
A rapidly evolving malvertising campaign that originally targeted Windows users through Meta's ad network has expanded its reach to Android devices, pushing an advanced version of the Brokewell malware disguised as a legitimate trading app.
Bitdefender Labs warns that the mobile campaign is now active globally and poses one of the most serious Android malware threats seen to date.
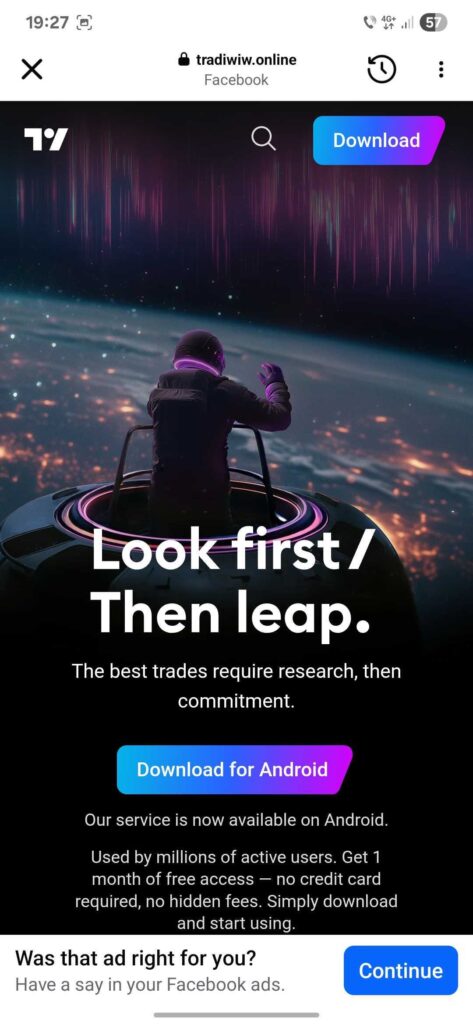
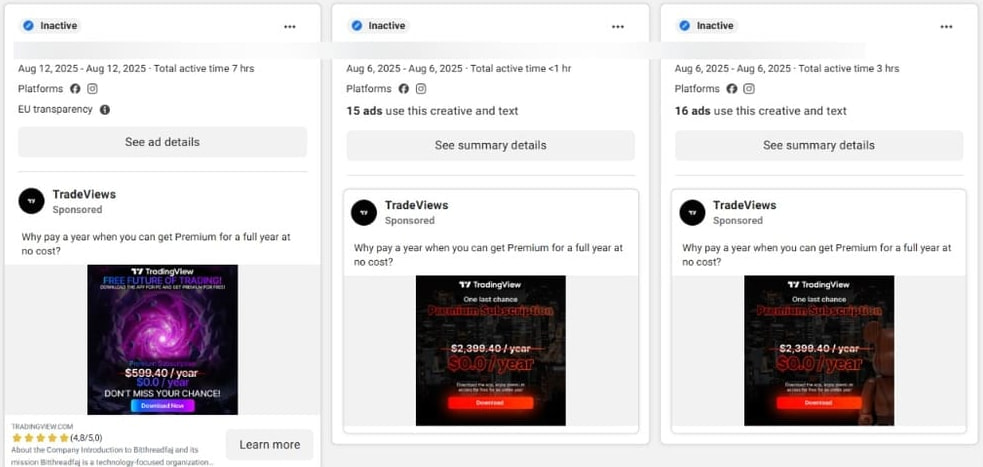
Since July 22, 2025, Bitdefender has identified over 75 malicious Facebook ads targeting Android users, with tens of thousands of impressions reported across the European Union. The malicious ads mimic official TradingView branding and, in some cases, even combine it with culturally specific imagery, such as a Labubu cartoon, to maximize appeal.

Bitdefender
Android users who click these ads are redirected to a phishing page at new-tw-view[.]online, which closely imitates the real TradingView website. From there, victims are tricked into downloading a malicious APK from tradiwiw[.]online/tw-update.apk. The downloaded APK acts as a dropper, installing a secondary payload while masking its activity with fake update prompts.
Bitdefender
The malware requests intrusive permissions, including Accessibility Services, and overlays deceptive messages on popular apps like YouTube to harvest user input. It even prompts for the device's lock screen PIN, enabling further control and unauthorized access.
Brokewell spyware
The dropped malware is a new, enhanced strain of Brokewell, a full-featured Android spyware and remote access trojan (RAT). It is designed for financial theft, device surveillance, and command-and-control communication through both Tor and WebSockets. Once granted the necessary permissions, Brokewell can:
- Steal cryptocurrencies (BTC, ETH, USDT), IBANs, and wallet addresses
- Intercept SMS messages, including 2FA and banking texts
- Scrape data from Google Authenticator and email inboxes (Gmail, Outlook, Yahoo)
- Record audio and video, take screenshots, and stream the camera feed
- Log keystrokes and clipboard content
- Overlay fake login screens for credential theft
- Control device actions like sending SMS, making calls, or uninstalling apps
It achieves this by using two native libraries and encrypted .dex payloads loaded via reflection, making detection and reverse-engineering significantly more difficult.
Meta's role
The campaign exploits Meta's Facebook Ads infrastructure, where bad actors run fraudulent promotions in dozens of languages. Previous campaigns targeting Windows users impersonated brands like Binance, Bitget, Metatrader, OKX, and even public figures like Donald Trump. Bitdefender's analysis shows these malicious ads are tailored to regional audiences with localized language, popular financial brands, and culturally specific visuals, increasing their success rate and evading suspicion.
Bitdefender
The Android branch of the campaign is more narrowly focused, with TradingView being the only impersonated brand so far. But given the attackers' past behavior and adaptive tactics, broader targeting is anticipated.
Meta, the operator of the Facebook platform, has not commented on how these ads bypassed its internal moderation systems. The continued abuse of its ad network for malware distribution raises serious concerns about the platform's security controls.
Bitdefender recommends that users avoid sideloading APKs from outside Google Play, and be skeptical when met with “free premium” offers on ads. Always verify URLs to ensure you're on an official project domain before downloading anything, and during installation, watch out for high-risk permission requests like for the Accessibility Service.






Meta/BigTech directly collecting your data & spying on you, for sale to any bidder, destroying your privacy, while serving you RAT spyware so others can spy on you, steal your data.
Two nasty peas in the same pod.