
Google has released Chrome 148 to the stable channel with one of the largest security update batches in the browser’s history, patching 127 vulnerabilities across Windows, macOS, and Linux systems.
The update includes three critical flaws and dozens of high-severity memory safety bugs affecting core browser components such as Blink, V8, ANGLE, WebRTC, GPU, and Chromoting.
The new versions are Chrome 148.0.7778.96 for Linux and 148.0.7778.96/.97 for Windows and macOS, and the rollout is expected to continue over the coming days and weeks.
Among the most serious issues fixed in this release is CVE-2026-7896, a critical integer overflow vulnerability in Blink, Chrome’s rendering engine. The flaw was reported on March 18 by a security researcher identified as “c6eed09fc8b174b0f3eebedcceb1e792,” who received a $43,000 bug bounty reward from Google. Integer overflow vulnerabilities can lead to memory corruption, which attackers may exploit to achieve arbitrary code execution within the browser process.
Google also addressed two additional critical vulnerabilities: CVE-2026-7897, a use-after-free flaw in Chrome’s mobile-related code, and CVE-2026-7898, another use-after-free bug affecting Chromoting, the remote desktop component used by Chrome Remote Desktop. Both issues were discovered internally by Google researchers in April 2026.
Chrome is the world’s most widely used web browser, powering not only Google Chrome but also other Chromium-based browsers used by hundreds of millions of people globally. Due to the browser’s exposure to untrusted web content, memory corruption vulnerabilities in components like Blink and V8 are considered especially dangerous because they can potentially allow remote attackers to compromise systems simply through malicious webpages.
Several of the high-severity flaws addressed in Chrome 148 also involve memory safety issues commonly associated with browser exploitation chains. These include out-of-bounds read/write bugs in the V8 JavaScript engine, heap buffer overflows in ANGLE, and numerous use-after-free vulnerabilities affecting GPU, Fullscreen, ServiceWorker, SVG, Aura, Skia, Passwords, WebRTC, and other subsystems.
One notable issue is CVE-2026-7899, a high-severity out-of-bounds read/write vulnerability in V8 reported by Project WhatForLunch researchers who earned a $55,000 reward. V8 flaws are particularly valuable to attackers because the engine processes JavaScript from websites and has historically been a frequent target in browser exploitation campaigns.
While Google has not linked the unusually high number of vulnerabilities to AI-assisted auditing, it is notable that most of the reported flaws were discovered internally by Google rather than by external researchers. That pattern mirrors a recent disclosure from Mozilla, which said Anthropic’s Claude Mythos AI system helped uncover 271 previously unknown vulnerabilities in Firefox 150 during large-scale AI-assisted code analysis.
Google has not reported active exploitation for any of the vulnerabilities fixed in Chrome 148, and technical details for many of the flaws remain restricted until most users receive the update.
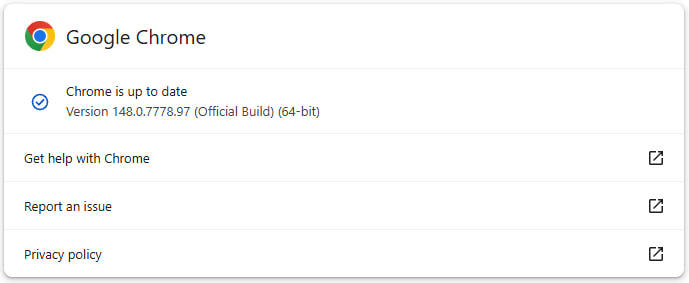
Users are advised to update Chrome immediately by going to Settings → Help → About Google Chrome, which will automatically trigger the update process. Restarting the browser is required to apply the security fixes.







Leave a Reply