
Microsoft has released the May 2026 Patch Tuesday updates for Windows 11, fixing 97 security vulnerabilities across the Windows ecosystem.
This month’s updates include fixes spanning Windows components, Microsoft Office, Azure services, SQL Server, SharePoint, Hyper-V, .NET, and multiple cloud platforms. Microsoft says none of the flaws were publicly disclosed or actively exploited before patches became available, but several bugs received critical severity ratings, while others were assessed as being more likely to be exploited.
The updates were released as part of KB5089549 for Windows 11 versions 24H2 and 25H2, bringing systems to builds 26100.8457 and 26200.8457. In addition to security fixes, Microsoft also addressed reliability problems with Secure Boot and BitLocker recovery introduced by earlier updates.
Among the most severe vulnerabilities patched this month is CVE-2026-32169, a critical Azure Cloud Shell elevation-of-privilege flaw with a maximum CVSS score of 10.0. Microsoft says the issue stems from a server-side request forgery (SSRF) vulnerability that could allow an unauthenticated attacker to elevate privileges over a network without user interaction.
Azure Cloud Shell is Microsoft’s browser-based command-line environment used by administrators and developers to manage Azure resources. The service is widely used in enterprise cloud environments.
Microsoft also fixed CVE-2026-21536, a critical remote code execution bug in the Microsoft Devices Pricing Program. The flaw carries a CVSS score of 9.8 and is caused by unrestricted upload of dangerous file types. Successful exploitation could allow attackers to execute arbitrary code remotely without authentication.
Two additional critical vulnerabilities, CVE-2026-32191 and CVE-2026-32194, impact Microsoft Bing Images and also received CVSS scores of 9.8. According to Microsoft, both issues are command injection vulnerabilities that could allow remote code execution over a network. Exploiting the vulnerabilities requires no authentication or user interaction.
Several important Windows privilege escalation flaws were also patched this month, including vulnerabilities in the Windows Kernel, Winlogon, SMB Server, ATBroker.exe, and the Ancillary Function Driver for WinSock. Microsoft flagged some of these, including CVE-2026-24289, CVE-2026-24291, CVE-2026-24294, CVE-2026-25187, and CVE-2026-26132, as “Exploitation More Likely.”
The Patch Tuesday release also addresses multiple remote code execution bugs in Microsoft Office and Excel, including CVE-2026-26107 through CVE-2026-26113, as well as SharePoint flaws that could allow attackers to compromise enterprise collaboration servers.
In addition to the security fixes, Microsoft used this month’s release to warn users about upcoming Secure Boot certificate expirations beginning in June 2026. The company says devices that do not receive updated certificates in time could encounter Secure Boot problems. To reduce disruption risks, Microsoft added expanded device targeting for automatic Secure Boot certificate delivery in this update.
The update also resolves an issue where some systems entered BitLocker recovery after installing the April 2026 updates on devices with certain TPM and PCR7 validation configurations. Microsoft says boot reliability has now been improved to prevent unnecessary recovery prompts after boot file updates.
Microsoft is not currently aware of any known issues affecting the May 2026 cumulative updates.
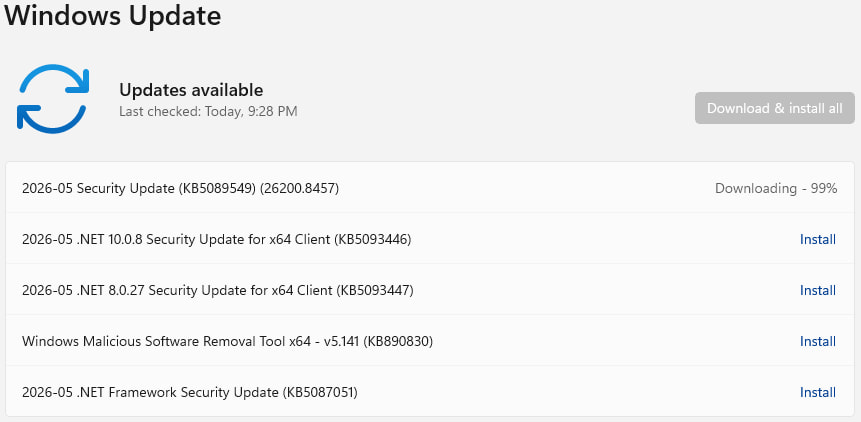
Windows users can install the updates through Settings → Windows Update. A restart will be required for the changes to apply. As always, users are recommended to back up their most important data before applying the update.







Leave a Reply