
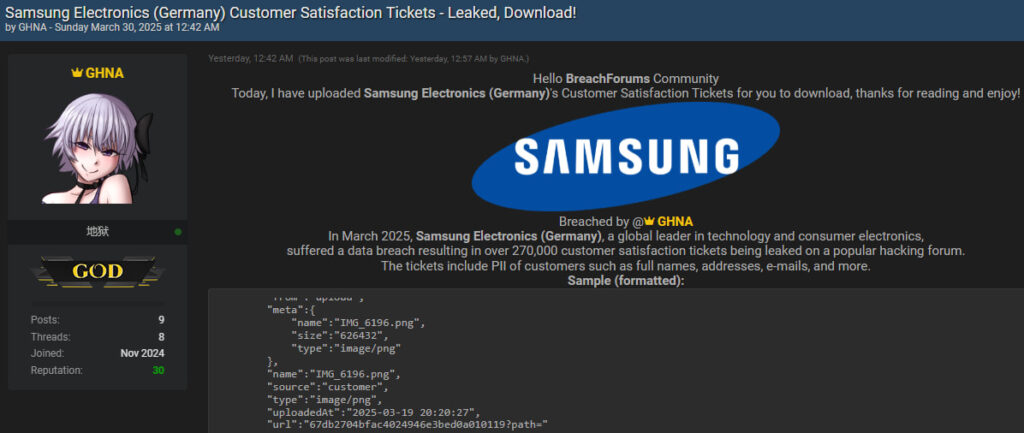
A hacker using the alias “GHNA” has leaked over 270,000 customer service tickets tied to Samsung Electronics Germany, exposing sensitive personal and transactional data.
The dataset, now circulating freely on BreachForums, contains names, addresses, emails, order details, and internal communications, all tied to Samsung's customer satisfaction portal.
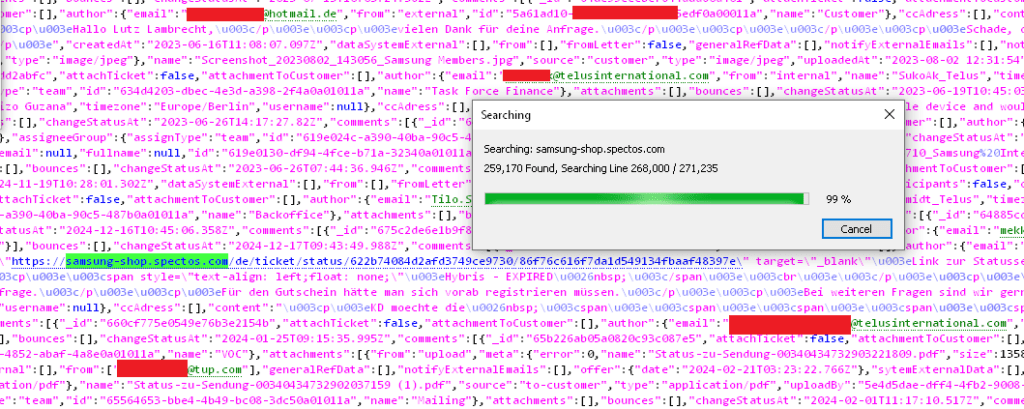
Cybercrime intelligence firm Hudson Rock has linked the incident to stolen credentials obtained via an infostealer infection dating back to 2021. According to Hudson Rock's analysis, the credentials were harvested from a machine belonging to an employee of Spectos GmbH, a German firm managing customer experience platforms, including Samsung Germany's service ticketing system at samsung-shop.spectos.com.
The compromised credentials — left unchanged for years — provided GHNA with administrative access to the backend of Samsung's ticketing platform. This allowed the attacker to extract a comprehensive archive of customer interactions, mostly from the year 2025.
Samsung Electronics is one of the world's largest technology firms, operating in consumer electronics, semiconductors, and IT services. Its German division serves one of Europe's most significant markets. Spectos GmbH, the service provider implicated in the breach, partners with large enterprises to monitor and improve customer service quality through data analytics and workflow platforms.
The leaked dataset includes structured JSON records of customer complaints and feedback, often containing:
- Personally Identifiable Information (PII): full names, email addresses, physical addresses, phone numbers, and salutations.
- Transactional metadata: order numbers, model numbers, purchase channels, delivery details, and payment methods.
- Internal data: support agent email addresses, assigned teams, escalation statuses, and internal commentary.
- Attachments: uploaded customer images and documents, including screenshots and delivery confirmations.
According to Hudson Rock, the same credentials used in this breach were present in its Cavalier cybercrime intelligence database for years. The firm noted that the Spectos employee had been infected with the Raccoon Infostealer malware, one of the most common credential-harvesting tools in the wild. Despite this, no apparent action was taken to rotate or revoke the compromised login — leaving the platform vulnerable until GHNA exploited the dormant credentials in 2025.
Hudson Rock
The stolen data are not being sold but distributed freely, dramatically increasing its potential for abuse. The data is already being analyzed and scraped by threat actors for use in phishing campaigns, fake warranty claims, and even physical delivery fraud schemes. Widely available AI tools can now rapidly parse such unstructured data leaks, enabling the automation of sophisticated social engineering and fraud operations at scale.
Samsung has not yet publicly confirmed the breach or responded to our inquiries regarding the validity of the data. However, cross-verification of email addresses, internal communication metadata, and file structures strongly suggest the leak is authentic. The presence of real agent contact details, internal ticket IDs, and high-fidelity order data adds further weight to its legitimacy.
If you have interacted with a Samsung Germany agent or used their customer support services in the past, you should be vigilant for phishing emails referencing past orders or customer service issues.







Leave a Reply