
The cybercrime group ShinyHunters has announced a new large-scale campaign targeting organizations using Salesforce Experience Cloud sites.
The cybercriminals warned that “several hundreds of companies” could face public data leaks if they fail to respond to extortion demands.
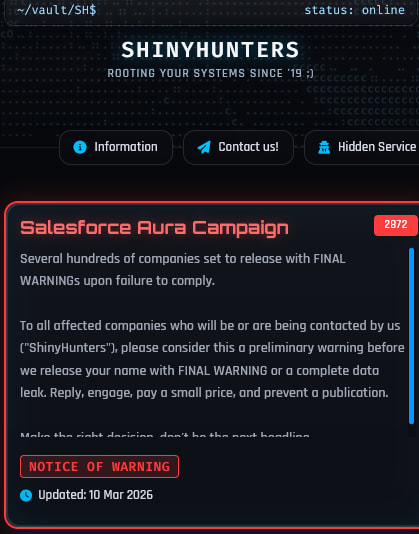
A screenshot from the group’s data leak portal shows a new listing titled “Salesforce Aura Campaign,” claiming the attackers are preparing to release stolen data from numerous affected organizations. The post instructs affected organizations to respond to the attackers, negotiate payment, or risk public exposure of allegedly stolen data.
“Please consider this a preliminary warning before we release your name with FINAL WARNING or a complete data leak,” reads the hackers’ message on their dark web site.
While the attackers do not explicitly describe the intrusion method in their announcement, the campaign appears to align with a recently disclosed threat activity reported by Salesforce.
In a security bulletin, Salesforce warned that threat actors are exploiting misconfigured Experience Cloud guest user permissions on publicly accessible sites.
According to the company, attackers are:
- Mass-scanning Experience Cloud websites
- Targeting the /s/sfsites/aura endpoint
- Using a modified version of the Aura Inspector tool to extract exposed data
The issue does not stem from a vulnerability in the Salesforce platform, the company said. Instead, it arises when organizations grant excessive permissions to the shared guest user profile used by anonymous visitors.
If misconfigured, the guest account can allow unauthenticated users to query Salesforce CRM objects and retrieve data that organizations did not intend to expose publicly.
Salesforce warned that threat actors are performing large-scale automated scanning of these endpoints to harvest data, including names, phone numbers, and CRM records. This data is often used for targeted social engineering campaigns, including vishing attacks.
The company advised customers to immediately audit guest user permissions, disable public API access for guest profiles, and ensure object permissions follow a least-privilege model.
ShinyHunters is a well-known cybercrime group linked to multiple high-profile data breaches and extortion operations in recent years. The group typically publishes stolen data on leak sites and pressures victims into paying to prevent disclosure.
The new “Salesforce Aura Campaign” announcement suggests the group may be attempting to monetize data obtained from misconfigured Salesforce environments across multiple organizations.
At the time of writing, the attackers have not yet publicly named specific victims, but in a communication with CyberInsider, they promised to share more details soon. We will add an update to this post with new info as it becomes available.
Article Update 3:45 PM EST –
ShinyHunters told CyberInsider that the Salesforce Aura Campaign has impacted 400 companies, 100 of which are “essential high profile” firms.
The threat group has stolen data from these entities which it will leak publicly in the following days.
Additionally, ShinyHunters told us that they are exploiting a flaw in the product, so this is allegedly not just a matter of misconfiguration, as portraited in Salesforce's advisory. However, they have decided not to disclose any details about the flaw until the exploitation phase is over.







Leave a Reply