
Google’s Threat Intelligence Group (GTIG) has uncovered an advanced iOS exploit kit called “Coruna” that targets Apple iPhones running iOS 13 through iOS 17.2.1 using multiple exploit chains and 23 vulnerabilities.
The toolkit has been used in both targeted espionage operations and financially motivated campaigns.
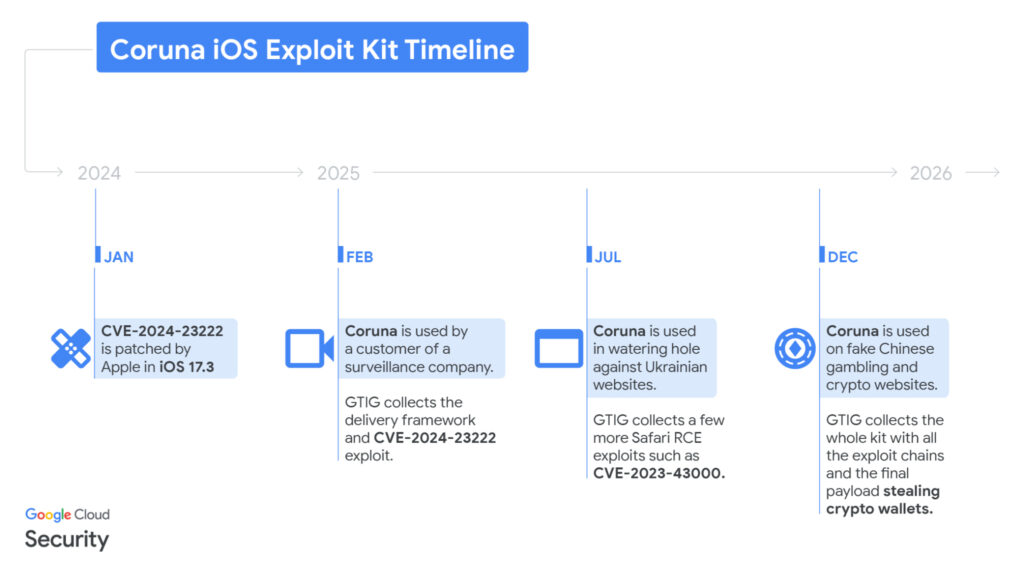
Google first observed parts of the exploit kit in February 2025, when researchers captured an iOS exploit chain used by a customer of a commercial surveillance vendor.
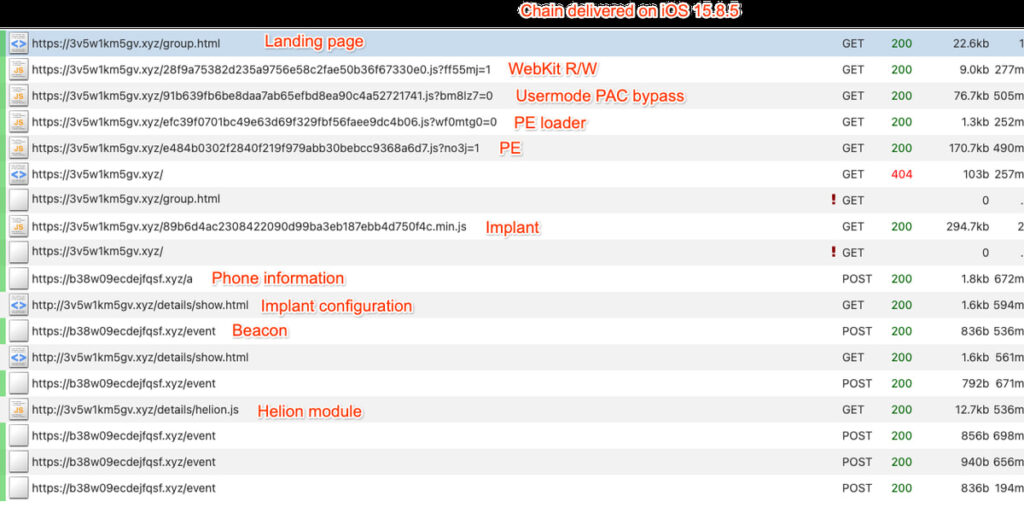
The attack relied on a previously unseen JavaScript framework that used simple obfuscation techniques to encode data. When a victim visited a malicious webpage, the script launched a device fingerprinting routine that collected details such as the device model and iOS version.
Based on this information, the framework delivered a WebKit remote code execution (RCE) exploit, followed by a Pointer Authentication Code (PAC) bypass to advance the attack.
One vulnerability used in these attacks was CVE-2024-23222, a WebKit flaw that Apple patched in iOS 17.3 in January 2024.
Gradually uncovering Coruna
In summer 2025, Google identified the same framework hosted on cdn.uacounter[.]com, which was loaded through hidden iframes embedded in compromised Ukrainian websites.
The exploit was delivered only to selected iPhone users from specific geolocations, suggesting a targeted espionage campaign. The compromised sites included industrial equipment suppliers, e-commerce platforms, and local service websites.
Google attributed the activity to UNC6353, a suspected Russian state-linked threat actor, and worked with CERT-UA to remediate the compromised websites.
Exploit chains observed during this campaign included CVE-2024-23222, CVE-2022-48503, and CVE-2023-43000.
Later in late 2025, GTIG discovered the same framework across a large number of fake Chinese financial and cryptocurrency websites designed to lure victims into visiting them from an iPhone.
These sites displayed prompts encouraging visitors to access them using iOS devices. When opened, a hidden iframe silently delivered the exploit kit.
During this investigation, researchers recovered debug versions of the toolkit, revealing internal exploit names and confirming the platform’s name as Coruna.
The recovered samples allowed Google to reconstruct five complete iOS exploit chains containing 23 exploits, capable of targeting devices running iOS 13 through iOS 17.2.1.
Google attributed the scam campaign to UNC6691, a financially motivated threat actor believed to operate from China.
Exploit framework and malware behavior
The Coruna toolkit includes mechanisms designed to adapt to victim environments and avoid detection. The framework terminates execution if the device is in Lockdown Mode or if the user is browsing in private mode.
Exploit payloads are delivered as files disguised as “.min.js” scripts that actually contain encrypted binary components compressed with LZW and encrypted with ChaCha20.
The exploit chains combine WebKit vulnerabilities, sandbox escapes, kernel privilege escalation exploits, and PPL bypasses to achieve full device compromise. Some vulnerabilities used by Coruna, including Photon and Gallium, were previously linked to Operation Triangulation, the iOS espionage campaign revealed by Kaspersky in 2023.
After exploitation, the attack deploys a loader called PlasmaLoader, tracked by Google as PLASMAGRID, which injects itself into the powerd system daemon.
Unlike traditional spyware implants, the recovered payload focuses primarily on financial theft. The malware scans device data for cryptocurrency wallet information and financial credentials, including BIP39 seed phrases and keywords such as “backup phrase” or “bank account.” It can also decode QR codes stored on the device to extract wallet data.
Additional modules downloaded from command-and-control servers target numerous cryptocurrency wallet applications, including MetaMask, Trust Wallet, Exodus, Phantom, BitKeep, and TokenPocket.
Google says the Coruna exploit kit does not work against the latest versions of iOS, and all identified malicious domains have been added to Google Safe Browsing.
Users are advised to update their devices to the latest iOS version, enable Lockdown Mode, and avoid suspicious websites, particularly cryptocurrency-related platforms.







Leave a Reply