
APT groups are increasingly using AI-assisted development tools to rapidly generate large volumes of malware written in obscure programming languages, allowing them to evade detection by security tools tuned for more common codebases.
The trend was highlighted in a Bitdefender report analyzing recent activity linked to APT36 (Transparent Tribe), a Pakistan-aligned threat group known for targeting Indian government organizations and diplomatic missions. The researchers found that the threat group is producing large volumes of AI-assisted malware samples in languages rarely seen in typical enterprise environments.
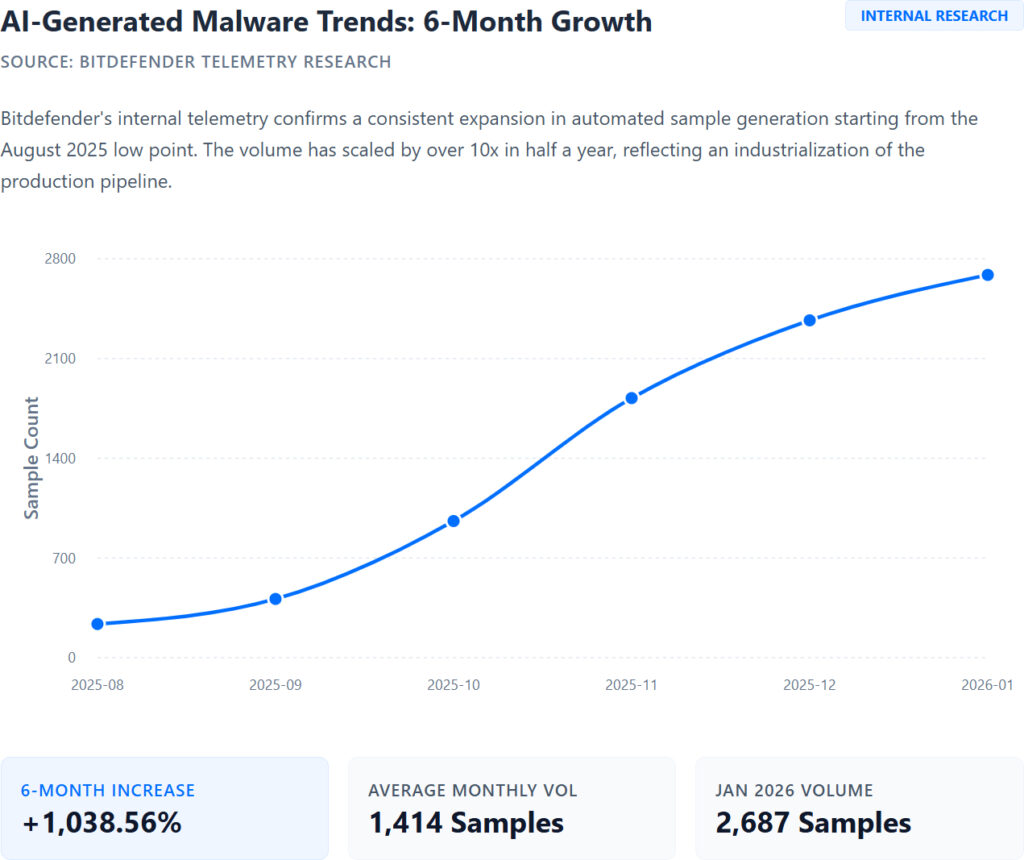
Instead of developing highly sophisticated malware, the operators appear to rely on AI coding tools to rapidly assemble functional, but often flawed, malicious programs. Bitdefender observed the group maintaining a “malware-a-day” pace, generating new variants frequently and deploying multiple implants simultaneously inside compromised environments.
Evasion through uniqueness
Many traditional antivirus and endpoint detection engines are optimized to detect malware developed in common ecosystems such as C++, C#, and .NET. By switching to less common languages, attackers effectively reset the detection baseline.
During the campaign, Bitdefender identified malware written in several languages, including:
- Crystal and Zig, used for cross-platform backdoors
- Nim, acting as a wrapper for legacy payloads like Cobalt Strike beacons
- Rust and Go, used for file harvesting and data exfiltration
These languages allow attackers to generate binaries that appear unfamiliar to some security engines while still implementing well-known malicious behaviors.
The code quality varies significantly. In one example, researchers found a Go-based credential-stealing tool that used a placeholder for a command-and-control server address, rendering it incapable of actually sending stolen data.
Such mistakes suggest the malware was generated quickly using AI-assisted tools rather than carefully engineered by developers.
Blending into trusted services
To further evade detection, the malware relies heavily on “Living Off Trusted Services” (LOTS) techniques for command-and-control. Instead of communicating with attacker-controlled servers, the implants interact with legitimate cloud services that are commonly allowed in corporate networks.
Researchers observed the malware using platforms including:
- Discord and Slack for remote commands
- Google Sheets to store instructions and receive output from infected systems
- Firebase and Supabase databases for data storage and coordination
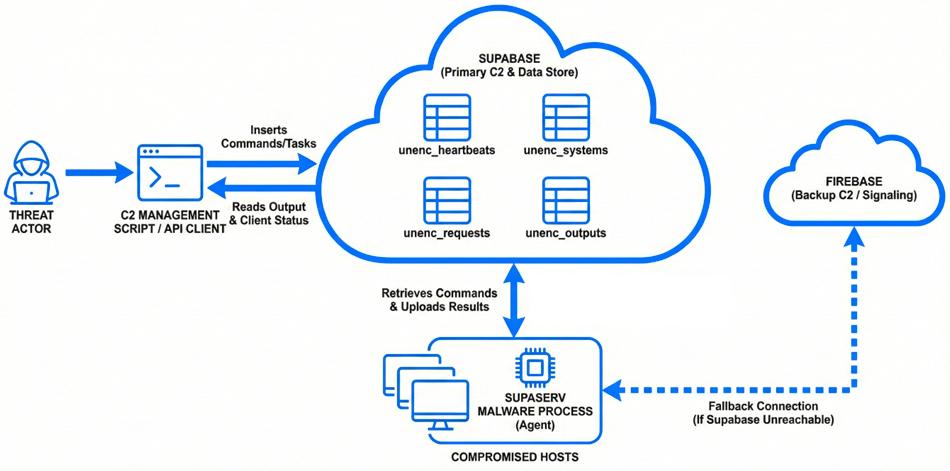
One backdoor, dubbed CrystalShell, uses Discord channels as a command interface, while another component, SheetCreep, converts a Google Sheets spreadsheet into a command-and-control hub.
Because these services are widely trusted and heavily documented, AI tools can easily generate functional integration code for them.
Bitdefender attributes the campaign to APT36 with medium confidence, citing overlaps with previously observed infrastructure and tools used by the group.
The attacks primarily targeted organizations linked to the Indian government and diplomatic missions, though entities in Afghanistan and several private-sector organizations were also affected.
The attackers appear to be seeking sensitive information related to military personnel, diplomatic communications, and national security policies.
Turning up the complexity
While the malware samples are often inconsistent or poorly implemented, researchers warn that the approach still poses a significant risk.
AI models trained on publicly available code repositories can reconstruct and adapt common malicious routines with minimal prompting. This allows attackers to quickly generate large numbers of unique binaries and deploy them simultaneously.
According to Bitdefender, the strategy effectively creates a “distributed denial of detection” scenario where defenders must analyze a constant stream of new variants.







Leave a Reply