Proton Pass password manager has passed an independent security audit conducted by Recurity Labs, that described the product’s overall security posture as “well above par.”
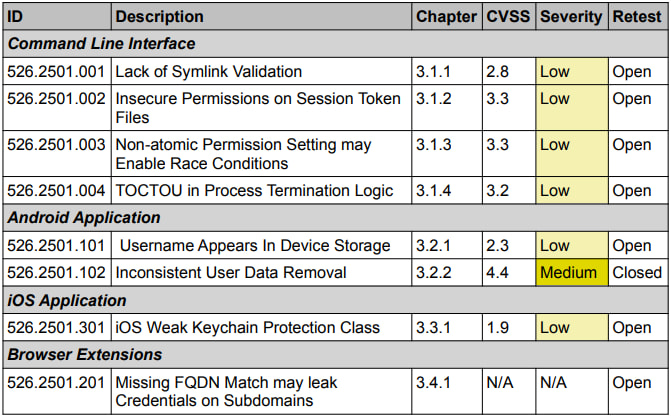
The audit, commissioned by Proton and carried out between January and April 2026, examined the Proton Pass desktop and mobile apps, browser extensions for Chrome, Firefox, and Safari, and the Proton Pass CLI tool. According to the final report, auditors identified mostly low-severity issues and one medium-severity flaw affecting Android data removal, which Proton fixed during retesting.
The audit was conducted by Recurity Labs, an ISO 27001-certified German security consultancy that stated it had no financial or operational conflicts of interest with Proton beyond the assessment engagement itself.
Recurity Labs found no remotely exploitable vulnerabilities, no encryption bypasses, and no evidence that attackers could compromise users simply by visiting malicious websites or clicking harmful links.
Proton is best known for its encrypted email service, Proton Mail, but has expanded into a broader privacy ecosystem that includes VPN, cloud storage, calendar, and password management products. Proton Pass competes with services such as 1Password, Bitwarden, and Dashlane, offering end-to-end encrypted password and identity storage across browsers and mobile devices.
The 57-page audit report from Recurity Labs is based on the review of source code for nearly all Proton Pass components and gray-box testing against the production environment.
The most significant issue uncovered involved the Android app’s handling of local data deletion when users signed out and selected the option to remove account data from the device. Recurity Labs found remnants of user-related information persisted in SQLite database and write-ahead log files, creating a potential privacy issue on shared or compromised devices.
Several additional findings were classified as low severity and largely affected the Proton Pass CLI tool. These included insecure file permission handling, race-condition issues, and weaknesses in symlink validation that could, in theory, allow local abuse under specific conditions. Auditors noted that practical exploitation would generally require local access and significant effort.
The Android app was also found to store usernames in plaintext within local storage and logs under certain circumstances, although Recurity Labs noted that exploiting this would require root-level device access. Proton addressed the logging portion of the issue during remediation efforts, but plaintext usernames in local database storage remained unresolved at the time of the final report.
On iOS, auditors identified a low-severity issue involving weaker-than-ideal Keychain protection classes. Proton reportedly developed a fix but decided not to deploy it because of concerns that the change could introduce stability risks.
The browser extension audit uncovered a credential autofill behavior in which saved credentials were still suggested across related subdomains because strict fully qualified domain name matching was not enforced. Recurity Labs noted that similar behavior is common among password managers as a usability tradeoff, and no direct exploit chain was demonstrated.
Recurity Labs
Despite unresolved low-severity issues, Recurity Labs praised Proton’s response to the findings, particularly the company’s decision to improve memory-handling protections, even though those areas initially fell outside the defined threat model.
As with most security audits, the report does not guarantee the absence of vulnerabilities in the product, and several low-risk findings remain technically open. Users can further reduce their exposure by enabling multi-factor authentication on their Proton accounts, keeping devices updated, avoiding rooted or jailbroken phones, and promptly installing Proton Pass updates as remediation patches continue rolling out.







Leave a Reply