
A covert cyber-espionage campaign targets global telecommunications providers where attackers deploy an advanced Linux backdoor called BPFdoor to maintain long-term, nearly invisible access.
The operation is attributed to a China-linked threat group known as Red Menshen.
The findings come from a months-long investigation conducted by Rapid7 Labs. According to the report, the attackers are not conducting quick intrusions but instead embedding persistent “sleeper cells” deep within telecom infrastructure, allowing them to quietly monitor sensitive communications over extended periods.
Stealth foothold in telecom networks
BPFdoor, an earlier variant of which was previously found in South Korean firm SK Telecom, operates at the kernel level, making it significantly harder to detect than conventional malware. Instead of opening a network port or regularly contacting a command server, the backdoor passively monitors network traffic using Berkeley Packet Filter (BPF) technology.
It activates only when it receives a specially crafted “magic” packet. This means compromised systems can appear completely normal to administrators and security tools, even during active surveillance.
This technique allows attackers to bypass many traditional detection methods, including endpoint monitoring and network scanning tools.
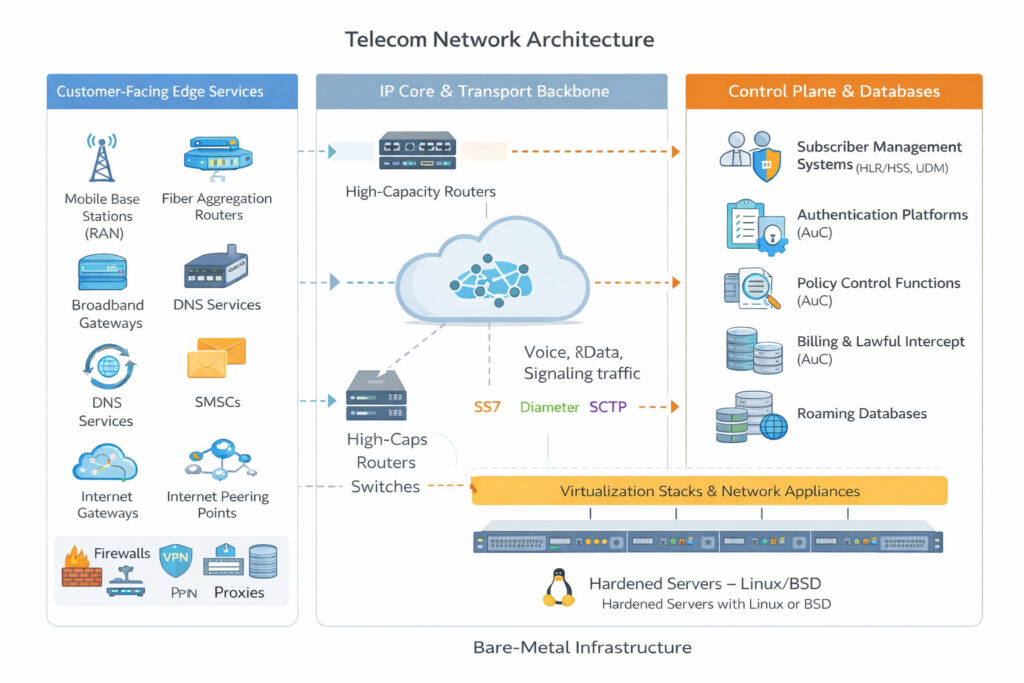
Telecommunications providers form the backbone of global digital communications, carrying voice calls, messages, and internet traffic for billions of users. Their infrastructure includes routing systems, subscriber databases, authentication platforms, and signaling protocols such as SS7 and Diameter.
Rapid7
Because of this central role, gaining access to telecom networks offers attackers far more than a typical data breach. According to Rapid7, a successful compromise can provide visibility into subscriber identities, call and message metadata, device location and mobility data, authentication, and signaling traffic.
How BPFdoor attacks unfold
The campaign typically begins at the network edge, where attackers exploit internet-facing systems such as VPN appliances (Ivanti), firewalls (Fortinet, Palo Alto), routers (Cisco, Juniper), and virtualization platforms like VMware ESXi.
Once inside, they deploy a toolkit that includes:
- CrossC2: a Linux-compatible command-and-control framework derived from Cobalt Strike
- TinyShell: a lightweight passive backdoor for long-term persistence
- Credential harvesters and SSH brute-force tools
BPFdoor is then installed deeper in the environment to maintain covert access.
Rapid7 observed that the malware is highly tailored to telecom environments. Some variants mimic legitimate processes found on enterprise hardware, such as HPE ProLiant servers, while others imitate container services, such as Docker, to blend into modern 4G/5G infrastructure.
