
Qihoo 360 has inadvertently exposed a production SSL private key inside the installer of its newly launched AI assistant.
The key, which secures the *.myclaw.360.cn domain could allow attackers to impersonate official services and intercept encrypted communications.
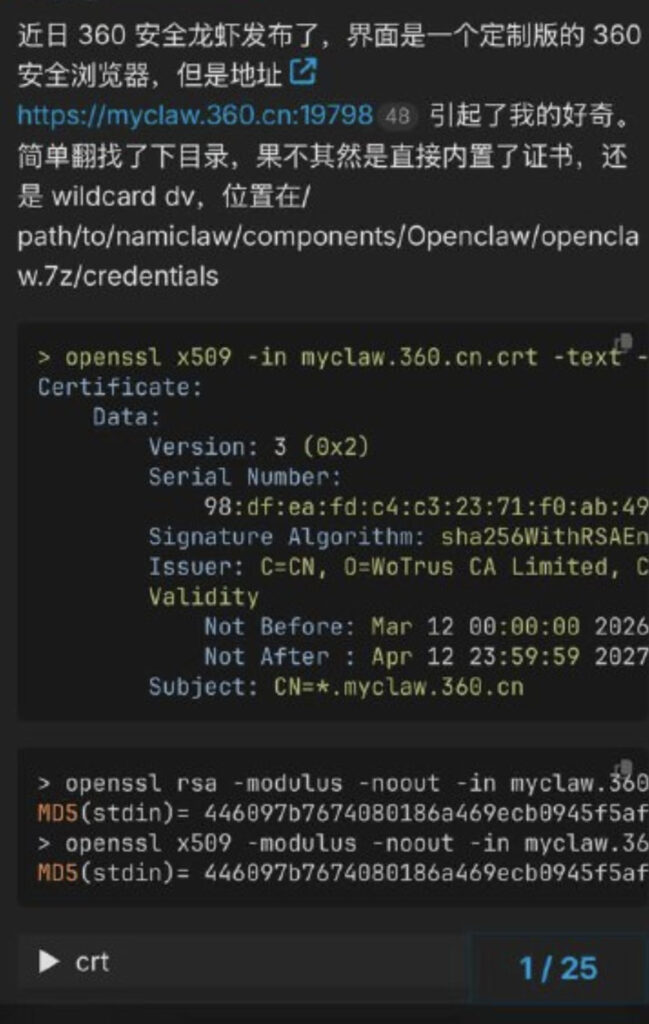
The issue was discovered by security researcher Lukasz Olejnik, who reported finding the private key embedded within the installer package for “360 Security Claw,” an AI-powered tool released by the Chinese cybersecurity firm last week. According to Olejnik, the key was located in the credentials directory of the installer executable (namiclaw.exe), making it accessible to anyone who downloaded the package.
@lukOlejnik
An SSL private key is a critical component of HTTPS encryption, used to authenticate servers and secure communications between users and online services. Exposure of such a key effectively compromises the trust model of the affected domain. In this case, the leaked wildcard certificate, valid until April 2027, covers all subdomains under myclaw.360.cn, significantly broadening the potential attack surface.
With access to the private key, threat actors could carry out man-in-the-middle (MITM) attacks, decrypt intercepted traffic, or create convincing phishing pages that appear to be legitimate Qihoo 360 services. In more advanced scenarios, attackers could potentially manipulate communications between users and the AI assistant itself, undermining both privacy and integrity.
Qihoo 360 is one of China’s largest cybersecurity vendors, often compared to companies like Norton or McAfee, with hundreds of millions of users and a strong presence in endpoint protection and internet security products.
As of writing this, there was no public indication that Qihoo 360 had revoked the exposed certificate or issued a formal response, leaving users potentially vulnerable. The longer the key remains valid and unrevoked, the greater the risk that it could be abused in real-world attacks.
As a precaution, users should avoid interacting with the affected service until the certificate is revoked and replaced. Organizations relying on Qihoo 360 products should monitor for suspicious network activity involving myclaw.360.cn domains and consider implementing certificate pinning or additional verification layers where possible.







Leave a Reply