
A new advisory by CISA warns that a stealthy technique known as “fast flux” is being widely used by cybercriminals and nation-state actors to evade detection, sustain attacks, and resist takedowns — posing a growing threat to national security and enterprise networks alike.
The joint alert from CISA, NSA, FBI, and their international counterparts urges internet service providers (ISPs), cybersecurity vendors, and Protective DNS (PDNS) services to urgently enhance their ability to detect and block malicious infrastructure leveraging fast flux.
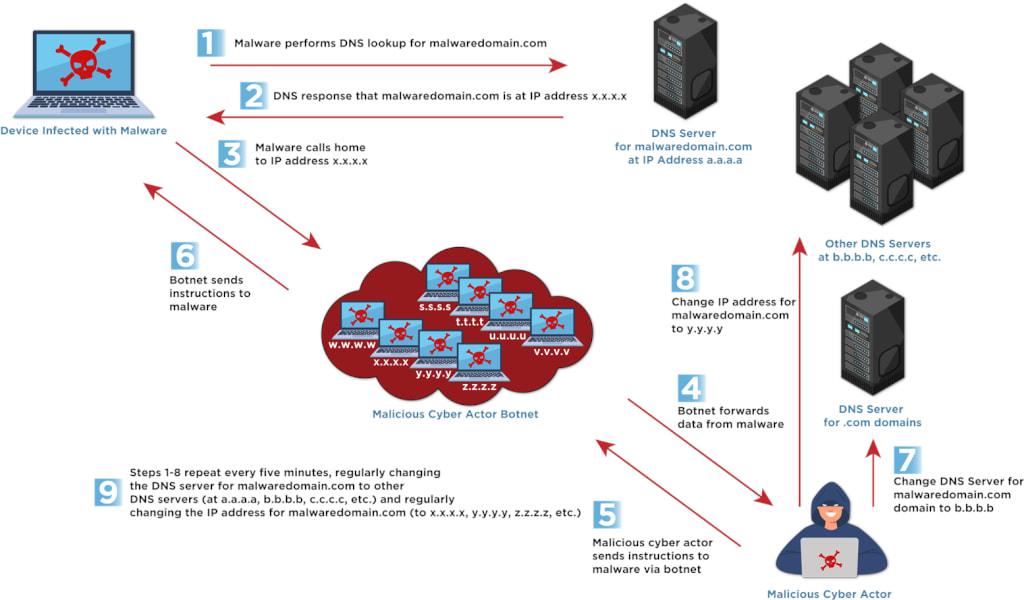
The technique involves rapidly rotating the IP addresses or even the name servers tied to malicious domains, making it significantly harder for defenders to trace, block, or dismantle the underlying infrastructure.
Fast flux is not a new tactic, but it remains a notoriously difficult challenge to contain — and many modern defenses are still unequipped to detect it reliably. By using this technique, threat actors can maintain persistent command-and-control (C2) channels for malware, keep phishing sites online through takedown attempts, and operate illegal marketplaces behind layers of anonymity.
Two main variants of fast flux are currently observed:
- Single flux, where a domain name rapidly cycles through numerous IP addresses to avoid being blocked.
- Double flux, which adds another layer of complexity by also rotating the DNS name servers associated with the domain.
CISA
These setups often rely on vast botnets made up of compromised devices scattered globally, used to relay traffic and obscure the true source of malicious activity. The result is a resilient, distributed, and nearly untouchable infrastructure.
Fast Flux widely abused by cybercrime
Entities such as Gamaredon, a Russian-linked group, have used fast flux to maintain operational access despite IP blocking efforts. Ransomware operators behind Hive and Nefilim attacks have also adopted the technique. Meanwhile, bulletproof hosting (BPH) providers — services that openly ignore abuse complaints — actively market fast flux as a feature to their criminal clientele. Some even offer tools to shield customer servers from blocklists by routing traffic through disposable “dummy” interfaces.
Fast flux also powers phishing campaigns, enabling malicious websites to remain active even as defenders work to take them down. These sites often aim to harvest login credentials, credit card numbers, or install malware on unsuspecting victims' systems.
Despite its impact, many networks and security services still lack effective detection mechanisms. The advisory recommends that service providers develop behavioral analytics to identify fast flux domains based on patterns like:
- Excessively short DNS time-to-live (TTL) values
- High-frequency IP address changes (sometimes every few minutes)
- Geographic inconsistency in IP address resolution
- Large volumes of DNS traffic with high entropy
To counteract these threats, the advisory recommends a layered defense strategy that includes DNS analysis, real-time network monitoring, threat intelligence feeds, and flow data inspection. Equally critical is collaboration between providers and organizations through information-sharing platforms such as CISA's AIS and ASD's CTIS.
Organizations are also encouraged to block or sinkhole known fast flux domains and IP addresses, use DNS filtering based on domain reputation and monitor network traffic for fast flux-related anomalies.
The advisory stresses that organizations should not assume their PDNS or cybersecurity vendors are already protecting against fast flux. Many do not. Verifying coverage — and demanding improvements — should be an immediate priority.







Leave a Reply