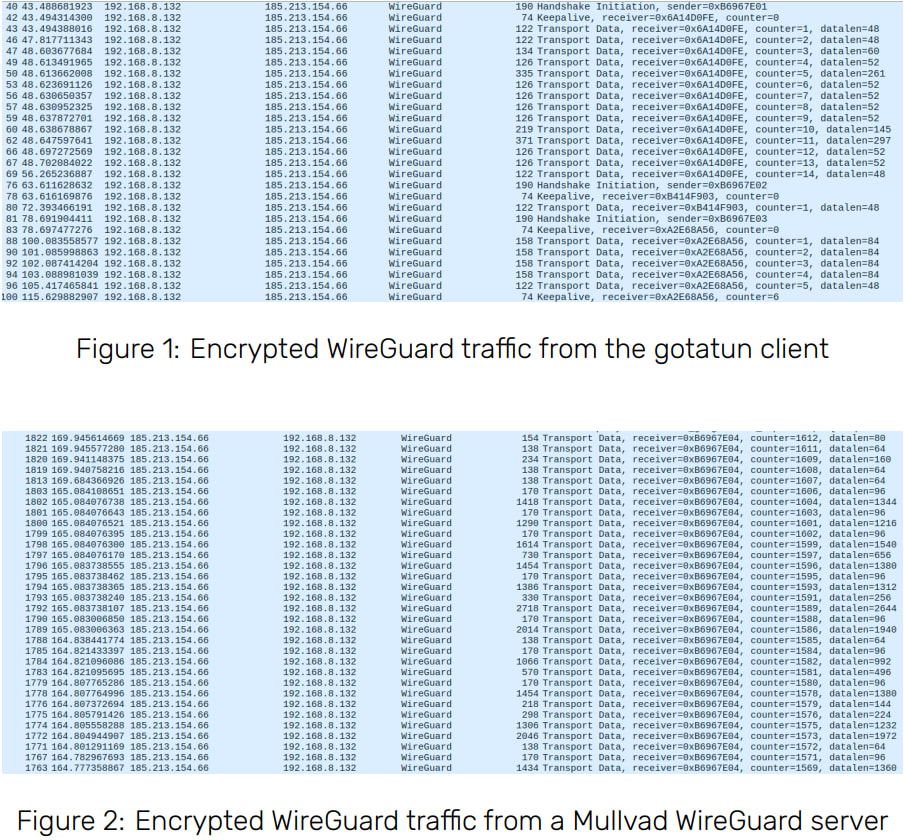
GotaTun is Mullvad’s custom user-space implementation of the WireGuard tunneling protocol written in Rust. It is based on Cloudflare’s BoringTun but modified to support Mullvad features such as DAITA (Device-Aware IP Traffic Allocation) and multihop routing.
The project was introduced in late 2025 as part of Mullvad’s broader effort to replace the legacy Go-based implementation, wireguard-go, which had been responsible for most crash reports in the company’s Android VPN client. Mullvad reported that switching to the Rust-based implementation significantly improved stability and performance in testing.
The privacy-focused VPN provider, headquartered in Gothenburg, Sweden, is known for its strict no-logs policy and for publishing much of its software as open source. GotaTun currently powers the Android version of Mullvad’s VPN client, with a rollout to additional platforms planned for 2026.
Low-severity deviations from WireGuard
The audit highlighted two issues rated as low severity, both related to deviations from the official WireGuard specification.
The first involved the way GotaTun generated session identifiers for peers. Instead of using a fully random 32-bit value, the implementation used a 24-bit Linear Feedback Shift Register (LFSR) combined with an 8-bit counter, a method inherited from BoringTun. While this design did not weaken encryption, auditors noted it could reveal limited metadata to a passive observer, such as the approximate number of handshake events or the number of active peers.
The second issue concerned packet padding. WireGuard’s specification recommends padding encrypted packets so their lengths are divisible by 16 bytes, which can slightly complicate traffic analysis. GotaTun initially skipped this padding step, though auditors noted it was not a significant cryptographic weakness.
Assured
Mullvad has since corrected both issues, aligning GotaTun with the WireGuard specification starting with version 0.3.0.
Additional notes
Beyond the two low-risk findings, the auditors recorded several informational observations about the codebase and its dependencies.
Among them were recommendations to improve peer roaming behavior, simplify the packet buffer implementation, and consider additional memory protections for sensitive data such as encryption keys. The review also pointed out that certain dependencies, such as the Rust cryptography crate ring and the tun networking library, are maintained by small teams or individual developers, which could increase long-term supply-chain risk.
Other notes included a vulnerability discovered during the audit period in the bytes crate (CVE-2026-25541), though auditors confirmed it could not be triggered in GotaTun. Mullvad still upgraded the dependency as a precaution.
Fixes already implemented
Mullvad states that most of the audit’s recommendations have already been implemented in subsequent releases, including patches for the two low-severity issues and improvements to buffer management and dependency versions. Additional fixes, such as improved endpoint handling for roaming clients, were included in GotaTun version 0.4.0.
The company says its applications will automatically adopt the updated implementation in future releases as the rollout continues across platforms.
With the audit completed and major issues ruled out, Mullvad plans to expand GotaTun beyond Android and eventually deploy the implementation across all of its VPN clients during 2026.







Leave a Reply