New variants increase stealth and control
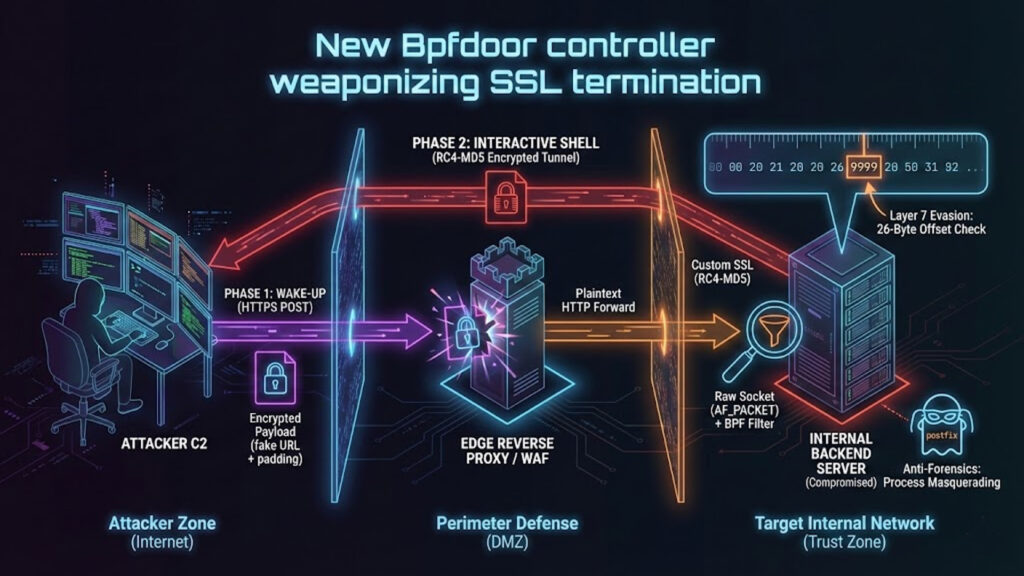
The latest BPFdoor variants introduce several upgrades designed to evade modern defenses.
Notably, the activation trigger is now hidden within normal HTTPS traffic, allowing malicious commands to pass through encrypted connections and security systems before execution. The malware also uses a clever padding technique to ensure its trigger data remains detectable to itself even after passing through proxies or load balancers.
Rapid7
Additionally, Rapid7 identified a new control mechanism using ICMP (ping) traffic, enabling compromised systems to relay commands among themselves without relying on traditional command-and-control servers.
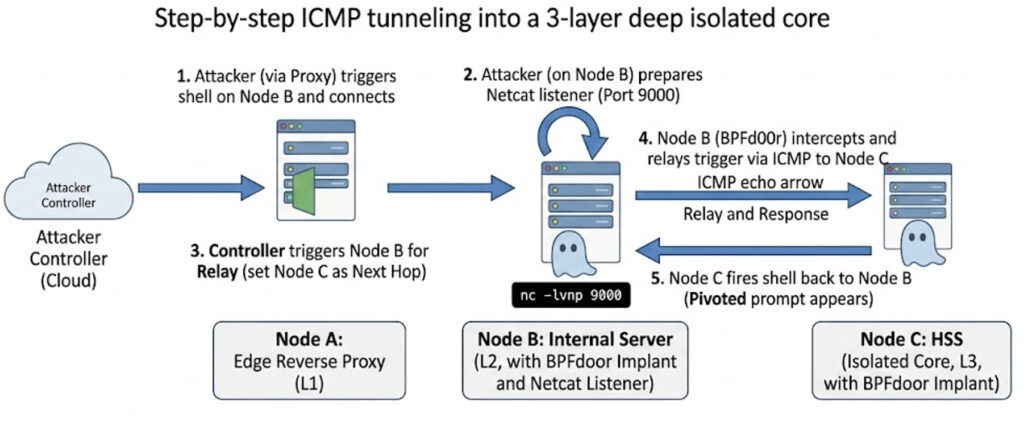
These features effectively turn standard network behavior into a delivery channel for hidden instructions.
Because BPFdoor operates below most visibility layers, many organizations lack the tools needed to detect it. The report highlights that defenders must monitor deeper system activity, including raw socket usage, unusual packet filtering, and suspicious process behavior.
To assist, Rapid7 has released a detection script that identifies known indicators and behavioral patterns associated with BPFdoor infections across Linux systems.







Leave a Reply