
Researchers have demonstrated that standard fiber-optic internet cables can be covertly repurposed into highly sensitive listening devices, capable of capturing speech and tracking human activity inside buildings.
The study shows that, under realistic conditions, attackers could exploit existing telecom infrastructure to recover conversations and other sensitive information without deploying traditional surveillance hardware.
The research, conducted by the Hong Kong Polytechnic University and the Chinese University of Hong Kong, was presented at the NDSS Symposium 2026. The team set out to explore whether optical fibers, widely considered immune to eavesdropping, could leak acoustic information through subtle physical effects.
“Listening” to sounds on the cable
At the core of the attack is the fact that optical fibers, while designed to carry light signals, are also sensitive to minute physical vibrations. Sound waves in the surrounding environment can slightly deform the fiber, causing measurable phase shifts in the light traveling through it. By connecting one end of the fiber to a commercially available Distributed Acoustic Sensing (DAS) system, an attacker can analyze these phase changes and reconstruct the original sound.
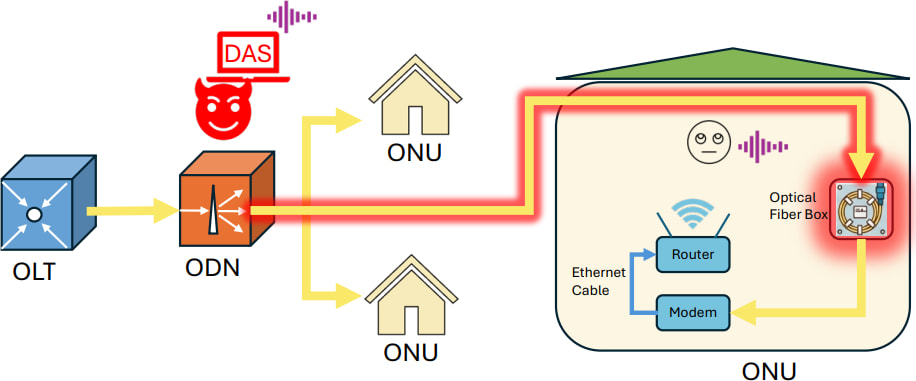
NDSS
The threat becomes particularly relevant in the context of Fiber-to-the-Home (FTTH) deployments, where fiber cables run directly into residential and office environments. These installations often include unused “dark fibers” and excess cable stored in wall boxes, both of which can be repurposed for surveillance. The researchers show that an attacker with access to the network infrastructure, such as a malicious insider or contractor, could tap into a victim’s fiber line from a remote location and begin collecting acoustic data.
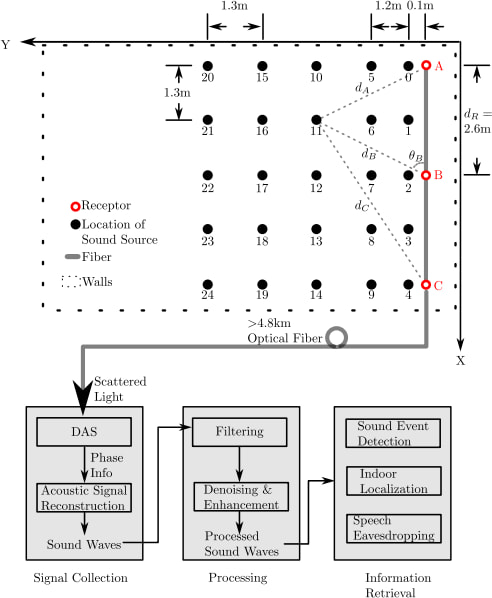
To overcome the natural limitation that bare optical fibers are not very sensitive to airborne sound, the team engineered a “sensory receptor,” a small cylindrical structure around which the fiber is tightly wound. This design amplifies sound-induced vibrations, effectively converting weak air pressure changes into measurable strain along the fiber. The receptor can be disguised as a standard fiber junction box, making the attack difficult to detect during routine inspections.
NDSS
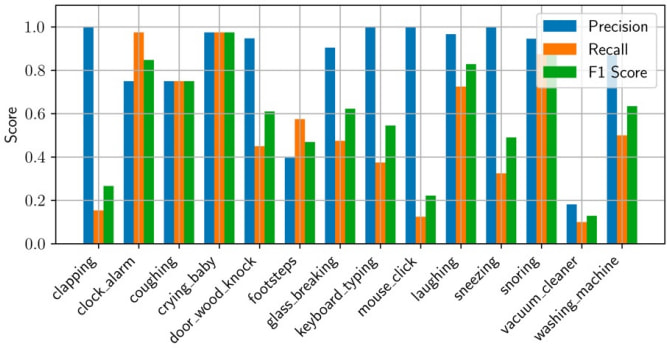
In controlled experiments, the system demonstrated the ability to detect household activities such as typing or coughing, localize sound sources within a room with sub-meter accuracy, and reconstruct speech with notable fidelity. The researchers report that more than 80% of spoken content could be recovered within 2 meters, and that automatic speech recognition systems achieved low word error rates at short range.
NDSS
The study also explored real-world scenarios, including an office setup where two rooms were connected by over 50 meters of fiber. Even in noisy conditions, the system recovered intelligible speech, with performance varying depending on how vibrations were transmitted through surfaces such as desks or walls. Notably, the technique proved resistant to ultrasonic jamming because it relies purely on optical and mechanical effects rather than electronic sensors.
Despite its effectiveness, the attack has practical constraints. Sound quality degrades with distance, background noise near the fiber can significantly reduce accuracy, and the method requires physical access to the fiber infrastructure. However, the researchers argue that in high-value targets such as corporate offices or government facilities, these barriers won’t stop determined attackers.







Leave a Reply