
A new data breach has impacted the Royal Mail Group, with 144GB of sensitive data leaked on March 31, 2025, by a hacker using the alias “GHNA.”
The attack, linked to a long-dormant infostealer infection from 2021, is the second major incident involving Spectos, the same third-party service provider implicated in last week's Samsung Tickets breach.
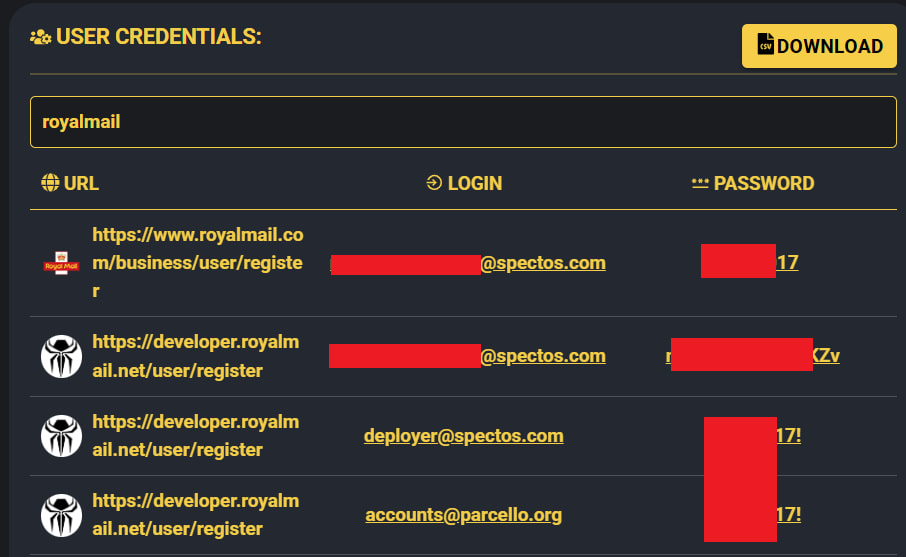
Cybercrime intelligence firm Hudson Rock traced the Royal Mail breach to the same root cause as the Samsung incident: credentials stolen from a Spectos employee infected by an infostealer malware strain in 2021. Despite the infection being four years old, the stolen access remained active and was only recently exploited by GHNA, who published the stolen dataset freely on the popular cybercrime marketplace BreachForums.
The leaked dataset includes highly sensitive personal information including:
- Customer names
- Email addresses
- Physical addresses
- Package weights
- Delivery classes
- Sender information
- Subscriber records from Mailchimp mailing lists
Furthermore, GHNA's post includes internal Zoom video recordings between Royal Mail and Spectos, delivery and postal location data, and the complete SQL database of the WordPress site mailagents.uk.

Royal Mail Group is the United Kingdom's official postal service and one of its oldest institutions, with over five centuries of operational history. It plays a critical role in national communications and logistics, managing postal deliveries across the UK and abroad. Given its importance and vast user base, any compromise of its internal data carries significant implications for both customers and operational integrity.
The attacker's use of legacy credentials points again to the neglected risk posed by third-party access and long-standing credential leaks. In both this breach and the Samsung incident, GHNA exploited credentials harvested from a 2021 infostealer infection — identified by Hudson Rock as Raccoon Infostealer — which remained active due to inaction on Spectos' part. The malware, designed to silently exfiltrate credentials and browser data, allowed GHNA to access sensitive back-end systems years after the initial compromise.
A screenshot from Hudson Rock's Cavalier platform shows the Spectos employee's credentials indexed and exposed in the cybercrime underground for years before being operationalized in these recent attacks.
The breach raises broader concerns about supply chain security and the dangers of third-party integrations. Spectos, a German analytics provider that supports logistics and customer service systems for large enterprises, has now been at the center of two high-profile leaks in less than a week. The firm has not publicly addressed the recurring credential issue, and Royal Mail has yet to respond to GHNA's allegations. CyberInsider reached out to Royal Mail Group for comment but has not received a response at the time of publication.
Article Update – Royal Mail sent CyberInsider the below comment after the publication of this article:
We are aware of an incident which is alleged to have affected Spectos, a supplier of Royal Mail. We are working with the company to investigate the issue and establish what impact there may be regarding their data. We can confirm there has been no impact on Royal Mail operations and services continue to function as normal. – Royal Mail spokesperson.







Leave a Reply