A security researcher has publicly released proof-of-concept exploit code for a previously undisclosed Windows zero-day vulnerability.
The flaw, dubbed “BlueHammer,” enables local privilege escalation (LPE) and has been confirmed to work in real-world tests, albeit not 100% reliably.
The disclosure was made earlier this week by a researcher using the alias “Nightmare-Eclipse,” who published a blog post and a GitHub repository containing exploit code. The tone of the disclosure suggests frustration with Microsoft’s Security Response Center (MSRC), with the researcher explicitly stating the release was intentional and criticizing the company’s handling of vulnerability reports. The blog post offered no technical breakdown of the flaw, challenging others to reverse engineer the exploit independently.
The GitHub repository contains a Visual Studio project with multiple source files. The project appears to weaponize Windows Defender-related interfaces, though the exact vulnerability mechanism isn’t formally documented by the author.
Despite the lack of a technical explanation, the exploit has been independently validated. Security researcher Will Dormann confirmed on Mastodon that the BlueHammer exploit successfully escalates privileges on Windows systems. In his testing, a non-administrative user was able to spawn a command prompt with SYSTEM-level privileges, demonstrating full compromise of the affected machine. Dormann noted that while the exploit is not entirely reliable, it works “well enough” to be considered a credible threat.
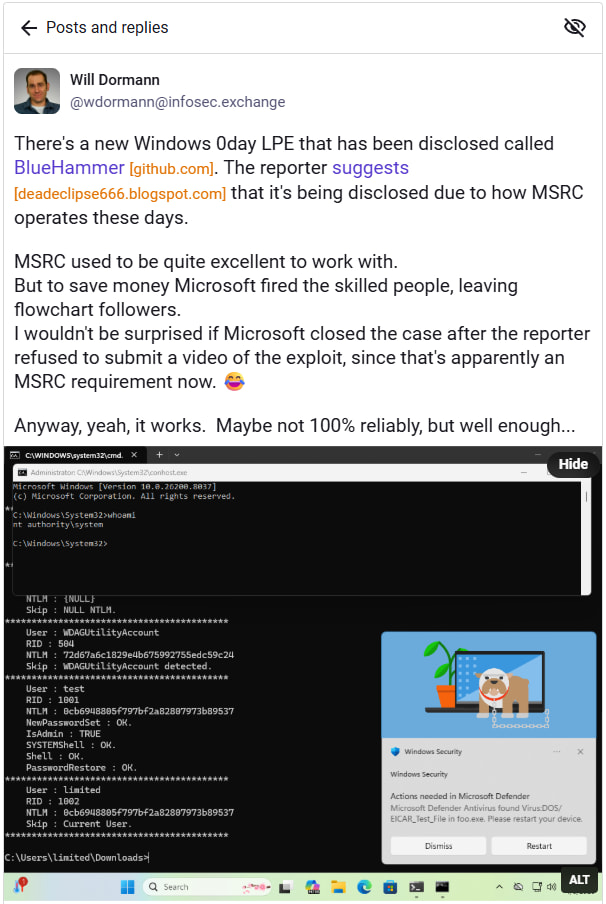
Further discussion among researchers suggests varying behavior depending on the target system. On Windows Server platforms, the exploit appears to elevate a user to administrative privileges rather than full SYSTEM access in some cases. Reports indicate inconsistent success rates across different versions, including Windows Server 2022 and 2025, hinting at environmental dependencies or instability in the proof-of-concept code.
Dormann speculated that stricter submission requirements, such as mandatory video proof of exploitation, may have contributed to the breakdown in communication.
Microsoft is a leading global technology company whose Windows operating system powers a vast majority of enterprise and consumer PCs worldwide. A local privilege escalation vulnerability in Windows poses a significant risk, as attackers often chain such flaws with initial access vectors like phishing or remote code execution to achieve full system compromise.
Microsoft has not yet publicly acknowledged the vulnerability or issued guidance at the time of writing. At present, there is no official patch or mitigation available for BlueHammer. Given the public availability of exploit code, threat actors could quickly adapt it for use in malware campaigns or post-exploitation frameworks.
Users and administrators are advised to take precautionary steps such as restricting local user access, monitoring systems for suspicious process creation, especially unexpected SYSTEM-level shells, and enabling advanced endpoint protection and behavior-based detection. Unusual interactions with Windows Defender components or registry modifications should also be treated as red flags.






Leave a Reply