
A new malware campaign abuses Microsoft’s Phone Link app to intercept sensitive mobile data, including one-time passwords (OTPs), without compromising the phone itself.
The attack centers on a modular malware toolkit called CloudZ RAT and a previously undocumented plugin for it, named “Pheno,” which enables attackers to monitor synchronized smartphone data directly from a victim’s Windows machine.
The activity, observed by Cisco Talos researchers, has been ongoing since at least January 2026. According to their report, the attackers deploy CloudZ RAT after gaining initial access through an unknown vector, ultimately using it to harvest credentials and intercept authentication data. The campaign relies on the legitimate Microsoft Phone Link application, formerly known as “Your Phone,” as a bridge to access mobile communications indirectly.
Microsoft Phone Link is a built-in Windows 10 and 11 feature that allows users to sync their smartphones with their PCs over Wi-Fi and Bluetooth, mirroring notifications, SMS messages, and call logs. As part of its functionality, the app stores synchronized data locally in SQLite database files such as “PhoneExperiences-*.db.” Attackers exploit this design by targeting the PC-side artifacts rather than the mobile device.
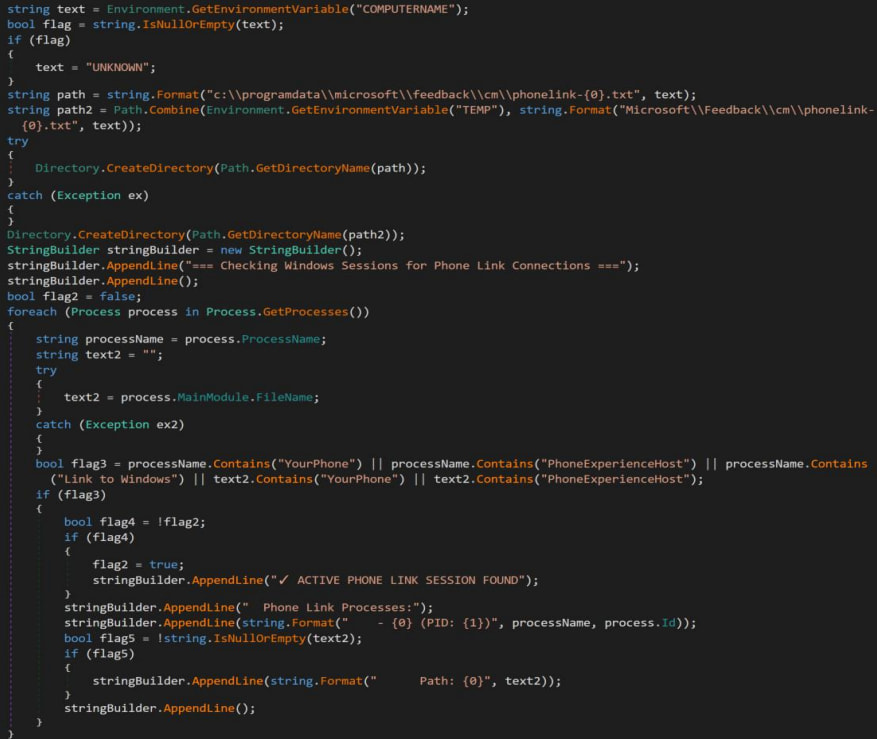
The Pheno plugin continuously scans for active Phone Link processes, specifically looking for indicators like “YourPhone,” “PhoneExperienceHost,” or “Link to Windows.” When detected, it logs process metadata and checks for signs of an active connection, such as the presence of a local proxy used by Phone Link to relay traffic. If a live session is confirmed, the malware flags the system as “Maybe connected,” enabling follow-on data collection.
Cisco
Once a connection is established, CloudZ can access and exfiltrate data from Phone Link’s local database files, potentially capturing SMS messages and OTPs generated by authenticator apps.
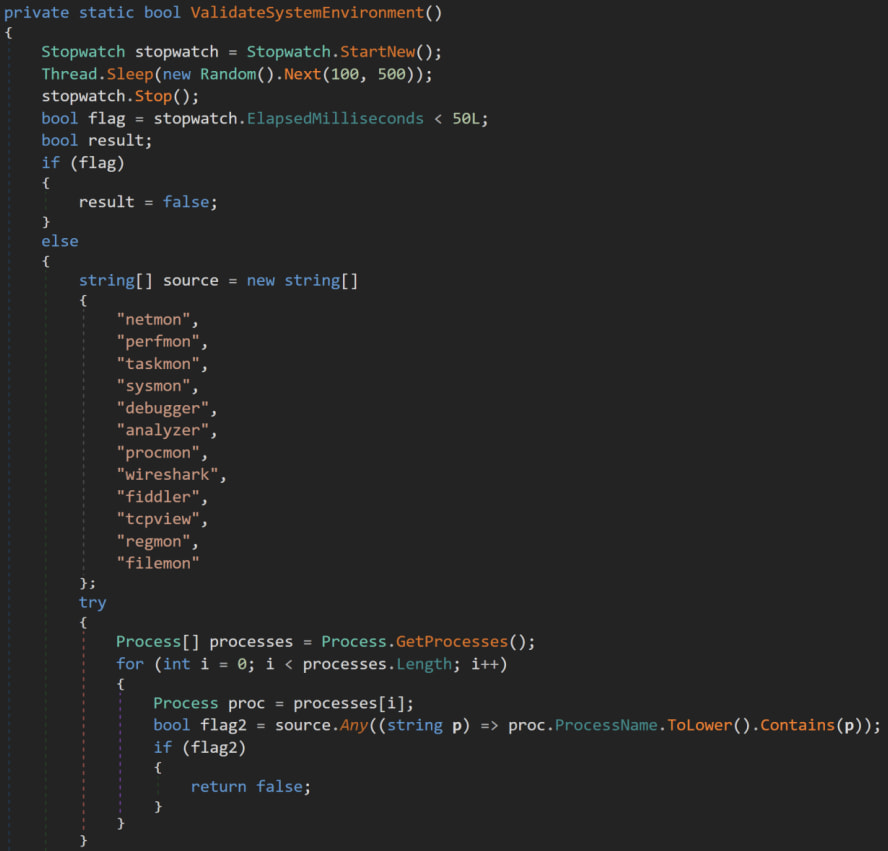
Victims are initially infected via a malicious executable disguised as a ScreenConnect update, which deploys a Rust-based loader. This loader drops a .NET-based secondary payload that establishes persistence using a scheduled task (“SystemWindowsApis”) and executes via the legitimate Windows utility regasm.exe. The final payload, CloudZ RAT, is heavily obfuscated and runs primarily in memory, employing anti-analysis techniques such as sandbox detection, debugger evasion, and dynamic code generation.
Cisco
CloudZ communicates with attacker-controlled infrastructure via encrypted TCP connections and retrieves additional configuration data from services such as Pastebin. It also supports a plugin-based architecture, allowing operators to dynamically extend its capabilities, including deploying the Pheno module for Phone Link reconnaissance and data harvesting.
To mitigate the risk, users should review whether Phone Link is necessary in their environment and disable it if it is not. Additionally, using multi-factor authentication methods that do not rely on SMS, such as hardware tokens or app-based push notifications, can reduce exposure to OTP interception.







Leave a Reply