Oracle has confirmed a significant data breach involving the theft of legacy client login credentials, marking its second acknowledged security incident in recent weeks.
After previously denying that any compromise had occurred within its cloud infrastructure, the company is now reportedly informing select customers of an intrusion that impacted outdated systems—some of which reportedly contained data as recent as 2024.
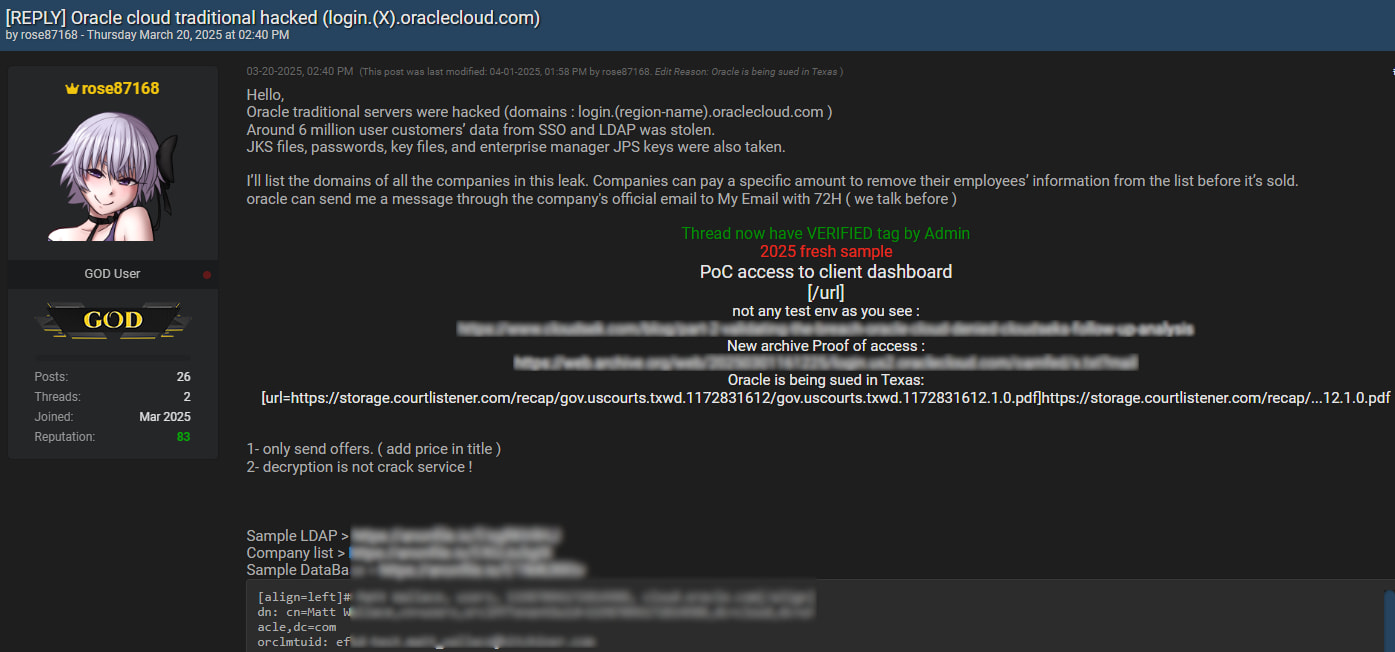
The breach was first brought to public attention in March 2025, when a threat actor using the alias “rose87168” began selling what they claimed were six million Oracle customer records on BreachForums. Initially, Oracle dismissed the claims via a statement to BleepingComputer, asserting that its Oracle Cloud systems remained uncompromised. However, multiple cybersecurity firms, including Trustwave and CybelAngel, have since validated the authenticity of the leaked data, which includes usernames, encrypted Single Sign-On (SSO) and LDAP credentials, Java Keystore (JKS) files, and enterprise manager JPS keys.
According to individuals briefed on Oracle's internal investigation, the attack targeted a so-called “legacy environment” not used in active services. Despite Oracle's statements that the compromised system was decommissioned eight years ago, a separate source familiar with the breach indicated that some stolen credentials were dated as recently as 2024. This discrepancy raises questions about Oracle's handling of legacy data retention and internal system segmentation.
The attack appears to have originated from a vulnerability in Oracle's Gen 1 cloud infrastructure. A webshell and malware were reportedly deployed to access Oracle's Identity Management (IDM) database, allowing the attacker to exfiltrate sensitive authentication data. CybelAngel reports that the breach likely began in January 2025 via exploitation of a known Java vulnerability, and that Oracle became aware of suspicious activity in February, shortly before the first ransom demand in early March.
Oracle Corporation, a global leader in enterprise software and cloud computing, serves thousands of customers across sectors, including finance, government, and healthcare. The firm is headquartered in Austin, Texas, and operates one of the largest cloud infrastructure platforms in the world. Its legacy Gen 1 servers, which were superseded by Gen 2 architecture, reportedly lacked many of the security hardening measures present in modern deployments.
The attacker, “rose87168,” surfaced publicly on March 5, 2025, and has since demanded a ransom of $20 million. The threat actor has also shown a willingness to barter stolen data in exchange for zero-day exploits — suggesting motivations beyond simple financial extortion. Samples of the data shared online included proof of access to Oracle Cloud subdomains, though Oracle continues to insist there was no breach of the Gen 2 cloud systems.
CyberInsider
The FBI and CrowdStrike are currently investigating the intrusion. While Oracle has not publicly commented beyond customer communications, internal notifications have acknowledged that the exposed data — although partially outdated — could facilitate phishing campaigns or account takeover attempts.
This incident follows a separate, unrelated breach involving Oracle's patient records management software, which came to light in late March. In that case, threat actors accessed patient data held by healthcare providers and attempted to extort them individually.






Leave a Reply